Embrace these strategies to confidently navigate the Dark Web, preserving your privacy and security in an ever-evolving digital landscape. Ruheni Mathenge specializes in writing long-form content dedicated to helping individuals and businesses navigate and understand the constantly evolving online security and web freedom worlds. His articles have appeared in many respected technology publications. Ruheni explains complicated technical concepts clearly and simply.
History Of Dark Web Marketplaces
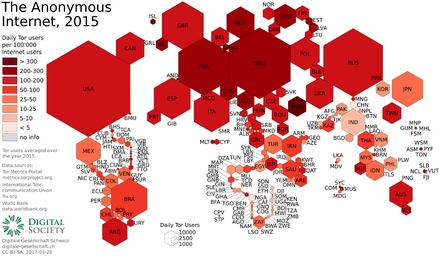
Tor, short for The Onion Router, is open-source software that routes Internet traffic through a global network of relays. This process hides the user’s location and enhances protection against surveillance and traffic analysis. This guide provides essential information on accessing the darknet safely and responsibly. Please read through the sections below to gain a better understanding. People mostly use it for covert communication, anonymous tips submission, and stuff like that. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node.
Meet LockBit 50: Faster ESXi Drive Encryption, Better At Evading Detection
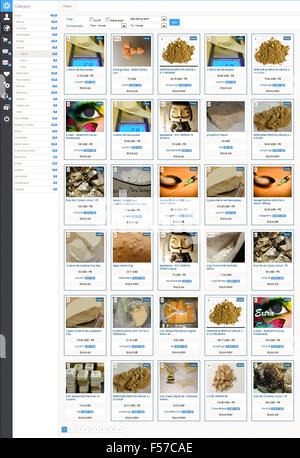
He recommends verifying market employees carefully, and to weed out law enforcement infiltration through barium meal tests. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs. However, the technology that Yippy manages, was created in Carnegie Mellon.
Bitcoin Wallets
Simply accessing the dark web and using the Tor browser may already raise government suspicion. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web.
Use Secure Communications
Information and data can be published and exchanged with the greatest possible anonymity on the so-called darknet, as PCWorld first noted in 2013. A curated collection of darknet resources for educational purposes, offering insights into darknet frameworks, tools, and security practices. By keeping these tips in mind and maintaining cautious online behavior, you can safely navigate the depths of the Tor network while ensuring your anonymity. Always stay aware of evolving threats and continue educating yourself about best practices for online privacy. If you need to communicate securely, utilize encrypted email services like ProtonMail or secure messaging apps, such as Signal or Session, rather than traditional messaging platforms that may compromise your privacy. Keep in mind that while Tor anonymizes your browsing activity, it is not foolproof.
Levels Of Security
It’s a modified Firefox that allows access to the dark web and is configured for higher security. When considering anonymous browsing, Tor isn’t the only option available. VPNs, proxies, and alternative privacy-focused networks like I2P and Freenet also offer unique advantages. Understanding the strengths and limitations of each solution helps you select the best tool for your specific needs.
- Other options include Ahmia and NotEvil, which focus on listing .onion links.
- Chances are you can find it at the Imperial Library, one of the most popular sites on the dark web.
- At this level, only features necessary for static websites and basic services are enabled.
- Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites.
- To expand their reach, some marketplaces established parallel channels on Telegram.
- They were also the first to host a .onion site to make their content accessible to everyone everywhere, regardless of censorship or anti-journalist laws in certain countries.
Best Tor Sites Available On The Dark Web – Quick List
This repository and its contributors are not liable for any misuse of the provided information. When using the Tor network, avoid accessing your regular browser or any site that could link back to your real identity. Mixing these activities can jeopardize your anonymity and expose your personal information. A pivotal moment in the history of the dark web came in 2002 with the introduction of Tor (The Onion Router). Naval Research Laboratory, Tor utilized layered encryption to shield sources and destinations of internet traffic.
Most legitimate vendors on the dark web will exclusively accept cryptocurrency for this reason. When people go on about the so-called dark web, they’re usually talking about onion sites, which aren’t searchable via Google or accessible via standard browsers. On the regular web, domains such as are translated into their actual IP addresses via the domain name system (DNS). Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser.
SecureDrop is a site that protects the privacy of journalists and whistleblowers. SecureDrop is a dark web link that allows whistleblowers on the dark web to communicate and share information with journalists safely and without being tracked. Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see.
These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy. It will offer you an additional layer of encryption to access the deep parts of the internet. Check out these best onion sites to access the dark web securely and anonymously. Founded around 1999 by activists in Seattle, it has since grown to over six million users worldwide.
It’s divided into commercial links (from crypto services to gambling sites) and non-commercial links (like social media). As always, use Tor Links with care, as it includes onion links to dubious or illegal activity. Users should never share any personal information, such as their real name, email address, or any details that could potentially link their dark web activities to their real-world identity. This includes avoiding logging into any personal accounts (social media, email, banking, etc.) while using Tor Browser.
Commercial Services
Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too.