This means that the servers providing these services are only accessible via Tor and do not have a public IP address or domain name. Hidden services can operate while keeping the physical location of the server hidden, which makes tracking and shutting them down considerably more challenging. The dark web is content that exists on dark nets, which require specialized software (like the Tor Browser), configurations and authorization to access. These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be shared only with certain parties. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites.
BBC Tor Mirror
Such data includes medical records, financial information, research papers, private forums and networks, and other content. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here.
How To Access The Dark Web
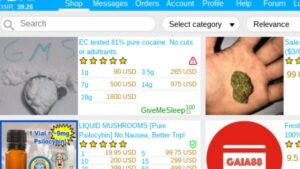
Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. It offers outstanding privacy features and there is currently a discounted rate available through this link. As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019.
- The platform is also used by governmental cyber departments to identify and track potential criminals or offenders.
- So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web.
- Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
- Therefore, the legality of the dark web will mainly depend on how you use it.
ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. Today, many organizations exist that are created only to handle these reports anonymously and effectively.
Use A Dedicated Browsing Machine

So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). It’s the last part of an internet domain name, stated after the last dot. For example, Google.com and PixelPrivacy.com both belong to the “.com” top-level domain. Google considers the majority of the content on the entire web highly irrelevant and useless to its users. That’s why such a large percentage (as much as 94%) of the entire web is not returned in Google Search.
Cryptocurrency Transactions

Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks. Darknets also serve as a platform for whistleblowers and privacy advocates. Platforms like SecureDrop enable individuals to submit documents and communicate securely with journalists, thereby exposing corruption and wrongdoings while preserving their anonymity.
Related Articles From The Safe Browsing Section
Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing.
These onion addresses will remain online even if the original page disappears. It also keeps the graphical copy and text of the page for better accuracy. SecMail is one of the most popular email services on the dark web. While this is not much compared to standard email services, it is enough for PGP-encrypted messages.
Onion Links: How To Access Them
One of the most well-known technologies enabling darknets is the Tor network, which was developed by the U.S. Naval Research Laboratory in the mid-1990s and later released to the public. Tor, short for “The Onion Router,” routes internet traffic through a global network of volunteer-operated servers to anonymize a user’s online activity. This technology initially had noble intentions, aiming to protect activists, whistleblowers, and individuals in repressive regimes. However, it soon became a double-edged sword as malicious actors began to exploit its capabilities for illicit purposes.
Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. This article lists some of the best dark web websites you can visit securely. Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. Sections of the dark web are often closed down too, as part of police operations. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges.
Cybercriminals use these platforms to traffic in stolen data, execute targeted ransomware attacks, and collaborate on advanced hacking techniques. Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc.
Is The Dark Web Illegal?
Keeper has millions of consumer customers and the business solution protects thousands of organizations worldwide. Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key.
- ZeroBin is a wonderful way to share the content you get from dark web resources.
- This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity.
- They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation.
- This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to.
- The website is available on the surface web and has a .onion site.
Government Surveillance
A network browser gives you access to sites with the ‘.onion’ registry operator. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser.