More recently, Gmail users can turn on 2-Step Verification on their accounts to add an extra layer of security. Each file on our download page is accompanied by a file labelled “signature” with the same name as the package and the extension “.asc”. The Tor Project offers Tor Browser for macOS, Windows, and Linux, as well as Android. From a macOS or Windows desktop, navigate via web browser to the Tor Browser download page and select the version for your operating system.
How To Use Private Browsing In Safari On IPhone, IPad & Mac
When it comes to accessing the dark web (and safely), selecting a good dark web browser is critical. We recommend that you use only the Tor browser to access the deep, dark web, if you must. Don’t be fooled into going to a malicious clone site that is designed to extract your information. The correct top dark web browser download isn’t enough when it comes to safely accessing the dark web.
Accessing On IPhone (iOS)
You can install it on any USB stick that has at least 8 GB of space. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. This type of government surveillance applies mostly to countries with environments that are hostile to free speech.

In Belarus, during the 2020 protests against President Alexander Lukashenko, the government imposed internet restrictions. In response, Tor usage surged by over 300%, as people relied on it to access uncensored news and communicate with the outside world. The state’s claim to protect the vulnerable often masks efforts to exert control.
Best Dark Web Sites: Unseen Onion And Tor Links
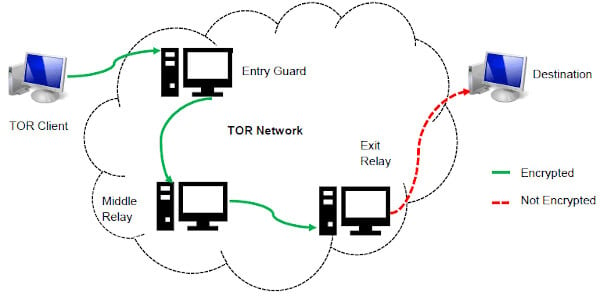
The dark web is a dangerous place, and all bets are off on your safety. As I mentioned previously, using the Tor Browser will slow down your browsing. Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down. This means Tor is a lousy option for streaming video, online gaming, or downloading files (torrenting).
How To Block Websites On Google Chrome

This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing. One option is to try DuckDuckGo’s .onion version, which is great for privacy.
Is The Dark Web Actually Anonymous?
Knowing where online materials are – and who is searching for them – makes it possible for search engines like Google to sell advertisements. This accounts for well over 80 percent of the company’s revenue, linking people who are searching with the millions of sites out there that pay Google to list their content. Next, select a dark web search engine like DuckDuckGo that can help you find dark web websites that cannot be indexed by traditional surface web search engines, such as Google or Bing.
The Tor browser can conceal your true location by shunting your traffic through various relays. But it can’t stop you from entering personal information on websites to say where you are. Your connection also may be encrypted but if you do something like send an email from your personal account, then anyone with access to your inbox will know that you were online at that time. The term ‘deep web’ doesn’t mean anything nefarious – it’s estimated to make up about 99% of the entire web. It refers to the unindexed web databases and other content that search engines can’t crawl through and catalog.

Why Use Tor For Accessing The Dark Web?
Tor is widely used in countries with strict internet censorship to access information that is otherwise blocked. For example, in China, where the “Great Firewall” restricts access to major platforms like Google, Facebook, and YouTube, people use Tor to bypass these restrictions. This technical design has immediate social consequences, which were apparent to the NRL designers from the early stages. Navy, for if this were the case, then only people who trusted the U.S.
- Internet service providers may also be suspicious of Tor usage and might monitor traffic patterns, even if they cannot see the content of the encrypted communications.
- Due to its absolute anonymity for knowledgeable users, the chance of running into bad people is also realistic, as they can operate relatively freely without the fear of getting caught doing something unlawful.
- Deep web content includes anything behind a paywall or requires sign-in credentials.
- It has features to maximize your privacy, unlike standard web browsers that have less stringent privacy protections.
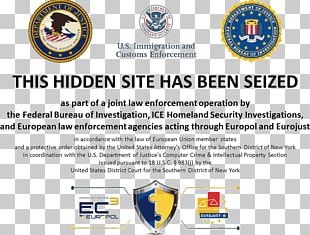
DNS provides organization with an opportunity to intercept malware before it contacts its command and control infrastructure. DNS visibility enables organizations to see other indicators of compromise such as spikes in IP traffic and DNS hijacking. Whistleblowers, human rights activists, journalists, military, and law enforcement all have a presence. Victims of domestic abuse use the Dark Web to communicate without being tracked by their abusers. There’s a lot of talk about the dark web these days, including how cybercriminals use it to spread malware, sell stolen data and publish user account credentials. Downloading tainted files or clicking suspicious links can install malware on your device, so be cautious when surfing the web.
In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy. It is the dark web’s version of Wikipedia with a massive links directory. You will find all the necessary .onion links to access any content or service on the dark web. If you choose to visit the dark web, you must take the necessary measures to protect your privacy and security. This includes using an anonymous browser like Tor, a VPN to encrypt your connection, an antivirus for protection against malware (we recommend TotalAV), and generally being careful not to reveal personal information.
Download Tor
Plus, there are only a few VPN providers that offer this option (PrivateVPN is the only one that comes to mind). VPN Over Tor is when you first connect to the Tor network and then connect to your VPN. While the Tor Browser does an excellent job of protecting your privacy and anonymity, you really shouldn’t use it as your daily driver browser.