
While ad blockers can prevent most harmful links from loading, you should also take steps to protect yourself from malware to keep your data safe from hackers and scammers. But you can do this through using open-source encryption software such as Veracrypt. Using open-source means there’s far less chance of any security flaws or deliberate backdoors as the code is constantly reviewed by the community. There’s a fascinating thread on Reddit (not remotely safe for work) where dark web users share their stories. Some of the tales are enough to make you tape over your webcam and disable your router just in case.
How To Stay Safe On The Dark Web
Discover the dark website’s hidden layers, its uses, and how to navigate it safely while protecting your privacy. The terms Darknet, Deep Web, and Clear Net are often used interchangeably, but they refer to distinct parts of the internet, each serving different purposes and accessibility levels. You don’t have to become a cybersecurity expert to understand the mechanics of the Dark Web. The reality is that you won’t realize how extensive your personal data exposure is until you look at the hard data. Aura’s free Dark Web scanner can notify you if your personal information has been leaked to the Dark Web. Because this offering is so extensive and affordable, the Dark Web is the ideal breeding ground for criminals.
There are also privacy and anonymous browsers, which are designed to keep you safe on the regular ‘open’ web. For example, the Epic browser is programmed to always run in private mode, so it doesn’t store data about which sites you visit. It is based on Chromium, the open-source of Google chrome but the developers claim to have removed all Google tracking software and that the browser stops other companies from tracing you too.
Dark Web Tools And Services
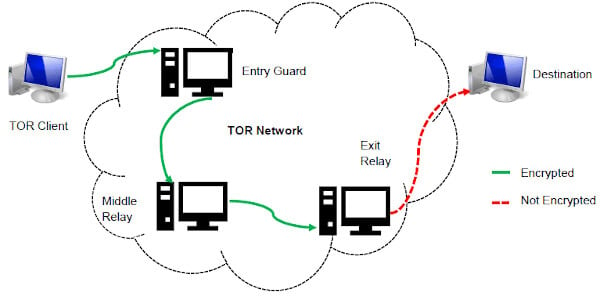
In the dark web, you can come across forums, markets, and hidden communities. These areas usually need specific darknet browsers such as Tor, which bounces the traffic through several layers or nodes to avoid the identification of IP addresses. ’ it is crucial to identify it as a two-sided phenomenon–a safe haven for legal proponents of privacy and a home for cybercriminals. The Dark Web differs from the Surface Web, which is the accessible and indexed part of the internet, in several ways. Users can access websites without revealing their identities, making it attractive to individuals who value privacy.
Risks Associated With The Dark Web

The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity. “Bitcoin has been a major factor in the growth of the dark web, and the dark web has been a big factor in the growth of bitcoin,” says Tiquet. All this activity, this vision of a bustling marketplace, might make you think that navigating the dark web is easy. The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others. The affiliates distribute the ransomware packages through the dark web.
Hacking Services And Data Breaches
The dark web is filled with information theft from malware-infected users. Attackers can use tools like keyloggers to gather your data, and they can infiltrate your system on any part of the web. Internet security software like Kaspersky Premium are comprehensive to cover both identity monitoring and antivirus defenses. The deep web is the next layer, and it encompasses a massive amount of online data that is not available for public consumption and not indexed by clear web search engines.
Cybersecurity Best Practices For Protecting Your Digital Assets
When people go on about the so-called dark web, they’re usually talking about onion sites, which aren’t searchable via Google or accessible via standard browsers. On the regular web, domains such as are translated into their actual IP addresses via the domain name system (DNS). Once you’re in, continue to use caution to protect your anonymity and safety. Don’t click on random links from strangers while browsing the dark web, and never give away any personal information.
What Is The Dark Web? Here’s Everything To Know Before You Access It
However, setting up or running a bridge like this requires additional software and configuration, which can be a barrier for less technical users. Tools like Norton 360 are critical on the dark web because they actively scan for and block threats — ensuring your device remains secure even in the dark web’s riskier environment. This added protection is vital, whether you’re using the dark web for privacy or out of curiosity. Additionally, a VPN like ExpressVPN masks your IP address before entering the Tor network, making it harder for your internet provider to detect Tor usage.
However, mobile phone carriers now offer extra security measures that can help protect you from SIM swapping attacks. Look online or contact your carrier to find out what you need to do to enable them. By encrypting communication before it gets to the Tor network, pairing Tor with a VPN gives a second degree of protection. Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity.

Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser. Locating surface web websites is possible because search engines can index the web via visible links (a process called “crawling” due to the search engine traveling the web like a spider). For over 40 years, PCMag has been a trusted authority on technology, delivering independent, labs-based reviews of the latest products and services. With expert analysis and practical solutions across consumer electronics, software, security, and more, PCMag helps consumers make informed buying decisions and get the most from their tech. From in-depth reviews to the latest news and how-to guides, PCMag is the go-to source for staying ahead in the digital world.
- Each warning for data leaks also includes the type of information exposed and the essential steps to limit your exposure.
- Tor relays are servers run by volunteers, designed to keep your activities private and untraceable.
- Keeper is the first and only password management application to be preloaded with mobile operators and device manufacturers including, AT&T, Orange, America Movil and HTC.
- DuckDuckGo runs on the Tor network and lets you search any part of the internet without tracking or storing your data.
- With the creation of Tor, users could now browse the internet completely anonymously and explore sites that were deemed part of the “dark web.”
Report any unauthorized accounts and ask the credit bureaus to remove fraudulent items from your credit report. Consider placing a credit freeze if you suspect foul play, as doing so prevents anyone from opening new accounts or taking out loans in your name. Read on to learn more about the dark web and how to protect yourself from fraud if your data turns up there. The news he’s broken has been covered by outlets like the BBC, The Verge, Slate, Gizmodo, Engadget, TechCrunch, Digital Trends, ZDNet, The Next Web, and Techmeme.
How To Access The Dark Web?
However, the same anonymity also facilitates illegal activities, including data breaches and unauthorized sales. Businesses are encouraged to conduct regular cybersecurity risk assessments to prevent their data from being traded on the dark web. Understanding how this hidden corner of the Internet works matters more than ever. Journalists, security professionals and everyday users alike rely on its anonymity tools to safeguard whistleblowers, protect sensitive research and evade censorship.
Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. Dark web encryption allows website owners and users to stay completely anonymous during their engagement.



