The platform’s design, which emphasises privacy and minimal regulation, has made it a favoured space for extremist groups. These groups exploit the app’s private channels to disseminate propaganda and recruit members, operating with reduced scrutiny compared to more regulated platforms. This use mirrors the dark web’s role in fostering extremist ideologies, providing a secure environment for the spread of harmful content and coordination of criminal activities.
14 Channel Promotion And Migration
- The agency, which manages pensions and insurance for millions, confirmed that hackers bypassed its security but did not identify those responsible.
- Telegram won’t ever compete with cybercriminal activity present on underground forums in terms of scale but it will continue to be used for the fraudulent activity discussed in the previous posts.
- This environment mirrors the dark web’s function, where anonymity and encryption allow users to engage in illicit activities with relative impunity.
- Despite these changes, many cybercrime-related Telegram channels remain active and influential.
- The queries here reflect a desire to expand networks and enhance social media presence rather than technical troubleshooting.Credential Compromise channels share a similar dynamic with Blackhat Resources, where queries are about the practical aspects of hacking tools.
- In Blackhat Resources channels, users frequently engage with the content by providing feedback on the effectiveness of various hacking tools.
Party drug prices are falling on the encrypted messaging app despite claims of record seizures by authorities, VICE News analysis shows. Like we wrote in previous Dark Web Pulse posts, there are many other cyber criminal groups who use Telegram, such as RansomHouse, Arvin Club, Lapsus , BlackShoadow, GhostSec, Moses Staff and more. As we wrote in previous Dark Web Pulse posts, many other cyber-criminal groups, such as RansomHouse, Arvin Club, Lapsus , BlackShoadow, GhostSec, Moses Staff, and more, use Telegram. Your account must be older than 4 days, and have more than 20 post and 10 comment karma to contribute. Please note that the site is automatically filled from open sources and does not store information about Telegram channels except for the name, description, link, and avatar.
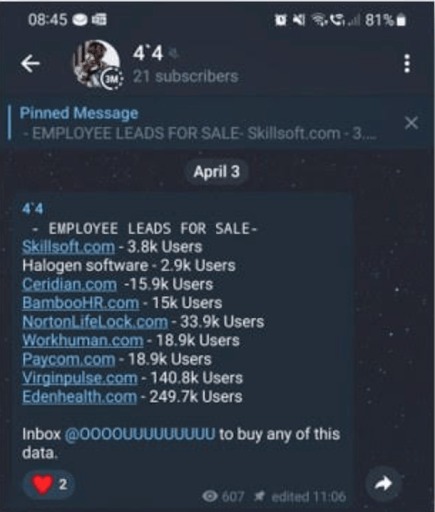
Data Leak Monitoring
Elliptic says that Haowang Guarantee’s owners also own a stake in another similar Telegram-based market called Tudou Guarantee, according to a Telegram post from one of Haowang’s administrators, and they may seek to rebuild their business there. Tudou Guarantee has already seen a significant surge in new users, Robinson says. When WIRED asked Telegram about Elliptic’s findings regarding both markets, the company responded with broad bans of Xinbi Guarantee and Haowang Guarantee accounts.
- These groups exploit the app’s private channels to disseminate propaganda and recruit members, operating with reduced scrutiny compared to more regulated platforms.
- As cybercriminals continue to exploit dark web markets, Telegram channels, and underground forums, organizations must take a proactive approach to identifying potential risks.
- Additionally, we’ll cover core similarities and key differences between each platform in order to better understand that not all cybercriminal based communities are created equally.
- The focus here is on enhancing visibility rather than acquiring specific tools or resources.
- It frequently shares updates about claimed attacks on public and private sector targets, including infrastructure, transportation, and government systems.
The Wiretap: At $24 Billion In Sales, The Biggest Illicit Marketplace Ever Is On Telegram
Telegram is a free, open-source, cloud-based instant messaging platform that has gained huge popularity as people want privacy-focused communications. Another moniker mentioned in coordination with SiegedSec is “Sryakarad“, often shortened to “Sry” in darknet chatter. Sryakarad was mentioned specifically as a key contributor to SiegedSec when the group leaked data from another online media firm they compromised in Pakistan, e-paper.pakistan. There have also been cases of cybercriminal groups using Telegram channels to promote their activity and build a following.
We also identified 42 posts offering Personally Identifiable Information (PII) through leaked account credentials for various email providers and online services, similar to those found in Credential Compromise channels discussed in Section 5.1. These credentials were often shared as attached text files (25), via external links for downloading (14), or with instructions to contact an external bot or user to obtain or purchase them (3). Additionally, 16 posts included ”proofs” such as screenshots or videos demonstrating successful logins or transactions, serving as evidence of the authenticity of the leaked credentials. Moreover, 11 posts contained warnings about potential risks and guided on avoiding detection by security systems, such as not using the same credentials across multiple IP addresses and avoiding access from known devices or networks to prevent tracking back to the user. Cybercriminals increasingly favor IM platforms like Telegram over traditional dark web forums and markets.

