A VPN protects your connection against everyone, not just your ISP and the authorities. This process also prevents your ISP from seeing your data or where it’s going. Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.
It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. If you only want to mask your IP address and don’t need to access the dark web, then going online with a VPN is much easier and faster than using Tor. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?).
How To Stay Safe On The Dark Web
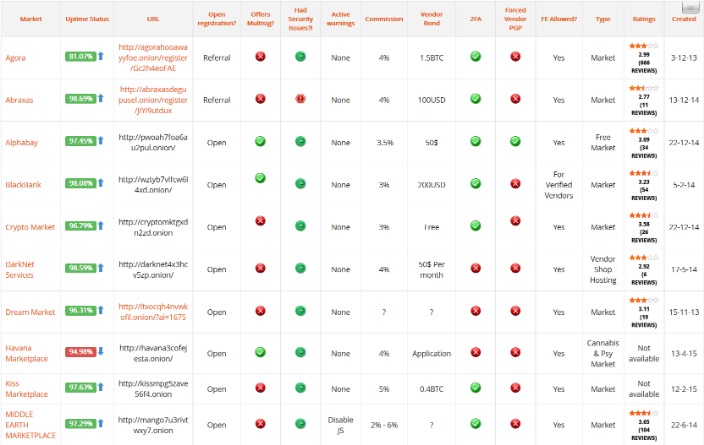
That means you may violate copyright laws while downloading books, so use a VPN to protect yourself from any legal repercussions if you have a dire need to use it. The Comic Book Library is the home for all your comic book needs. You can access thousands of issues, from the most popular to the most niche. It is one of the best sites on the dark web to find your favorite comics. The platform utilizes end-to-end encryption, ensuring it does not store any activity records. Like other email clients on the dark web, it does not require you to give your personal information. mark it means it has been verified as a scam service and it should be avoided. While browsing online, you might have noticed that the websites you are visiting have URLs starting …|This double encryption also protects against compromised Tor entry nodes that could potentially monitor your activity. While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites.|This is high-level protection; no one can intercept your data or activities. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too.|ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely.}
Does The CIA Have An Onion Site?

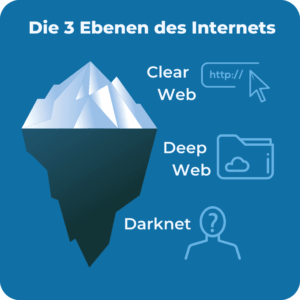
Many mainstream media organizations monitor whistleblower sites looking for news. Many dark websites are set up by scammers, who constantly move around to avoid the wrath of their victims. Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web.
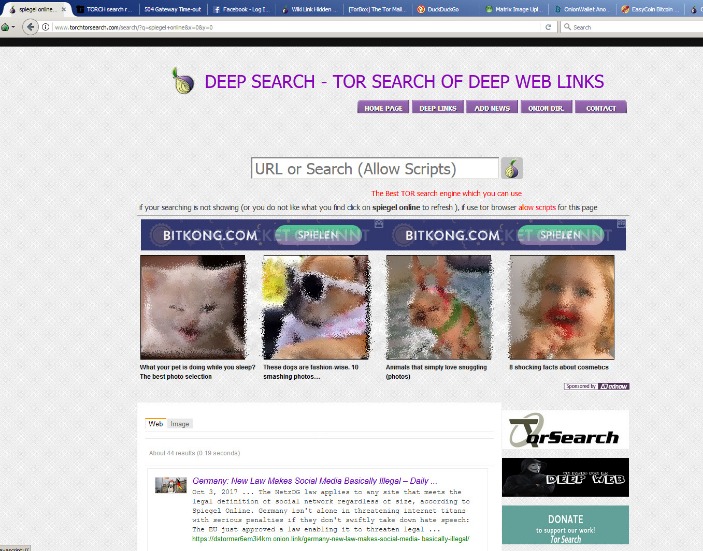
However, most are outdated and have not kept up with the changing landscape. For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want.
Onionname
As we stated earlier, the Hidden Wiki is an unreliable platform. The biggest and most frustrating part about dark websites is that they live for a short span of time. These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
Welchen Browser Benötige Ich, Um Onion-Links Zu Öffnen?

This means you have to know someone who is already using the platform. Even without the code, you can visit the security section to get tips on improving your daily life privacy. ProtonMail is a Swiss-based email service that is very easy to use. You are not required to provide your personal information to create an account.
Your safety on the dark web depends more on cautious browsing habits than any single security tool. While a VPN adds valuable protection, being selective about which sites you visit and never sharing personal information are equally important. Stick to verified dark web directories and legitimate services to minimize your exposure to risks. Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses. The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private.
Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Site operators can also submit their own .onion sites for indexing.
Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites. BlackCloud offers encrypted file storage specifically optimized for the Tor network. The service emphasizes privacy with zero-knowledge encryption and no registration requirements. My tests showed reliable performance for smaller files, but larger transfers can be slow due to Tor’s limitations.

You can also use it on the surface web, but it is still unadvisable without proper safety measures. It has a vast library of over 1.5 billion indexed pages that lets you find whatever you are looking for. However, the threat of clicking on the wrong link always remains, so be cautious while you use it. Just like Facebook, this is no random namesake; it is a legitimate platform from which to reach the CIA anonymously. You can even apply for jobs and request information, among other things. People like spies or whistleblowers often contact the CIA via the dark web to keep themselves hidden.
Tips To Stay Safe When Using The Dark Web
Other options include Ahmia and NotEvil, which focus on listing .onion links. Hence, you never know when a popular .onion site is going to vanish, or even die. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though).
Mit Dem Tor Browser Surfen: Die Beliebtesten Seiten Im Darknet
The dark web news site Deep.Dot.Web teems with stories of buyers who have been arrested or jailed for attempted purchases. These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”. For most people and use cases, using only a VPN will offer sufficient privacy with much faster speeds than Tor alone. A VPN provides strong security for everyday browsing without the extra delays, middle checkpoint, and then finally the exit gate.
ProPublica – Investigativer Journalismus Auf Tor
Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage. This isolates any potential malware and prevents cross-contamination with your personal data. Using Tails OS can further security, as all your data is reset every time you close the device. Always run the latest version of the Tor Browser to protect against security vulnerabilities.
- If you find a link that is not working let us know on our contact page.
- This means your activities cannot be traced or your browser history exposed.
- You only need to upload your PGP key or let the platform create one.
- For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.
Was Ist WPA2 (Wi-Fi Protected Access ?
NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. A reliable, fast, and user-friendly VPN service offering lots of customizable options for privacy geeks.
- It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications.
- Check out these best onion sites to access the dark web securely and anonymously.
- Even completing a transaction is no guarantee that the goods will arrive.
- However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities.
- So don’t be surprised if you encounter different versions that claim to be genuine, and be very careful.
Was Sind Onion-Webseiten?
The email service is available both on the surface and on the dark web. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem.