It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers. Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025. In 2025, darknet markets have become highly sophisticated platforms for secure and reliable drug trade, offering users unparalleled privacy and efficiency. These platforms leverage advanced encryption technologies and decentralized systems to ensure that transactions remain confidential and untraceable.
Darknet Market Onion Links
Accessing blocked content can result in being placed on a watch list or imprisonment. Some services are genuine; you can get what you want at an agreed fee. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows.
Tips To Stay Safe When Using The Dark Web
A VPN allows a user to encrypt all internet traffic traveling to and from his or her device and route it through a server in a location of that user’s choosing. A VPN, in combination with Tor, further enhances the user’s security and anonymity. Tor is a network of volunteer relays through which the user’s internet connection is routed.
No user names are tied to actual identities, and no moderation like one may find on Reddit. Users leverage these platforms to organize protests, whistleblow, share survival guides, or share files P2P. Also, you can set a strong password to protect your message and choose how long it will take to expire. ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. It aims to advance research on terminal illnesses like cancer with access to unbiased scientific publications.

The History Of Darknet Marketplaces

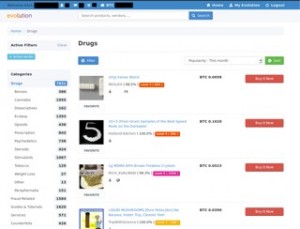
The best darknet markets in 2025 continue to evolve, offering improved user interfaces and expanded product listings. Darknet market lists and darkmarket urls help users navigate these platforms efficiently. The darknet drug market and dark web marketplaces remain popular for their reliability and diverse offerings.
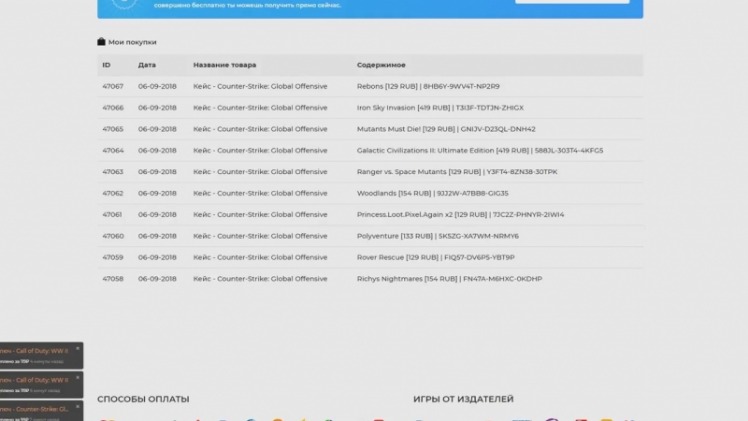
Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). Both MEGA and Hydra hidden services emphasize trusted vendor-buyer relationships before the market will facilitate the crypto-transaction and goods exchange. For example, on Hydra, before an order from the buyer is processed, the vendor and buyer must communicate and trust each other. The market even offers a “transaction chat” platform to communicate securely about the order. This approach theoretically reduces the likelihood of scamming and law enforcement operations.
Home Products

A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. You should never use your personal information on the dark web anywhere else in your life.
Darknet Markets Onion Address
Some of these sites are very helpful (but unseen as Google doesn’t show them), while others are just for fun. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. Today’s markets reflect a decade of evolution, balancing user demand with operational security against an ever-present cat-and-mouse game with authorities.
Set Up Tor Browser
- Please note that all material provided here is aimed at promoting awareness, responsible research, and ethical use of information.
- Remember that illegal activities can still incriminate you, whether you are using a Tor browser.
- And then there’s malware—click the wrong link or download the wrong file, and your device could get infected.
- This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity.
- OPSEC (Operational Security) involves following strict online practices to protect your identity.
You can find featured listings on the homepage and browse the products of your choice. There’s also a search bar that you can use to search for any particular product or vendor. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track.
Agentic AI-Powered, Intelligence-Driven Unified Cybersecurity Platform
As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. Many people overlook the importance of regularly changing the WiFi network password. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address.
Notes From The Dark Web: Analyzing Ukraine-Related Chatter In Key Forums

Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals.
The market is especially well-known for providing access to freshly compromised data, often obtained from recent breaches and stealer logs. The platform is favored by cybercriminals seeking access to accounts that can be exploited for fraud or sold to others. Here’s a look at the top 10 dark web markets currently dominating this underground space. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge.
- For safer browsing, it is highly recommended to also use a VPN and antivirus software.
- While browsing online, you might have noticed that the websites you are visiting have URLs starting …
- The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method.
- By following simple but effective OPSEC strategies, you can protect your identity, avoid scams, and reduce unnecessary risks.
- Besides, victims of crime may want to hide their identities from their perpetrators.
Russians On The Darknet Part II: Marketplaces & Forums

I2P uses one-way tunnels, so an eavesdropper can only capture outbound or inbound traffic, not both. Obviously, finding these .onion websites is the first challenge, as they won’t show up in Google search results. You can’t just Google “Silk Road” and hope to land on the dark website. Officially, the Tor Browser is only available on Windows, Mac, Android, and Linux. Many experts advise against using third-party mobile browsers that utilize the Tor Network. As long as users take the necessary precautions, no one knows who anyone else is in the real world.