
The extent of the problem became clear in 2015, when the FBI shut down a dark web site on Tor named Playpen that hosted 23,000 sexually explicit images of minors. Not all mass thefts of data facilitated by the dark web have been motivated by money. The publicizing of Snowden’s actions led to a global spike of interest in Tor and a resulting rapid expansion of the network’s user base. As we all know, websites on the surface web end with common suffixes such as .com, .org, .edu, and .gov. When browsing through Tor on the dark web, however, the suffix is .onion. It’s fitting because Tor itself stands for The Onion Router, a reference to the multilayered (like an onion’s skin) encryption it uses to keep users anonymous.
What Is The Dark Web? The Good And Bad Of The Internet’s Most Private Corner
- At the same time, Tor became an effective shield for the illicit sale of heavily controlled goods, such as guns and drugs.
- It uses a technology called “onion routing,” which protects users from surveillance and tracking through a random path of encrypted servers.
- This helps support our work, but does not affect what we cover or how, and it does not affect the price you pay.
- The affiliates distribute the ransomware packages through the dark web.
- Platforms like SecureDrop even allow journalists to receive tips anonymously.
From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI. The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers.
How To Access The Dark Web?

Individuals can scan the dark web or sign up for a monitoring service. For over 40 years, PCMag has been a trusted authority on technology, delivering independent, labs-based reviews of the latest products and services. With expert analysis and practical solutions across consumer electronics, software, security, and more, PCMag helps consumers make informed buying decisions and get the most from their tech. From in-depth reviews to the latest news and how-to guides, PCMag is the go-to source for staying ahead in the digital world.
You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. While the Dark Web hosts illegal activities, it also supports legitimate uses like protecting free speech and aiding cybersecurity. A person must exercise caution while accessing the Dark Web, while being mindful of legal obligations and possessing an ethical perspective. The debate about how best to balance technology regulation against anonymous benefits will transform as science advances.
How To Access The Dark Web: Step-by-Step Tutorial (and A Few Words Of Caution)
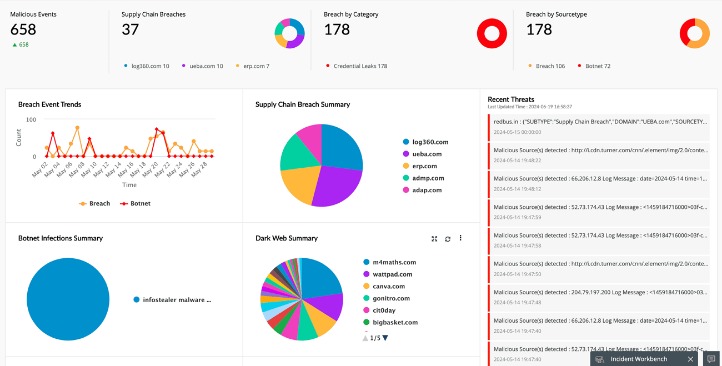
Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks. The dark web is dangerous due to the presence of scams, malware, and illegal material. The use of tight security measures, dedicated hardware, and awareness are required to prevent these threats. Additionally, SentinelOne can identify sensitive data and assets within your organization, leveraging its AI-powered threat intelligence to prevent potential data breaches. You can apply automated actions to control and secure access to sensitive data.
Drug Trafficking Sites
However, there are also some perfectly reasonable and legitimate uses too. Journalists and activists often use the dark web to communicate securely with sources and work around censorship imposed upon them by tyrannical regimes. Ken Colburn is the founder and CEO of Data Doctors Computer Services, datadoctors.com. Ask any tech question at facebook.com/DataDoctors or on X @TheDataDoc. You cannot stop breaches from happening, but good digital hygiene helps limit the damage and stay ahead of cybercriminals. In today’s digital era, where information is constantly on the move across all digital platforms, an…
BUSINESS BROADBAND GUIDES
However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. It allows you to search for images, maps, files, videos, social media posts, and more.
Dark Web Statistics For 2025: Key Trends And Threats
In darknet mode, you can select friends on the network and only connect and share dark web content with them. This enables individuals to form groups and only share content in a highly anonymous network of darknet users who they know. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces.
All ISO publications and materials are protected by copyright and are subject to the user’s acceptance of ISO’s conditions of copyright. As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators. But let’s be realistic, the best defence isn’t just playing detective after the fact. It’s making sure your sensitive information never lands there in the first place.

The dark web is a domain that provides anonymity to site owners and guests so they cannot be monitored by outsiders. Although many people use the two terms interchangeably, they are two different layers of the internet. On the other hand, it hosts illegal activities like black markets for drugs, weapons, and stolen data.
Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading. I agree to receive information, tips, and offers about Tech Research Online products and services. One of the major advantages of the Dark Web is the maintenance of “Privacy and anonymity”. Journalists, activists and others use the Dark Web to communicate safely and anonymously to avoid censorship.
To Browse The Dark Web, You Need A Dark Web Browser
If you’re on the dark web to engage in illegal activity and your traffic passes through a compromised exit node, your secrets can be exposed. The “onion routing” technology underpinning the dark web was developed by researchers at the U.S. Initially designed for secure military communications, it evolved into a broader tool for online anonymity, later expanding to public use with the Tor network. The dark web’s anonymity accommodates illegal activity and contributes to its reputation as being a haven for criminals. This anonymity, coupled with access difficulties and a high barrier to entry, facilitates all manner of illicit activities such as drug and human trafficking, weapons deals, and money laundering. However, the cloak of anonymity also attracted those seeking to engage in criminal activities.
Myth 1: The Dark Web Is Only Used For Illegal Activities
To strengthen your organization’s cybersecurity posture and protect against emerging threats, consider exploring our comprehensive dark web monitoring and security assessment services at Cybernod. One of the most concerning aspects of the dark web is the prevalence of illegal activities. Users may inadvertently encounter illicit content, such as child exploitation materials, counterfeit documents, or illegal drug marketplaces. Even browsing such content, intentionally or not, can have severe legal ramifications in many jurisdictions. While the deep web includes legitimate, unindexed content such as private databases and subscription-only platforms, the dark web specifically facilitates anonymity. This feature has given rise to misconceptions, such as the assumption that all dark web activities are criminal, overshadowing its legitimate uses.
With top-of-the-line encryption and excellent speeds, you can browse safe in the knowledge that NordVPN will keep you safe without slowing you down. On top of this, NordVPN offers cyber threat protection, combating any cyber nasties you might come across. The dark web is a small, hidden corner of the deep web that requires special software to access, and that’s where things can get dubious. The best analogy I have heard is to think of the internet as an iceberg. Beneath the surface lies the “deep web,” which includes information not publicly searchable, such as online banking portals, paywalled content and internal company databases.


