
Torch illustrates exactly why searching for onion sites doesn’t always deliver the results you expect. For instance, using Torch to search for “Facebook” doesn’t return the Facebook onion site (which you can find here). Rather, it returns a list of posts looking for advice on how to hack Facebook accounts, where to buy stolen Facebook accounts, and so on.

FAQs On The Best Dark Web Search Engines
Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
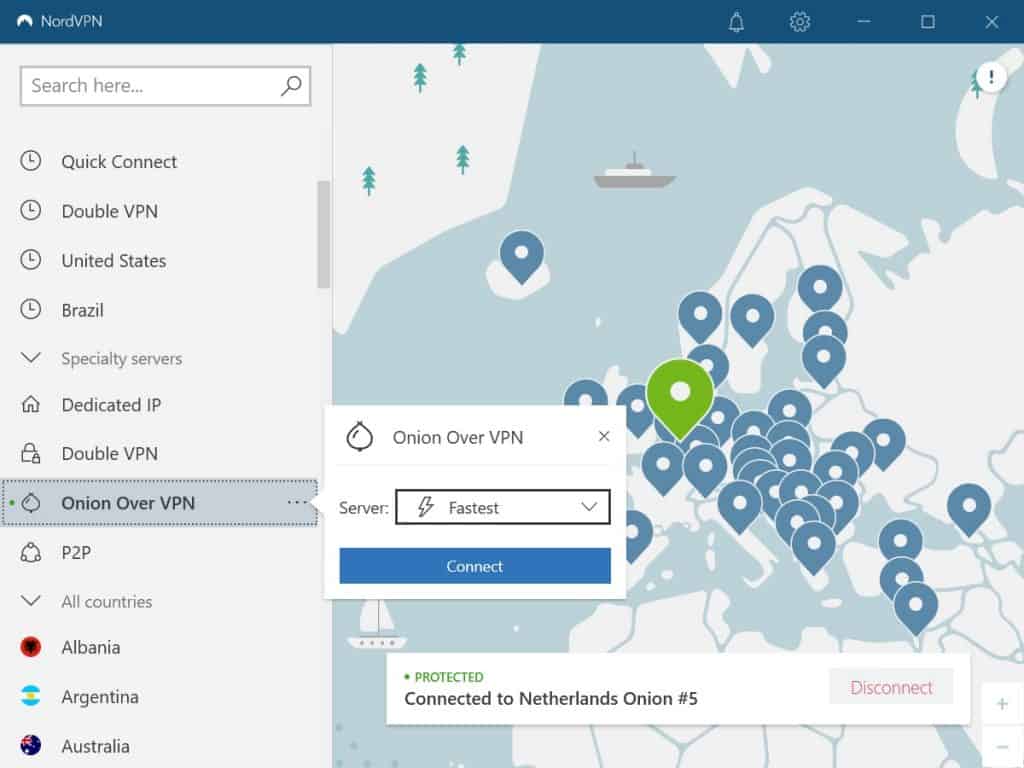
When using Tor without a VPN, each volunteer-operated node that your traffic passes through can potentially see some of your data. While Tor anonymizes your location, the exit node—the final point before your data reaches its destination—can view unencrypted information, such as the websites you’re visiting or data you’re transmitting. This means that, without additional protection like a VPN, your privacy is not fully secure. ExpressVPN adds an essential layer of encryption, ensuring that even if a Tor node intercepts your traffic, it cannot access your sensitive information, keeping you safer as you browse anonymously.
Is It Illegal To Use The Tor Browser?

Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. If you are in a position to report the incident safely, you should report it to the authorities immediately. It’s recommended not to be too vigilant here and leave the investigation to the professionals.
However, this feature is only available on iOS, Android, and Windows. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online.
Enhancing Your Security
Owing to its large search library, Torch is probably the best search engine for exploring the dark web. A familiar interface and fast loading speeds are the icing on the cake. While other dark web browsers (like Brave) can support onion links, the Tor Browser is highly recommended because it’s preconfigured with security and anonymity features optimized for the dark web. Check out our onion directory to explore standout hidden services and find new picks added by members of the onion community. In this guide, we’ll review the top Tor search engines right now, explaining what each one is best at, its advantages, and potential downsides. If you’re interested in exploring Tor for privacy-focused browsing or accessing hard-to-find resources, these search engines are invaluable tools.
How To Access onion Sites (Also Known As Tor Hidden Services)
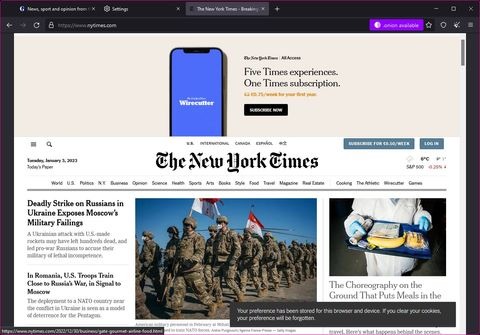
To access .onion websites securely, you’ll need the Tor Browser, a privacy-focused tool designed specifically for anonymous browsing. Here’s a straightforward guide to help beginners get started safely and efficiently. Navigating .onion sites requires the Tor Browser, specifically designed for privacy and accessing the dark web. Follow these straightforward steps to set up Tor and begin searching safely. Viruses, ransomware, and other types of malware are more common on onion sites than on the normal internet. Many pages have poor encryption standards and no other protections, so simply visiting a Tor site can infect your device.

Understanding Risks And Staying Safe On The Dark Web
You can access encrypted email services through the onion site without getting tracked. DuckDuckGo is a reputable US-based software company, so their Tor site itself is safe to use. That said, you still might get malicious links in your search results, so you still need to proceed with caution with any page DuckDuckGo takes you to. Unlike the surface web, where pages are easily searchable, dark web sites use encryption to hide their IP (Internet Protocol) addresses. Due to law enforcement takedowns and security reasons, .onion addresses are frequently rotated. As a result, the dark web has become a breeding ground for illicit activities because government agencies face significant challenges in identifying the operators behind hidden services.
However, these search engines serve as an entry to the internet’s underbelly. They index everything on the dark web, meaning you can find anything from whistleblower forums and privacy-centric blogs to illicit marketplaces, data leak repositories, and cybercrime hubs. These sites are often unlisted, constantly rotating, or intentionally fragmented, making them a breeding ground for cybercriminals, and dark web search engines are one of the easiest ways to find them. Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship.
- Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin.
- We’ve also looked at how Tor allows users to access the dark web, and we’re now aware of the resources and dangers that await us there.
- A VPN’s ability to hide your Tor usage from your ISP and from government authorities makes for a valuable addition to your online privacy arsenal.
- Read on to find out how to search for onion sites on the Tor network—and how to stay safe while doing so.
- Website addresses that end in “.onion” aren’t like normal domain names, and you can’t access them with a normal web browser.
Stay Safe
It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. While the iOS solution is not an official one, the Tor Project links to it, providing the browser its tacit approval. We’ve found that Tor is an excellent way to keep your internet browser-based online activities undercover, although we’ve also seen how using the Tor Browser can bring unwanted attention. If you find that Tor is restricted in your current location, you can use a bridge. A bridge creates an obfuscated relay on the Tor network that is not listed in the main directory. That means that even if an ISP is monitoring all of the known Tor relays, they may not be able to block all of the obfuscated bridges.
Since regular search engines don’t index .onion sites, finding what you need on the dark web can be tricky. That’s where dark web search engines come in — they help you discover hidden websites and make navigating this part of the internet easier. In this guide, you’ll find the top 9 dark web search engines, complete with .onion links. Each one offers unique features, such as better privacy and extensive .onion site indexing. While the surface web is easily accessible, the Dark Web offers anonymity, uncensored content, and resources that are hidden from traditional search engines like Google or Bing. But accessing this hidden part of the internet safely requires reliable Dark Web search engines — tools that help you explore the darknet without compromising your identity or security.
Websites you visit via Tor will see the IP address of the exit node, not your actual IP, just like websites see the IP address of your remote server when using a VPN. Onion sites are hosted on the Tor network, enabling them to share information without revealing users’ IP addresses. They facilitate secure communication over the web and protect from third-party surveillance. Regular browsers can’t open Onion sites because they aren’t part of the standard domain name system.
Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy. Yes, you can access the dark web on mobile — you just need the right app. Android users need to download the Tor Browser app, while iPhone fans should get the Onion Browser app. Users can ask questions, share answers, and engage in discussions without revealing their identities.
Activists, whistle blowers, and journalists also use the dark web to communicate securely with sources and news organizations. These domain names are not registered with a central authority but are instead derived from cryptographic keys. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?).
Discover Tor Links
In some cases, they even require JavaScript activation or specific browser settings that are only supported through Tor or other compatible dark web browsers. The basic architecture of a standard web crawler, such as those used by Google, relies on indexing from seed URLs, analyzing metadata, and following link structures. This process doesn’t work on the dark and deep web, where most sites are not interlinked. Plus, many .onion websites are created to be temporary or invite-only, so they may not even be active long enough to be indexed. These forums are frequently accessed via the top 10 dark web search engines, serving as essential resources for information and networking. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on.
Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. However, there are some significant variances in the background despite the similarities.



