Even when using security measures and your common sense, accessing deep web content still poses a risk. Antivirus will ensure that any viruses or malware downloaded from the dark web are removed. Tor is a network of volunteer relays through which the user’s internet connection is routed.
A Beginner’s Guide To Tor: How To Navigate The Underground Internet
- Tor browser is a freeware that is available for Windows, macOS, Linux, and Android, and it can be downloaded from the official Tor Project website.
- Without a doubt, there are a bunch of places in this bizarre grove of the web that people should avoid at all costs.
- Once we have the browser correctly installed, when we open the application, we will be asked whether we want to join the Tor network or surface the Web without it.
- The platform is also used by governmental cyber departments to identify and track potential criminals or offenders.
- The impact of such breaches extends beyond financial loss, as it can erode trust and damage reputations.
- Then, simply click the operating system that you are using and download the file.
If the default engine is not available in the list of search engines, you can add it by clicking the ‘Find more search engines’ option. This means the connection to the guard node is established and you are free to use the browser. Changes to the Tor browser will only take effect after connecting to the Tor network, so don’t click the ‘Tor Network Settings’ option. Let’s start with downloading the Tor browser for Windows from the official website. Tor browser is developed by a non-profit organization called ‘Tor Project’ to make communications safer and anonymous and to fight surveillance and censorship. By following these guidelines, you can have a safer and more fulfilling dark web experience while leveraging the privacy-focused search capabilities of DuckDuckGo.
Can My ISP See That I Am Accessing The Dark Web?
The dark web is a known haven for the distribution of malware, viruses, ransomware, and keyloggers, which can severely compromise a user’s device and personal data. Similarly, engaging in financial transactions or making purchases on the dark web is generally discouraged due to the high risk of scams and potential legal ramifications. Most legitimate vendors on the dark web will exclusively accept cryptocurrency for this reason. Yes, we recommend that you always use a VPN if you’re accessing the dark web on your phone. The dark web is packed with potentially harmful content that puts you at risk, so a VPN is an important tool in keeping your identity and personal information safe. Therefore, it’s best to use a VPN no matter the personal device you’re using.
However, stepping into this part of the internet without preparation can expose you to risks. Once you are connected to the TOR network, you can start browsing the dark web by entering .onion URLs into the address bar of the TOR browser. You can find .onion URLs by searching for dark web directories and forums on the clear web. Accessing it without proper protection exposes you to surveillance, tracking, and potential security risks. If you need to access the dark web, NymVPN can add an essential layer of privacy and anonymity, encrypting your connection before you even access the Tor network.
How Tor Has The Answer To Secure Browsing

The company enforces a strict no-logs policy and is based in Switzerland, which has some of the world’s strongest privacy laws. For the highest level of security, use Tails OS (The Amnesic Incognito Live System) on a bootable USB drive. Tails is a live operating system that runs independently of your regular OS and leaves no trace.
This feature offers a more direct and potentially more trustworthy way to find the onion versions of legitimate websites. While there are several search engines available for exploring the dark web, such as Tor2Web and Grams, one popular choice is DuckDuckGo, a search engine known for its privacy-focused approach. If you connect to your VPN and fire up Tor Browser, you’re using Tor over VPN. All your device’s internet traffic first goes to the VPN server, then bounces through the Tor Network before ending up at its final destination.
Is Tor Enough, Or Do I Also Need A VPN?
Contact us today to learn more about how Brandefense’s dark web monitoring service can help you protect your business and achieve peace of mind. The dark web is known to host illegal and disturbing types of pornography, including child exploitation and violent content. Some dark websites offer hacking services, such as password cracking and DDoS attacks, for a fee. That’s why at TecnetOne, we don’t just collect data—we use smart technology and expert analysts to separate what matters from what doesn’t.
Some reports say the FBI will simply label you a “criminal” once they’re aware you’re using the Tor browser. The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you.
I2P – The Invisible Internet
- For most people this will not be a problem, but if it is, you can easily find forums online teaching you to implement a configuration.
- Tor Browser masks your IP address and routes traffic through multiple servers.
- Yes, you definitely need a VPN if you want to access the dark web on your phone.
- One of the most significant dangers is the high likelihood of encountering malware, ransomware, and other forms of malicious software.
