Instead, these tools rely heavily on manual submissions, curated lists, and user reports. John Awa-Abuon is a seasoned technology writer with a passion for making tech accessible to everyone. His articles have appeared in many respected technology publications.
Use Active Monitoring Of Financial And Identity Theft

It is available for Windows, macOS, Linux, and Android, offering a user-friendly interface and seamless integration with the Tor network. Unlike traditional websites with fixed IP addresses, hidden services have no single point of failure or central server. Instead, they utilize a distributed network of servers, known as Tor nodes, to maintain their operations and protect against censorship or shutdowns. This decentralized nature allows hidden services to remain online and accessible even if some Tor nodes are compromised or taken down. Welcome to the dark side of the internet— the intriguing and mysterious realm known as the Dark Web.
The Legality Of Accessing The Dark Web

Lastly, maintaining discretion is vital when engaging in transactions on the dark web. Avoid discussing your purchases or revealing sensitive information, such as delivery addresses, on public forums or in unsecure communication channels. Minimize the risk of your personal information being exposed and exercise caution at all times.
Dark Web Websites: How To Access Them Safely
This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.
Hence, if you participate in them, whether knowingly or unknowingly, you can end up putting criminal charges on yourself, and in some extreme cases, even imprisonment. The website has an advanced search filter and an easy-to-use interface, which makes it easy to find what someone is looking for. You can also use it within the dark web, as it has .onion links. It will offer you an additional layer of encryption to access the deep parts of the internet. You can choose the best darknet (.onion) website that suits you and start surfing. For safer browsing, it is highly recommended to also use a VPN and antivirus software.

What Should I Do If I Suspect I’ve Encountered Illegal Content On The Dark Web?
Avoid clicking on suspicious links or downloading unknown files. Stick to reputable sources and communities to reduce the risk of encountering malicious actors or falling victim to scams. Accessing the Dark Web is significantly different from browsing the regular internet. It requires specific tools and precautions to ensure privacy and security. In this section, we will explore the steps you need to take to access the Dark Web safely. In the next sections, we will delve deeper into the steps required to access the Dark Web, find popular marketplaces, and protect yourself from potential risks.
BBC Tor Mirror
Ensure that the provider does not keep logs of your online activities, as this can potentially compromise your privacy. Look for VPNs that have a strict no-logs policy, meaning they do not collect or store any information regarding your internet usage or IP address. One well-known marketplace on the Dark Web is “The Silk Road,” which gained notoriety as the first major online marketplace for drugs. It operated from 2011 to 2013 and provided a platform for users to purchase various narcotics using Bitcoin.
How To Access The Dark Web
For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings.
You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity.
Community Forums
Never install extensions or additional add-ons, even if they seem useful. They change your browser fingerprint and make you easier to track. Setting up Tor correctly is critical if you want to browse the dark web without exposing your real identity.

How Do I Find onion Websites Safely?
For over 40 years, PCMag has been a trusted authority on technology, delivering independent, labs-based reviews of the latest products and services. From in-depth reviews to the latest news and how-to guides, PCMag is the go-to source for staying ahead in the digital world. Always use an abundance of caution when interacting with anything or anyone on the dark web. It hosted over 7,000 .onion categorized links to make surfing the web easier.
However, always be diligent in assessing the credibility, reputation, and reviews of vendors before engaging in any transactions. The first step is to use a trustworthy virtual private network (VPN). A VPN creates an encrypted connection between your device and the internet, masking your IP address and location.
Other Ways To Access Dark Web Platforms
This ensures that your internet traffic is well-protected and secure from unauthorized access. Additionally, features like a kill switch can automatically disconnect your internet connection if the VPN connection drops, preventing your real IP address from being exposed. Once you have a reliable VPN, the next step is to download and install the Tor browser. The Tor browser is specially designed to access the Dark Web and provides an extra layer of privacy and security by routing your internet traffic through a network of encrypted relays.
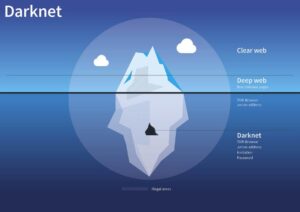
- Designed to be hidden from conventional search engines like Google or Bing, the dark web is a portion of the internet.
- Use secure payment methods, such as cryptocurrencies like Bitcoin, which offer an additional layer of privacy.
- This adds another layer of anonymity to the Dark Web, as it becomes extremely difficult for anyone to trace the origin or location of a hidden service.
- In some cases, it’s also used for private messaging, cybersecurity training, whistleblowing, and other legitimate uses.
- This page may contain sensitive or adult content that’s not for everyone.
In this section, we will discuss important factors to keep in mind when engaging in transactions on the dark web. The first and most important rule is to exercise caution and skepticism. Be wary of offers that seem too good to be true, as they often are. Scammers frequently lure unsuspecting individuals with enticing deals or promises of rare goods or services. Trust your instincts and always verify the legitimacy of a seller or marketplace before proceeding with any transactions.
Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. The anonymity provided by onion routing comes at the cost of slowing your internet considerably. As such, we do not recommend using Tor if you want to do data-intensive activities like streaming in HD, gaming, torrenting, or making video calls. It works by sending internet traffic through volunteer-operated nodes all over the world.
Opt for curated sources like Dark.Fail (PGP-verified mirrors) and Ahmia (filters abuse). Treat Hidden Wiki with caution and verify any link via multiple sources. Fake sites are everywhere, and even a one-character difference in the URL can land you on a phishing page. That is important for those who may fear persecution for their actions or live in areas where access to information is regulated.