Some examples include Mozilla Monitor (free) and Mozilla Monitor Plus (paid). Award-winning identity theft protection with AI-powered digital security tools, 24/7 White Glove support, and more. Darknet markets facilitate transactions for illegal goods and services. Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources.
You can either sell or buy goods on the dark web, but both present difficulties. The dark web is also a place for scammers to attract vulnerable and unwitting victims. The platform is also used by governmental cyber departments to identify and track potential criminals or offenders. You can never be sure who’s really behind the other end of the line. In opennet mode, the network will automatically assign you to other users on Freenet’s network.
Look For Warning Signs That Your Device Has Been Hacked
Similarly, the Onion Browser also has 3 security levels — Gold, Silver, and Bronze. The Bronze level maintains the lowest security, allowing scripts and access to videos and your microphone by default. The Silver level restricts access to your microphone and other features but permits JavaScript, while the Gold level severely limits all access and scripts. Open the Orbot app and click the Start button to use a secure tunnel to connect to the Tor network. Once connected, you should be redirected to the browser’s homepage.
Update Security Questions And Recovery Information
Next, we will discuss the importance of monitoring your credit and identity to stay proactive in the face of potential repercussions from having your phone number on the Dark Web. Many people are unaware of how their personal information, such as phone numbers, can end up on the Dark Web. It may seem like a mysterious and overwhelming issue, but it’s important to understand the implications and take proactive steps to protect yourself. With over 15 years of experience in content creation and digital publishing, he knows how to craft informative, useful content, with thorough research and fact-checking to back it up. He strives to make complex cybersecurity topics accessible and understandable to the broadest audiences. In his spare time, Michael likes writing fiction, reading murder mystery novels, and spending time with his family.
Apps & Products
This guide should serve as a comprehensive roadmap for Android users interested in exploring the dark web. With Forest VPN’s robust security features and the anonymity provided by Tor, the hidden corners of the internet become accessible without compromising safety. It’s not really dangerous if we consider the protection of a VPN service. Generally speaking, most websites are legal and they’re safe to use.
Popular Dark Web Search Engines And Sites
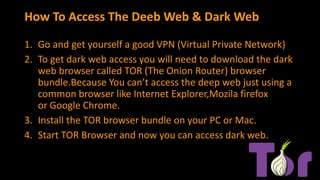
You’re probably mistaken if you think accessing the dark web on your phone is as easy as simply typing or “log in” to “dark web,”. To access the dark web, you need particular browsers, dark web search engines, and a reliable VPN provider. In general, using the dark web comes with significant risks, including malware, phishing scams, identity theft, and more. It’s crucial to take precautions to protect yourself and your data.

Best Dark Web News Sites Offering Factual Information
Tor is like the public-facing door to the dark web, and there are even mobile apps for Android and iOS. Backlinko turns AI SEO into clear, actionable strategies with step-by-step frameworks and examples to help you rank in an AI-driven search world. We’re still obsessed with bringing you world-class SEO insights, backed by hands-on experience. Unless otherwise noted, this content was written by either an employee or paid contractor of Semrush Inc. They troll through the non-surface level of the Internet to determine if your information has been compromised.
- You must be aware of your region’s legal and political policies when using Tor.
- Your mySocialSecurity account will show your benefits (if you have applied for them) and other helpful information.
- Navigating the Dark Web requires a certain level of vigilance and discretion.
- The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily.
- While some experts suggest placing a fraud alert on your account, it may not be enough to prevent fraud.
How Dark Web Report Works
Remember, some credit card companies offer this service for free if you have an account with them, so contact your credit card company to see if they offer credit monitoring. Dedicated identity theft protection services monitor your credit reports, bank accounts, SSNs and other sensitive information, and alert you to potential fraud. Even if you’ve taken the necessary steps to secure your accounts, it’s a good idea to set up ongoing dark web monitoring. Many identity protection services offer real-time alerts if your information appears on the Dark Web in the future. Within the Dark Web, various illegal activities take place, including the sale of drugs, weapons, stolen data, and other illicit goods and services. It serves as a marketplace for criminals and individuals seeking to engage in illegal activities without detection.

Should You Use A VPN With Tor?

So, you should be aware of your actions and adhere to local laws to avoid engaging in illegal activities. That said, accessing the Dark Web isn’t challenging and only requires a few apps to do so. A private search engine that doesn’t track your search queries and records data can help prevent tracking. Moreover, to limit the chances of tracking and data being shared, you need to turn off your location services on your device while accessing the dark web. Also, ensure that the dark web browser cannot access your contacts, phone, settings, or other important features.
It’s also worth noting that while the Dark Web can provide an additional layer of anonymity, it is not foolproof. Law enforcement agencies, with the help of cybersecurity experts, have successfully tracked down individuals involved in illegal activities on the Dark Web. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers. There are several email and IM services which you can use, and it’s highly recommended to pick one if you want to step up your dark web game.
As of 2025, Google offers residents of eligible countries with a consumer Google account a “Dark Web Report” feature. This feature monitors the information you add to your monitoring profile across known data breaches and Dark Web sites. Your personal information is all over the internet — whether you like it or not. Tor routes your traffic through a chain of relays to obscure your IP address. This makes it harder for websites, ISPs, or surveillance tools to see who you are or what you’re doing. Many sites on the dark web are scams, and some host illegal content.
Is It Safe To Access The Dark Web On An IPhone?
Aura’s Dark Web scanner and HaveIBeenPwned are both reliable free options to check whether your sensitive information is on the Dark Web. Have you ever encountered a breach of your digital privacy, and how did you navigate the aftermath? It offers outstanding privacy features and there is currently a discounted rate available through this link. By using a VPN you can hide these details and protect your privacy.
The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you. But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network. So, to get into the Tor network, follow the steps I’ve listed below.
However, it should serve as a wake-up call to take immediate action to protect yourself and prevent further harm. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. As well as phishing scams, a multitude of other scams operate across the dark web. There are many fake marketplaces and platforms that might offer to sell you goods or services but actually take your money without providing anything in return.
Despite their reach, no dark web scanner can cover all the stolen data that exists across the entire dark web as a result of criminal activity. However, if you suspect your personal information has been compromised, a dark web scan can be a great resource to help ease your mind. Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web. It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages.
Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used. Mary, I’m sorry to hear that your identity was being sold on the dark web. I’m glad you contacted the credit reporting agencies to alert them and place alerts on your credit report.