Premium Digital
We found that 5 channels were dedicated to a single TV show, posting episodes in a sequential format. For ongoing shows, new content was shared weekly.Additionally, it is crucial to highlight that distributing pirated media is a serious offense. Organizations and authorities actively ban such activities to protect intellectual property rights. Engaging in or facilitating the distribution of pirated content can lead to severe legal consequences, including fines and imprisonment. Beyond system exploitation tools, several tutorials focused on promoting social engineering tactics (other than phishing).
2 Malicious Files

The platform offers Live Traffic, delivering logs in real time, and Private Cloud, which provides up to 5,000 logs daily, amounting to 120,000 logs per month. Additionally, Omega Cloud maintains a database exceeding 2 billion records, accessible through a subscription-based model. A Telegram channel specializing in the distribution of credentials obtained from stealer logs. With 20,000 members, Moon Cloud shares a wide range of compromised data, including URLs, email addresses, IP addresses, passwords, and usernames. A widely recognized platform in the cybersecurity community, vx-underground is known for its extensive collection of malware samples, research papers, and cybersecurity insights.
You can send messages to loved ones and join a chat group or channel with people who share the same interests as you—like “Game of Thrones” or advanced algebra. But first impressions can be deceiving, and Telegram is not always what it seems. The aforementioned cyber threats are not just speculation — businesses have suffered from leaked sensitive data exposure on Telegram before. Here are some real examples of the most relevant data leaks appearing on Telegram. The dark web is a part of the internet that can only be accessed using specialist software and knowledge. Ever since the launch of the Silk Road marketplace in 2011, there has been a steady conveyor belt of websites selling illegal goods and services.
SiegedSec: A New Cyber Threat Actor Group
To receive notifications about new content, users on Telegram must follow (join) a specific channel. We tracked the growth of followers across all CACs in our database over the study period, yielding insights into their growth patterns. Collectively, the identified CACs are followed by approximately 23.8 million users, with a median of 8,000 followers per channel. Unfortunately, the Telegram API only allows channel administrators to view the list of followers, a limitation we faced.
The app has allowed people from all over the world to be able to share and collaborate more than ever before. However, it has also allowed numerous dark web forums and other nefarious groups to move onto the messaging app as well and create illicit channels successfully. Telegram, unlike some other messaging apps, provides end-to-end encrypted chats when a user selects the “Secret Chats” option in their settings. The content inside channels and groups is then encrypted between Telegram and its server, meaning ISPs can’t access any data.
The success of operations like DarkGram which led to the takedown of 196 illicit channels in just three months, shows what’s possible when threat intelligence is applied strategically. Threat actors typically use OTP bots for personal financial fraud rather than corporate. For example, if a data breach exposes corporate logins, a malicious actor could find those victims’ phone numbers through OSINT, then leverage that to solicit one-time passwords to bypass 2FA controls. Though threat actors can buy and sell infected devices on established autoshops, they can also be found on Telegram channels.
For years, a Chinese-language market for crypto scammers and money launderers—by some measures, the internet’s biggest black market of all time—operated in plain sight on the messaging service Telegram, facilitating tens of billions of dollars in illicit finance. Now, thanks to the scrutiny of one team of crypto crime researchers and Telegram’s ban hammer, it’s gone. Dark web Telegram merely refers to groups and channels that host illicit content—much of which originates from the dark web—or contain shady characters who want to steal your personal information or trick you into signing up for fake NFTs or crypto schemes. However, you don’t need a dark web internet browser like Tor to access this content.

These forums tend to view themselves as more professional than other cybercriminal communities, often shunning non-Russian speakers and those perceived as unskilled or inexperienced. These sites act as a network for career cybercriminals to connect with potential collaborators. For example, they are used by Initial Access Brokers to auction access to organization’s infrastructure and by Ransomware-as-a-Service (RaaS) operators as a PR channel. Russian nationals Roman Vitalyevich Ostapenko, Alexander Evgenievich Oleynik and Anton Vyachlavovich Tarasov have been indicted for allegedly operating cryptocurrency mixing service Blender.io and its successor Sinbad.io. The services were designed to help cybercriminals hide their crypto transactions and required little to no personal details for users to sign up, the Justice Department reported.
On Wednesday, the BBC learned that while Telegram does respond to some takedown requests from police and charities, it is not participating in programmes aimed to proactively prevent the spread of images and videos of child sexual abuse. The arrest of Telegram’s billionaire chief executive in France has ignited a debate about moderation on his app. About nine months ago while researching a story, I found myself added to a large Telegram channel which was focused on selling drugs. Watch our cyber team share their key insights from their investigations into the biggest dark web trends in 2022.