Look for vendors with high ratings and positive feedback, and be wary of new or untested vendors....
This further complicates monitoring efforts because now you need to search for the related Telegram channels and...
Many experts advise against using third-party mobile browsers that utilize the Tor Network. Tor is a network...
It marks the most significant JCODE operation to date, building on years of enforcement actions and marketplace...
Then there’s crypto—Monero’s the quiet kid who doesn’t spill secrets, unlike Bitcoin’s chatty ledger. Tor2door blends old-school...
Akasha says he caught Joules’ eyes from across the lawn, trying to silently signal to her with...
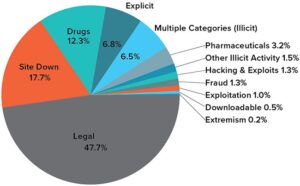
By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing...
In most cases, the vendors also have deposited large amounts for the vendor accounts. This is returned...
Use a separate email address and cryptocurrency wallet exclusively for marketplace activities to maintain proper operational security....
Keybase also offers extremely user-friendly secure chat and file-sharing services through its app. The process costs a...