So, if the website looks fishy, close the tab, and forget about it. Well, now it’s time to fire up Tails and do a little bit of tinkering. Note that the process can take anywhere from 5 to 30 minutes depending on your machine. Now, if you want to see what lurks in the dark corners of the Internet but don’t really trust Tor, there are alternatives. When using this method, Tor will encrypt your request, which will pass through your ISP unhindered. From there, it will go through a VPN server that conceals your IP and wipes geo-locations tags and other elements your Government or ISP might use to track the request.
Does Tor Browser Hide Your IP And How?
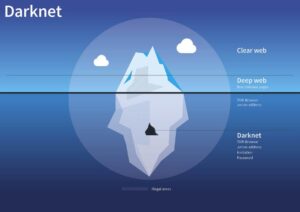
It is a part of cyberspace that is not indexed in conventional search engines such as Google or Bing. This means that for safely access the Deep Web specific tools and procedures are required. Even with Tor and onion routing in place though, you’re not suddenly completely invisible and free to do whatever you want, without repercussions. Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for.

Don’t Stick Your Nose Where It Doesn’t Belong
In addition, Tor and VPNs take different approaches to rerouting data. A VPN sends your web traffic to a server, which transmits it to the internet. Tor’s onion routing method reroutes your data through a series of independent nodes. Though Tor is slower, the process of rerouting data through nodes makes it more difficult to trace your activity back to you. Simply put, onion routing is how Tor works, and how dark web websites can be browsed without anyone except you knowing. But fortunately, knowing how to use Tor Browser doesn’t require a PhD in computer science — it’s surprisingly easy and user-friendly.
Is Tor Browser Free?
In this setup, the VPN connection acts as a middle layer between your device and Tor, routing your internet traffic through the VPN before it reaches the Tor network. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers.
- While it is not always possible to discover directly a specific web server’s content so that it may be indexed, a site potentially can be accessed indirectly (due to computer vulnerabilities).
- It’s somewhere Google and Bing don’t index, and you need special tools to get to it.
- Each router (or node) then “peels away” a layer of encryption until the data reaches its final destination, fully decrypted.
- Put simply, there’s a lot more secrecy than the already secret act of using Tor to visit a website on the open internet – for both parties.
- The Tor browser is able to access the special domain names, with the suffix .onion, used in the dark web.
One of the challenges of exploring the dark web is that you can’t just use a search engine and type in what you’re after like you would on the surface web. Instead, you often have to consult directories to find lists of legitimate sites and visit and access them that way or use special dark web-friendly search engines. The dark web has many legitimate use purposes and contains legitimate content, including dark web mirrors of popular websites and services such as BBC News and Facebook.
However, remember to be cautious when accessing this hidden part of the internet. For added protection, it’s best to use a VPN like ExpressVPN to encrypt your internet traffic and mask your IP address while establishing the initial Tor connection. A proxy server acts as an intermediary between you and host services, while Tor is an encrypted network of decentralized servers. While proxies replace your IP address and location, they don’t encrypt internet traffic, meaning your data is still exposed in transit.
Tor routes your traffic through a chain of relays to obscure your IP address. This makes it harder for websites, ISPs, or surveillance tools to see who you are or what you’re doing. Many sites on the dark web are scams, and some host illegal content. Tor over VPN also doesn’t protect users from malicious Tor exit nodes. Because Tor nodes are made up of volunteers, not all of them play by the rules.
These nodes/relays and the websites operating on them make up the Tor network, or as it is more generally named, the dark web. I2P is a private network built for secure, anonymous communication. Instead of the onion routing Tor uses, I2P relies on unidirectional tunnels and garlic routing, which bundles multiple messages together for better traffic obfuscation. It uses its own internal DNS to access “eepsites”, not .onion addresses.
Content Types
Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. Navigating the Tor network isn’t easy as search engines do not index .onion sites. Therefore, you need to use sites like the Hidden Wiki to find out the specific web addresses. Over 96% of the internet lies beneath the surface web, hidden from regular search engines like Google or Bing. For IT managers, cybersecurity experts, and tech enthusiasts, understanding the deep web is essential—not just for curiosity but for data access, research, and privacy.
Avoid Logging Into Personal Accounts
The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous. Read on to learn the pros and cons of the dark web, how to access it, and get tips for staying safe. Then, install Norton 360 Deluxe to get AI-powered scam detection to help secure your browsing against online threats.

As such, you should exercise caution when accessing any unofficial dark websites. The Tor network was created by the US military in the 1990s for anonymous communication between spies over the internet. That effort was never fully realized, but the US military published the code under a free license in 2004. Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers. Alternatively, users can connect in opennet mode, which automatically assigns peers on the network. Unlike darknet mode, opennet uses a handful of centralized servers in addition to the decentralized peer-to-peer network.
Tips On How To Use The Tor Browser Safely
The browser is available on Windows, macOS, Linux, and Android. There is no official Tor version for iOS because Apple requires all iOS browsers to use WebKit, which affects Tor’s privacy features. Copy your desired onion URL and paste it into the address bar at the top of the screen to begin searching on the dark web. Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website. This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously.
All your traffic is automatically routed through the Tor Network. Ensure you download the Tor Browser from the official website to avoid downloading malware, spyware, or other viruses to your device. The dark web, or dark net, is a small part of the deep web that is kept hidden on purpose. Websites and data on the dark web do typically require a special tool to access. You could certainly go much deeper into the topic, but we hope the information provided here has given you a basic understanding of what the deep web/dark web are, how they function and why they exist. More importantly, you should now know how to access these hidden sectors of the internet at your leisure.
It is much less populated – but the population is generally more technically savvy. You also have to watch out for scams and fraud – there is no regulation – so keep your wits about you. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security.
Using Proton VPN
This means always updating your device’s OS, having a working firewall, and a reliable antivirus system. The settings are accessed by clicking the shield button next to the address bar and choosing Advanced Security Settings. The names of dark web pages are unusual, too, and can make it difficult to find them.

Can A VPN And Tor Make The Dark Web Completely Private And Secure?
It has features to maximize your privacy, unlike standard web browsers that have less stringent privacy protections. However, using Tor has some challenges that you should be prepared for. The dark web refers to websites that are not on the regular internet but are instead hidden in a private network that is only accessible using specialized web browsers, such as the Tor Browser. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous.