We’ll go into great detail about the benefits and drawbacks of each browser, supported by a useful comparison table. Though secure against everyday threats, Tor is vulnerable to targeted attacks from state-level actors. By default, Tor has stricter privacy settings than most standard web browsers. Users can take further steps to maximize privacy when browsing with Tor. To use a new circuit, click the circuit button next to the domain.
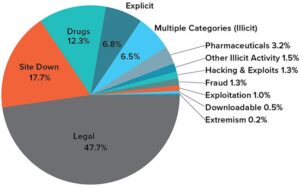
What Kind Of Content Is On The Dark Web?
No, while it hides your IP address and traffic, there are still vulnerabilities. Malicious exit nodes can monitor your traffic, and browser fingerprinting can track you. Governments also often monitor Tor usage, even if they can’t see your activity. It’s recommended to take safety precautions when accessing the dark web, even if you’re after legitimate content.
It safeguards the user’s online activities and identity by encrypting internet traffic and directing it through a series of TOR servers. While the TOR browser is frequently employed to access the dark web, it can also be used to browse the regular web more securely and privately. To find .onion links for dark web sites, you’ll need to use a dark web search engine. Many of them are safe for beginners to use since they filter out dangerous/illegal content to only provide safe .onion links. My favorites are DuckDuckGo (usually the Tor browser’s default search engine), The Hidden Wiki, and Ahmia.
- I found in my tests that all features work identically to the regular version.
- ID Agent and our solutions like Dark Web ID are not a means for accessing the dark web.
- For some, the dark web seems like an underworld filled with cybercrime and dead links.
- You’ll find articles on a wide range of topics, such as history, science, and culture — and that’s just scratching the surface.
- Onion routing is the process of encrypting and routing data through multiple layers (nodes) to ensure anonymity.
Recognize And Avoid Phishing Links
As well as phishing scams, a multitude of other scams operate across the dark web. There are many fake marketplaces and platforms that might offer to sell you goods or services but actually take your money without providing anything in return. Since the dark web is unregulated, there’s almost nothing scam victims can do to seek justice or compensation.
Browse Privately
It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder. Since Tor has to pass your traffic through several nodes, it will slightly slow your speeds. You can use the Smart Location feature for the fastest connections. ExpressVPN is an excellent choice for Tor and accessing the Dark Web. It has a proprietary onion site in the Tor network to give you safe access even if your country restricts VPN usage. Law enforcers can use custom software to infiltrate the dark web and analyze activities.
These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing. For this reason, you cannot browse through these sites using your default search engine. Keep in mind that you’ve to use very specific keywords when searching. And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing.
This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. This is why I strongly suggest using a Virtual Private Network to protect and enhance all of your online activities. A VPN keeps all of your online activities – including your web browsing, online gaming, streaming, and file-sharing – undercover and safe from being tracked or recorded. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you.
Separate Your Real Life From Your Online Persona
Our rigorous research and testing have revealed revealing truths and busted myths. We’ll navigate this intricate maze with you, uncovering its secrets while ensuring your online safety. Tor is like the public-facing door to the dark web, and there are even mobile apps for Android and iOS. Advocacy groups are also reaping the advantages of the darknet because, here, the term of censorship is as popular as HTTPS.
Is It Illegal To Visit Dark Websites?
The Cybercrime-as-a-Service (CaaS) gig economy is the main driver of economic growth on the dark web, and is getting bigger every year. Cybercrime specialists typically sell their goods and services on dark web message boards, Discord servers and Telegram channels, and are generally paid in cryptocurrency. An estimated 90% of posts on popular dark web forums are from buyers looking to contract someone for cybercrime services. It is simply a different section of the internet that is harder to access and less regulated.
Steps To Access The Dark Web Safely
Many services that are allegedly offered on the dark web are scams. Some services are genuine; you can get what you want at an agreed fee. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor.

Its dark web version provides the same functionality as the clear web option, while adding Tor’s anonymity layer. Pitch is a dark web-based Twitter/X alternative, providing a secure platform for anonymous discussions and information sharing. Unlike many dark web platforms, it maintains strict content guidelines while protecting user privacy. Implement dark web monitoring, block Tor exit nodes, conduct security audits, and educate employees on threats. Potential risks include malware infections, exposure to illegal content, and surveillance by authorities. These are search operators (like filetype, intext, site) used to filter specific data on dark web search engines.
It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security. SoftwareLab compares the leading software providers, and offers you honest and objective reviews. Anonymity on the dark web can be both a blessing and a curse, enabling users to protect their privacy while also providing cover for those engaging in criminal activities. Contact us today to learn more about how Brandefense’s dark web monitoring service can help you protect your business and achieve peace of mind.
Journalists, activists, and people in censored countries use it to share news and tips safely. It also allows site owners to run “hidden services” that don’t reveal their server’s actual address. While criminals do misuse it, the original purpose was not to facilitate crime, but rather to provide privacy. The deep web is the private layer, and it’s often password-protected. Here’s a guide that will help you learn about the dark web, the sites that populate it, and how you can visit it safely using the added protection of a VPN and antivirus software.
As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Those who access the dark web do so via the Tor (The Onion Router) browser. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. For example, the deep web is often a platform used by political activists who own a blog. But it also contains other news and religious sites, private discussion forums, and medical records.
Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check. Blockchain even has an HTTPS security certificate for even better protection.
Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. The VPN encrypts your traffic before it enters the Tor network, preventing your ISP from seeing that you’re using Tor. This double encryption also protects against compromised Tor entry nodes that could potentially monitor your activity. Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them.