Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. The experience is reminiscent of searching the web in the late 1990s. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query.
Best Dark Web News Sites Offering Factual Information
However, with all its advantages, Litecoin does not offer any additional security to its owner. Our subsequent research showed that the vendors alone represent the primary deciding factor regarding which payments will be implemented and which will not. As we described in our previous blog, the underground economy is dependent on smaller transactions in its day-to-day operations, with the cost of the average product or service beginning between $50–$300. With the addition of exuberant transaction fees, the price of such products and services suddenly inflates tremendously. A type of decentralized cryptocurrency that uses a public distributed ledger with privacy-enhancing technologies to keep finances anonymous and secure, increasing in popularity on the darknet.

Apocalypse Market
All vendors that were surveyed by the researchers still offered Bitcoin as an accepted means of payment. What is more of a surprise though is that Litecoin is the second most accepted coin by the vendors with over 30% of them accepting it as a method of payment. The investigators at Recorded Future then went on to try and establish which of those coins are beginning to replace Bitcoin as the currency of choice on the Darknet. Indeed, Bitcoin has become too mainstream for criminals as the extent of law enforcement tracking powers have been disclosed. But its share of the overall market may diminish in the future, given the mostly positive pronouncements about other currencies by vendors in Recorded Future’s report. Also called, 0day, a security design flaw or vulnerability that can be exploited with critical consequence, but cannot be quickly mitigated or patched by the hardware or software vendor.
- Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments.
- The fight against cryptocurrency money laundering is a complex challenge that requires a multidimensional approach.
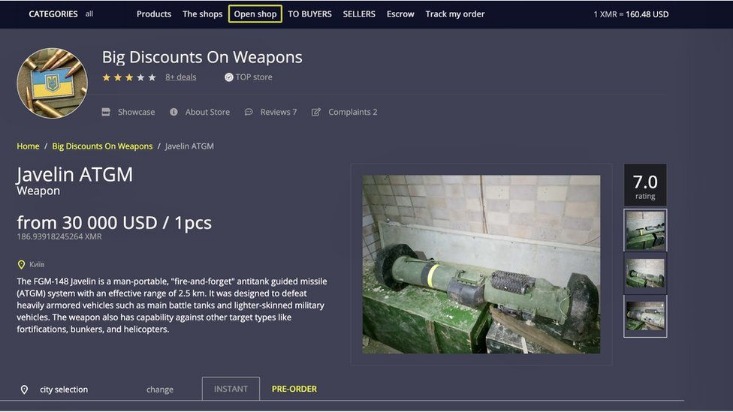
- These marketplaces have become popular hubs for illegal activities, enabling users to buy and sell illicit goods and services with relative ease.
- The dark web is where these coins are widely accepted unlike the real world where they are still taken more as a commodity than a currency.
- Text that is sent by a server to a web client, and returned by the client each time it uses that server.
The Bottom Is Near: Bitcoin Miners Officially Enter Capitulation Window For The Second Time In 2022
Other popular marketplaces include Dream Market and Empire Market, which also accept cryptocurrencies as a means of payment. As digital currencies become more widespread, they have unfortunately also been implicated in numerous instances of financial crime. This section explores some significant cases of cryptocurrency money laundering, highlighting the role of virtual assets in such illegal activities.

Separate Your Real Life From Your Online Persona
Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research. Is there any way to buy monero (or another currency then exchange to monero) in the same way localbitcoin used to work. In one of the latest reports, Chainalysis identified Eastern Europe as a leader in darknet market activity. In addition to the growing popularity of Bitcoin wallets with CoinJoin, the report authors note a rising demand for Monero, focused on enhanced cryptocurrency privacy. The growing popularity of Wasabi and Samourai Bitcoin wallets with coin-mixing capabilities significantly complicates the tracing of darknet activity. The finding is contained in the report from the European Union Police Service (Europol) on internet-related threats.
Empire Market
If there is one thing that we can learn from Bitcoin it is that the early adopters of the dark web have a knowledge of what is likely to disrupt the mainstream later. However, these were just the results of one forum on the darknet and hence cannot be considered as a comprehensive representation. After doing a more thorough analysis, the team concluded that Bitcoin was still the vendor coin of choice on the networks. It is often very difficult to get a judgement of exactly which coins are favoured by those who operate on the dark web. However, an interesting report has recently delved into this internet underground and found interesting results.
It has an active forum and community along with an extensive user vetting process. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar.
Impact Of Regulations On Crypto Industry
While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results. This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. For now, the race is between Litecoin and Dash, with Monero coming fast from behind.
You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. To learn more about the challenges and strategies in tackling money laundering via virtual assets, visit our articles on virtual currencies and money laundering and virtual asset laundering methods.
Large numerical value used to encrypt data and is publicly shared and used as a security tool to check legitimacy of digital messages and signatures. Also known as money mules; People that help conceal the identity of a cybercriminal by assisting in fraud by moving money illegally on their behalf. Otherwise known as cryptocurrency mining; Process where new cryptocurrency coins are verified and added to the blockchain. A common technique utilized by cybercriminals to test if historically exposed e-mail addresses and password combinations are valid logins across multiple commercial websites. Forum features ‘images’ with posts and known for fast-based, politically charged discussions. A shared ledger that facilitates the process of recording monetary and other asset digital transactions.
Mega Market
It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now). It’s somewhere Google and Bing don’t index, and you need special tools to get to it. Décary-Hétu called privacy coins “essential,” and said they represent a new reality for law enforcement to adapt to. “My default position is to let innovation work its way out. And then assess it. Don’t go and kill something off just because you don’t understand it.”
That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Talking about copycats and potential risks, due to its high risk and low signal-to-noise ratio for legitimate content, we advise beginners and privacy-conscious users to avoid The Hidden Wiki. If you must explore sites like The Hidden Wiki, do so with extreme skepticism, never download files, never enter personal info, and never send cryptocurrency to unknown sites.
Fraud And Hacking Services
Tracking a wallet’s owner is extremely difficult, despite the fact that in the blockchain everything is transparent and open. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web.
It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity. The dark web is a decentralized web, which means that the data is stored on many different servers around the world. Business operational data, such as operational data, financial data, intellectual property, and trade secrets can be found on the dark web. Lastly, the dark web is also used by activists and revolutionaries (like Anonymous).
- In addition, know that while accessing the dark web is legal in most countries, engaging in illegal activities (buying or selling contraband, hacking services, etc.), is illegal everywhere.
- To understand and anticipate any upcoming shift in the next six to 12 months, Recorded Future analyzed 150 of the most prominent message boards, marketplaces, and illicit services.
- NinthDecimal is the leading media and technology service provider for the WiFi industry.
- Tor2door claims that security and usability are its main priorities.
In Tor, bridge relay nodes are like ordinary Tor relays, are also run by volunteers, but not listed publicly. An intentional attack on a network, usually targeting organizations or corporations. The information that comes from a breach can be the same or similar as what comes from a Leak, but the method of obtaining said data is by direct attack instead of undisclosed vulnerability. An army of compromised computers or internet of things (IoT) devices that collectively utilized for a malicious purpose.
Of course, there are other reasons that restrain the process of legalization, related to tax issues, money laundering, ICOs and investment risks. The term “darknet” first appeared in the 1970s and referred to the private networks with a high degree of confidentiality. And though, initially, the “anonymous Internet” didn’t mean something dangerous, gradually it started to go underground and became a means of communication for illegal activities and crime.