- Please also bear in mind that there is no official version of Tor for iOS at this time.
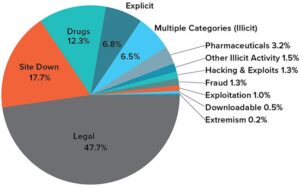
Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries. Did you know that Google only shows you a glimpse of all the websites that actually exist? The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search.
Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites.
FAQs On Accessing The Dark Web Safely
But that’s not all — there is a free plan that comes as a supplementary offer. All users who create a new Webshare account automatically receive 10 free (shared datacenter) proxies + 1GB/month bandwidth to use for as long as they want, no credit card required. The user who signs up will get a free basic plan, and also have a 25% discount when upgrading.
Best Practices For Staying Safe On The Dark Web
Tails is a mere 1.3 GB download, so on most connections it will download quickly. You can install it on any USB stick that has at least 8 GB of space. While this is good advice for any type of web browsing, be particularly careful not to offer up any personal details, such as your credit card info or email address. Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. On top of that, the installation process of Freenet is rather easy. Simply download the file, install the software, and you’re ready to use its web-based interface.
When you’re on Facebook and you search through content or perhaps on a Flash website with pop-up information, you didn’t click any links. You searched or stayed on the same page, yet you’re viewing different content. This is the Deep Web because it’s not indexable by current search engines. Now you’re probably asking, is the Deep Web and Dark Web even legal? There are many websites that exist within the Dark Web that provide illegal products or services, but generally speaking the Deep Web and Dark Web in and of themselves are legal. They can actually be a fantastic resource of knowledge and power when used mindfully.
Tor Browser And The Dark Web: A Beginner’s Guide To Anonymity And Security
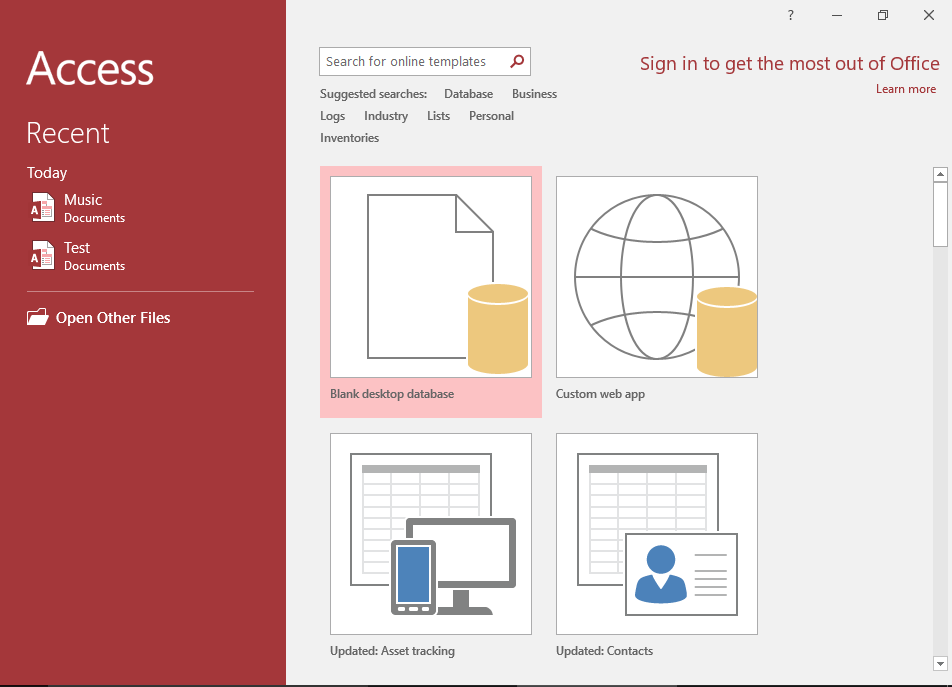
Tor will download the language and add it to the box if this is the first time you are adding it. After the connection is established, you will see a purple-colored welcome screen as shown below. Now, it will take a few seconds or minutes to establish the connection. In the Tor Browser Setup window, select the location where you want to install the Tor Browser. By default, the setup chooses your desktop location which is more convenient to use.