Websites on the surface web are publicly accessible and indexed by search engines such as Google and...
Pharmaceutical companies also see growingdemand for these super generics, leading to investment and ramping productioncapabilities. As patient...
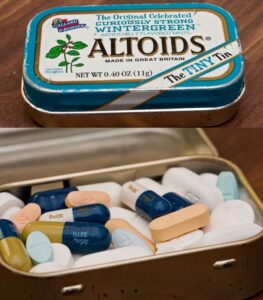
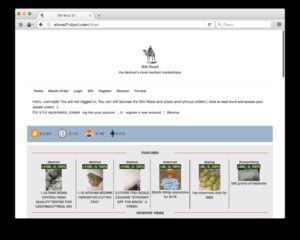
Silk Road was the first dark market of its kind, and it’s best known for the buying...
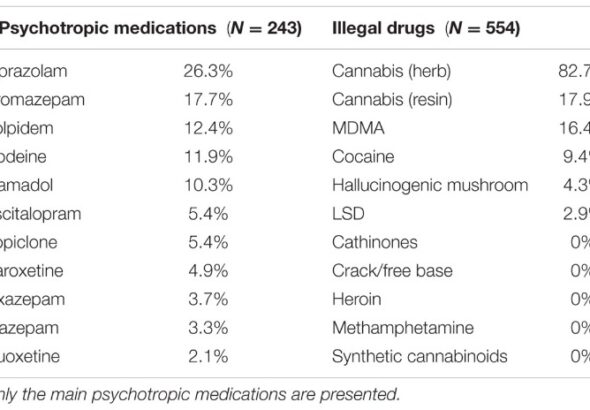
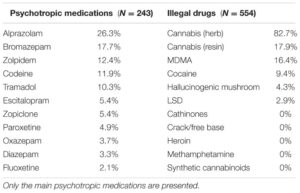
Opiate usage is widespread in some areas, although it is significantly less common than cannabis use. Compared...
It is also reliant on the level of internet access in different regions. As large platforms face...
The same report showed that cyberattacks on the healthcare industry grew by 86% in 2022 compared to...
LegitScript specializes in risk and compliance for highly regulated industries including CBD/cannabis, online gambling, cryptocurrencies, drugs, financial...
The same report showed that cyberattacks on the healthcare industry grew by 86% in 2022 compared to...
Seizing the assets and proceeds of these criminal enterprises not only hampers their ability to continue operating...
We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe...