By observing these patterns, they can link a Tor user’s request to a server and reveal their intended destination. Tor traffic is decrypted at the exit node, which opens a vulnerability for malicious actors to inject malware or intercept traffic. Hence, it’s advisable not to download files via Tor, especially from unknown sources. Tor is slower than standard browsers because it routes your traffic through multiple servers. This routing, through at least three nodes distributed worldwide, introduces latency, especially when there’s congestion on specific nodes.
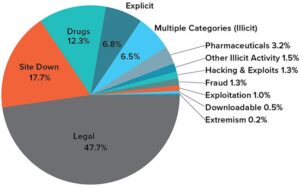
Dangerous And Disturbing Services And Items
- Neither ZDNET nor the author are compensated for these independent reviews.
- Crawling is the process by which search engines scour the internet for new content and websites.
- The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information.
- With this, even the most dangerous malicious actors won’t be able to intercept your browsing activity or know your real location.
- Although it’s not inherently illegal to access the Dark Web, remember that certain sites and activities may be.
Select your platform, click on it, and Tor will download in seconds. This time, you should do it, as you’re already hidden by NordVPN’s encryption. Once the app is installed, simply open it up and sign in with the credentials you provided during registration. The dashboard should open properly, indicating you’re ready to connect to any VPN server. This is just the first but also very important step to go to the dark web anonymously.
Use encrypted communication platforms instead of the standard ones with less robust security features. For example, you can use Signal as your daily messaging app– it has end-to-end encryption and collects minimal data unlike many other messaging apps. To make things simpler, HTTP stands for Hyper Text Transfer Protocol, and this protocol governs communication on the world wide web. It’s what enables web browsers and servers to share information, including web pages and media files. Each server our request passed through had a distinct IP address. The website could only see the IP address of the last server (exit node), not our actual IP address.
This makes it a great option for watching videos from streaming services that are available only in other regions of the world. This is why I strongly suggest using a Virtual Private Network to protect and enhance all of your online activities. A VPN keeps all of your online activities – including your web browsing, online gaming, streaming, and file-sharing – undercover and safe from being tracked or recorded. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you.
More Ways To Stay Safe On The Dark Web
The vast majority of transactions consisted of illegal drugs, but you could also find weapons, personal information, child pornography and stolen credit card details. Allegedly, it was also possible to hire hit men on the site, though it’s never been proven that any of these contracts were actually fulfilled. The dark web refers to the subsection of the deep web that provides illegal services.
Plus, the ISP won’t see that you’re using Tor, which is excellent. We also prefer this method because of VPN’s all-encompassing security. Now that your connection is active, it’s encrypted and untraceable by your internet provider.

Tor Browser: The Essential Classic For The Dark Web
Although it’s not inherently illegal to access the Dark Web, remember that certain sites and activities may be. Stay vigilant, trust your instincts, verify sources, and prioritize your security to make the most of the anonymity these networks provide. Now that you understand the essentials of anonymous networks and how to prepare yourself for secure browsing, it’s time to explore the practical steps involved in accessing the Dark Web. While the process is not overly complicated, it demands attention to detail, adherence to best practices, and an understanding of the risks. For one, the VPN can’t see your online activities because of VPN encryption.
Other Built-in Tor Features You Should Know

Arguably, the best-known tool used to access the dark web is the Tor Browser. This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. Since each node server in the Tor network is volunteer-operated, you never know who operates the relays that your data is traveling through. While this isn’t an issue for most of the trip (since each relay only has access to the previous and next relays in the network), it is an issue with the exit node. Often, what you can’t find in a search engine, you can find in various government and open access journals that you can search on Google. One example is USA.gov, which houses all files connected to the U.S. government.
Anonymity Is In Your Hands
What’s most interesting is that you don’t need to install anything. You simply boot it from a USB stick, and that’s it—you can use it on almost any computer without leaving a trace. Freenet isn’t just an anonymity tool—it’s practically a digital manifesto.

Disadvantages Of The Tor Browser
- The dark web has several convenient uses, which are not all basic.
- There’s the surface web, which is visible like the floating tip of an iceberg, and then there’s the deep web, which is the bigger part of the iceberg extending far below the surface.
- Then, install Norton 360 Deluxe to get AI-powered scam detection to help secure your browsing against online threats.
- It certainly isn’t illegal – not when it is actively used by all websites and permeates everything we do online, apart from idle browsing.
- To connect manually for the first time, click on the Connect button on the homepage and wait for Tor to establish a connection.
For example, you could find a passport from a UK citizen there for under a million dollars. The information can be of any kind, either social security numbers or even bank card numbers (the bank/credit card information is usually sold in bulk). The open web makes up less than 4-5% of the internet, which is just the tip of the iceberg of the entire internet. Call it curiosity, but many people are genuinely enticed about the idea of exploring the deep web. And although the deep web is often seen as the den of cyber criminals, there are actually a lot of interesting and useful things3 hidden there. With TecnetOne, you see what others don’t—and act before it’s too late.
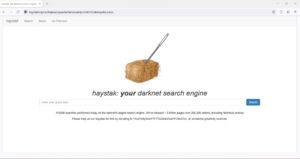
Finding Onion Sites
The dark web is part of the deep web and is hosted on darknets and encrypted networks like Tor, Freenet and Riffle. It comprises websites, resources and services that aren’t indexed by regular web crawlers. The websites are hidden in layers of encryptions and use dot (.) onion domains, which is why they are called onion sites. Tor protects your identity inside its network, but it doesn’t hide everything. Your ISP still knows you’re using Tor, and entry nodes can see your real IP address. A VPN adds protection before Tor, closing these gaps without breaking access to .onion sites.
A logless VPN, which doesn’t store any traffic logs nor session logs is highly preferable. Traffic logs are a bigger concern than session logs, but neither are good. Tor is a Firefox-based browser made specifically to enable access to onion sites, hence the name The Onion Router. This browser, on paper, ensures anonymity by routing your traffic through different “secure” nodes, preventing tracking and surveillance.
In 2002, the dark web grew significantly when researchers supported by the US Naval Research Laboratory built and released the Tor network. At the time, the internet was still young, and tracking people was easy while staying anonymous was not. The Tor network allowed safe communication channels for political dissidents and American intelligence operatives around the world.
As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%. Anyone can access the dark web, and it’s not that complicated to do so. Just remember, if you want to explore the dark web, be very careful. Tails is a mere 1.3 GB download, so on most connections it will download quickly.