They may also modify the smart contract code to enable the scammer to send the token on behalf of other addresses, making it appear that those addresses initiated the transfer. TRM Labs identified about USD 9.04 billion being sent to various types of fraud schemes in 2022, with the large majority going to apparent Ponzi and/or pyramid schemes. Cryptocurrencies can also be used to influence voters during election campaigns.
Predicting And Prioritizing Cyber Attacks Using Threat Intelligence
Although gambling is legal and socially acceptable in many jurisdictions, it has long been a useful method of laundering funds from illicit activity. The gambling process involves customers paying money into a casino or bookmakers’ and later cashing out any winnings along with the remaining funds and an official receipt. This gives money launderers the opportunity to claim that their illicitly-obtained funds are merely gambling profits. Although blockchain forensics tools can assist with identifying the transactions that reach the VASP, investigators are required to apply for legal data access to obtain the necessary transaction data to identify the off-ramps. Flaws in smart contracts, a key component of DeFi that facilitate automation and transparency, provide attackers a seemingly endless supply of bugs to exploit. Two of the most significant ransomware syndicates in recent years have been LockBit and Conti.
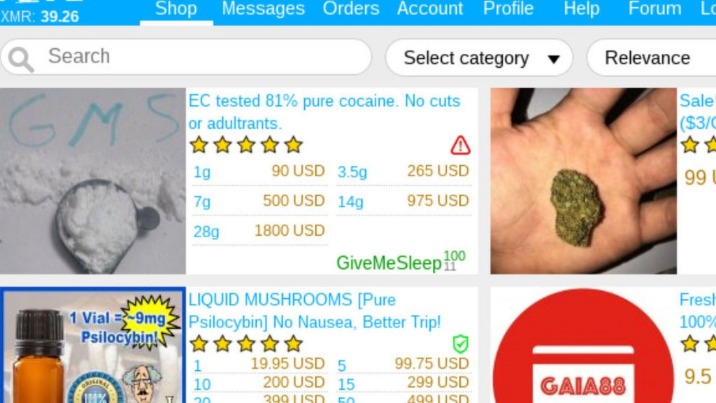
Early Warning Signals For Predicting Cryptomarket Vendor Success Using Dark Net Forum Networks
- All vendors must maintain product quality standards verified through customer feedback and random quality checks.
- Additionally, some criminals create fake marketplaces or deploy phishing links to harvest login credentials.
- By allowing users to create new addresses for every payment – or in some cases, reuse addresses for different actors – payment processors can make it more difficult for investigators to follow the flow of funds.
- Although gambling is legal and socially acceptable in many jurisdictions, it has long been a useful method of laundering funds from illicit activity.
- As a result, such OTC brokers are vulnerable to abuse by criminals seeking to cash out illegally-derived cryptocurrency.
It involves the scammer creating an address that resembles one to which the intended victim had previously sent funds. The scammer then sends a small amount of cryptocurrency to the target in the hope that they will unwittingly make a future payment to that scam address in place of their intended recipient. Crypto-related phishing attacks grew in prominence during the 2017 Initial Coin Offering (ICO) boom. Victims targeted in these phishing attacks would only lose the amount of cryptocurrency they sent to the wrong address in error. As NFTs entered the mainstream, attackers began to target novice NFT investors by exploiting the “FOMO” – fear of missing out – and hype surrounding the NFT world.

The Rise Of Crypto Fraud

These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private. Don’t ever reveal your true identity on the dark web marketplaces because there’s a high chance of hackers and scammers misusing it. Beware of sharing your financial details on the dark web, as this can result in identity theft and your bank account amount being stolen. Cybercriminals on the dark web marketplace always look for new victims to target them with scams or infect their devices with malware, spyware, or adware. Thus, use the best antivirus software that protects against these online threats.
Nation-state actors, too, leverage darknets for espionage and cyber warfare, capitalizing on the obscurity and untraceability they provide. Parasite VASPs rely on the architecture of a larger exchange to provide digital assets trading services to users, often without the knowledge or consent of the host exchange. Criminals and sanctioned individuals may use parasite VASPs to move their illicit proceeds through the crypto ecosystem to make the transactions appear legitimate. Parasite exchanges usually have weak to non-existent Know-Your-Customer (KYC) and AML requirements, which can make them a preferred vehicle of cybercriminals and money launderers for moving funds. They are distinct from independent single-vendor shops that also sell illicit drugs, and from other types of fraud stores.As much as USD 1.49 billion was spent on DNMs in 2022, according to TRM Labs research.
About TRM Labs
Two carding shops, Bypass and Ferum, were 4check’s biggest customers, having paid a total of USD 1.2 million each. They usually have their own websites and telegram bots, and can also work as built-in checkers within carding shops, by providing their API (application programming interface) to the carding shop. Unlike cybercrime forums or BPHS, CC checkers incur no fixed overhead expenses, which maximizes their profit margins. Indeed, one of the most recent darknet market busts was the Nemesis online market.
- In response to a rapidly changing cybersecurity landscape, criminals are expanding their toolkits by leveraging novel technologies.
- A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services.
- As a result of today’s action, all property and interests in property of the blocked person described above that are in the United States or in the possession or control of U.S. persons are blocked and must be reported to OFAC.
- It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any goods and services.
- Sanctioned Russian persons are known to employ a wide variety of measures in their efforts to evade U.S. and international sanctions.
- In that instance, the virtual asset service provider (VASP) involved in the transfer of the bitcoin to the would-be killer cooperated with authorities in providing details of the suspect.
How To Effectively Communicate Cyber Risk To The Board: Lessons From APRA Compliance
In the case shown above, a single exchange address received funds from 40 different cash-to-crypto services ATMs located all over North America. The same address was reported in multiple public reports and investigations as being used by scammers as an aggregator and off-ramp for stolen funds. In this case, the significant number of transfers from multiple cash-to-crypto service locations to the same address served as the trigger for investigators to identify the suspicious destination address. Money laundering amplifies the total amount of illicit activity in the ecosystem because all transactions made to try to launder funds are themselves illicit. It involves processing the criminally-derived funds in order to disguise their illicit origin.
Deepfake Attacks Hit Two-Thirds Of Businesses
It asks you to pay the merchant fee if you want to sell something, preventing the buyers from getting scammed. World Market is another largest dark web shops that deals with various goods and services. Its impressive anti-DDoS protection feature and easy-to-use interface make this marketplace stand out among the others. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. Sixth, we consider the cumulative mean interevent time for each entity i at time t, defined as the mean of the sequence of time interval between consecutive transactions of an entity until time t, which we denote by \(\phi _i(t)\). This feature is satisfied when \(\phi _i(t) \le \tau\), where \(\tau\) is the maximum value of mean interevent time.
Dark web users rely on a combination of tools and networks to maintain their anonymity. Tor (The Onion Router) remains the most popular, routing data through multiple encrypted layers to hide users’ real IP addresses. Some individuals and groups also leverage I2P, a peer-to-peer network designed for continuous routing within a decentralized environment. Beyond these specialized networks, users often connect through VPN services and proxy chains to further mask their physical locations. In 2022, Portugal became among the first countries to allow the sale of a house using crypto.
Q: What Advantages Does Cryptocurrency Offer On The Dark Web?
Frosties NFT was another NFT project that promised exclusive digital art and collectibles. However, shortly after the project’s launch the two 20-year-old creators shut down its website and Discord servers, removed the liquidity from the trading pool and disappeared with USD 1.1 million of investors’ funds. According to the DOJ complaint, the duo transferred the proceeds from the scheme to various cryptocurrency wallets under their control in multiple transactions designed to obfuscate the original source of funds. They were later arrested and charged with wire fraud and conspiracy to commit money laundering.
Cryptocurrency Transactions
Nevertheless, it is important to stress that the results are robust under considerable variation of the parameters, indicating that the coherent picture emerging from our analysis does not depend on the details of the method. Future work may further extend the approach presented here, for example using machine learning methods to capture further behavioral regularities. For example, in some cases, a seller in a given market may behave as a buyer in a second market or in the U2U network. This multi-role classification, to be implemented in future work, can help gain a more nuanced understanding of the ecosystem and the structure of the dark web supply chains.
With the USD 182 million, the attacker gained controlling ownership in the protocol providing the ability to influence votes. Code exploits target a project’s smart contract code and allow an attacker to remove funds from DeFi protocols without authorization. Code exploits are facilitated by coding mistakes and errors, such as unchecked external calls, access control issues, and logic bugs. Of the USD 1.4 billion stolen via code exploits in 2022, authentication issues, improper validation, and signature verification issues accounted for about 90% of the amount stolen. One example is the popular use of Maximal Extractable Value Bots (MEV Bots), which operate based on publicly available blockchain information. MEV Bots can have extremely high amounts of activity and have played a role in several large scale exploits, including Nomad.