Also, try its services risk-free with the 30-day money-back guarantee. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities.
TRM Talks: Hydra Takedown: A Discussion With Experts From US Treasury, Flashpoint And TRM Labs
The Russian darknet market conflict is a cyber conflict in the Russian darknet drug market, which began after the closure of the largest marketplace Hydra in April 2022. The struggle manifests itself in mutual cyber attacks of sites and an aggressive advertising campaign. The closure of Archetyp Market will likely trigger a temporary disruption in darknet drug supply chains, but it won’t end darknet drug trafficking altogether.
A 2014 study found that the most common type of content found on Tor, the most popular darknet, was child sexual abuse material. Darknets and dark markets present a multifaceted challenge to businesses and society as a whole. While these hidden networks can be used for legitimate purposes, they are equally significant as vectors for cybercrime and illicit activities. Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy. This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement. The use of digital signatures can also help verify the authenticity of users and transactions.
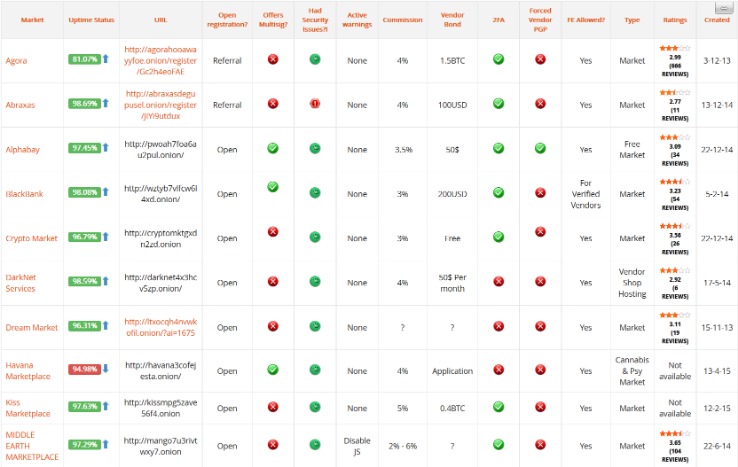
Further market diversification occurred in 2015, as did further developments around escrow and decentralization.
AI-Powered Cloud Security Platforms Set To Transform Enterprise Cyber Defense In 2025

Over time, ambitious individuals created infrastructure for these transactions, where for a fee, sellers have access to a digital ‘storefront’ to sell their products in a centralized marketplace. Given the darknet’s infrastructure, which is hidden behind onion routing, the darknet attracts sites whose proprietors want to remain anonymous. The most common darknet software is the free and open-source Tor, short for the Onion Router. The software was developed in the mid-1990s to protect U.S. intelligence communications online and is used in conjunction with virtual private networks (VPNs). Tor software, in conjunction with the user’s preferred VPN, conceals the user’s location and IP address and is implemented through layers of encryption, akin to the layers of an onion, from which the service derives its name. While some competing darknet softwares are similar to Tor browsers, they typically exist for different purposes.
Arrest And Trial Of Ross Ulbricht
Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Administrator and prolific vendor Gal Vallerius was arrested in August 2017. Disable JavaScript in Tor until you trust the site you’re visiting. Go to the security settings and set the security level to “Safest” to minimize potential vulnerabilities.
Trusted Directories And Forums (stay Away From Hidden Wiki)
The dismantling of Archetyp Market marks a significant milestone in the ongoing battle against darknet drug trafficking. This operation exemplifies how international collaboration, intelligence sharing, and advanced cyber-forensic techniques are essential in combating these hidden marketplaces. Unlike many dark web platforms that vanish quickly, Archetyp’s five-year longevity demonstrated the resilience and adaptability of darknet markets. However, this resilience also underscores the critical role of law enforcement in disrupting illegal economies that operate under layers of anonymity.
Agentic AI In Cybersecurity: Transforming Threat Detection And Defense
Therefore, if you do decide to explore it, exercise extreme caution. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged. You only need to upload your PGP key or let the platform create one. Use it to link your GitHub account, Twitter, Bitcoin address, and Facebook. This .onion link makes it impossible for hackers to impersonate your profile.
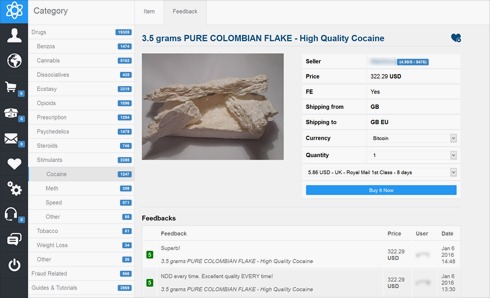
The Silk Road left a lasting legacy, influencing the emergence of numerous other darknet markets, and igniting ongoing debates surrounding privacy, ethics, and the regulation of online spaces. Dark markets are online platforms on the darknet where illegal goods and services are traded. You can find drugs, weapons, stolen data, and counterfeit documents on these marketplaces.
What Are Dark Markets?
A budget-friendly VPN service allowing users to access dark web safely anytime, anywhere, and on any number of devices they want. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there.
This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy.
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web.
Bitcoin Wallets
- Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed.
- The only difference is that it passes your traffic through random nodes before reaching the destination.
- Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web.
- Still, it’s a lot of work to take down a single forum, but it shows we can succeed if we have the right people in place and the resources to apply.
- The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
For example, concurrent with the takedown of Hydra was the sanctioning of Garantex, the Moscow-based exchange that made multiple transactions with Hydra-linked addresses. In the wake of recent headlines announcing actions against Hydra Marketplace by the U.S. and German governments, darknet markets have made an ironic entrance into the spotlight. It hosted over 7,000 .onion categorized links to make surfing the web easier. One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is online.
The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user.
Dark Web Email Services
Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. Archetyp’s use of Monero cryptocurrency highlights the challenges authorities face in tracking financial flows on the darknet. Monero’s privacy features make tracing transactions notoriously difficult, adding complexity to investigations. Yet, the successful seizure of infrastructure and key individuals proves that no system is invulnerable to coordinated, cross-border law enforcement efforts. One of the primary reasons whistleblowers choose to use Tor (The Onion Router) when sharing sensitive information is to protect their identity and enhance their online anonymity.