Regularly monitoring your credit card statements can help you detect any suspicious activity, such as unauthorized transactions....
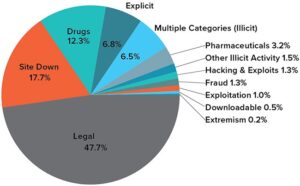
websites
Moreoever, the servers are owned by the organizations that use the service. There are several ways to...
The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires...
The group provided bulletproof hosting (BPH) services to the cybercriminals that breached health insurer Medibank Private. “BPH...
One common tactic among scammers is URL spoofing — creating .onion addresses that look almost identical to...
The darknet is primarily used to communicate unrecognized on the internet. Anonymization services prevent your own internet...
These sites utilize layers of encryption to provide anonymity to both users and site operators. The dark...
Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously)...
However, these search engines serve as an entry to the internet’s underbelly. They index everything on the...
Information in the listings was entered into a spreadsheet for data analysis and statistical calculations. B1ack’s Stash,...