Augmented Reality NFTs represent a convergence of cutting-edge technologies that redefine the way we interact with digital assets. Access darknet markets using Tor browser, a reliable VPN, and take precautions such as safeguarding your identity and not revealing personal information. We strongly suggest using a VPN while you’re researching and publishing articles to gain extra protection from prying eyes. This website comes in handy for people living under oppressive regimes, as ProPublica doesn’t shy away from covering controversial topics, such as child labor and corrupt politicians. ProPublica is an investigative journalism outlet that has a presence on the surface web as well as a dark web link. Some countries and governments implement strict online censorship and block access to foreign news outlets.
Articles are published regularly and include interesting information, images, and quotes from officials. You’ll also find a computerized equatorial mount within the VX Edge HD, with its main axis pointed at the celestial pole. As a result, the same mount can be used with a range of other telescopes and even cameras, so it’s ideal if you’re into astrophotography. The Celestron NexStar 8SE is no small investment when it comes to the cost, but this feels like a telescope that is really built to last. Edge-to-edge sharpness across the field of view and superb design means astronomers can upgrade this scope to last for years.
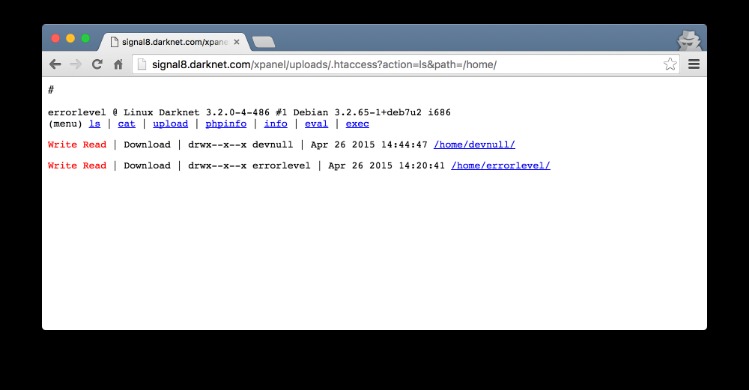
Media Blackmail: Businesses To Learn They Were Hacked From Hackers’ Public Posts With A Countdown To Release

Norton 360 has a complicated pricing structure, including low introductory rates that renew at a significantly higher price after your first year. All plans (except the most affordable AntiVirus Plus plan) include Dark Web monitoring. While free Dark Web monitoring is an attractive option, LastPass simply isn’t doing enough to earn back its customers’ trust and provide top-notch services. We continuously monitor underground markets for the emergence of new “cryptors,” which are tools specifically designed to obfuscate the code within malware samples. The primary purpose of these tools is to render the code undetectable by security software. In 2024, our expert observations indicate that commercial advertising for these cryptors have indeed gained momentum.

Do I Need A VPN If I’m Already Using Tor?
This includes supermarkets and hypermarkets, convenience stores, non-grocery retailers, and others. And then there’s the bad stuff – contract killers, child porn, drugs, and other nasty stuff which share the same benefits of anonymity as the good sites. Because of the protection offered by the Darknet and its hidden services, activists in oppressive regimes are free to exchange ideas and organize themselves. “Anyone who knows my record knows I will never bow to special interests or industry pressure, no matter how well-funded by dark money from shady sources,” Brown, who is up for reelection this year, told CNBC. Your safety on the dark web depends more on cautious browsing habits than any single security tool. While a VPN adds valuable protection, being selective about which sites you visit and never sharing personal information are equally important.
Considerations When Accessing Darknet Markets
- It was announced shortly thereafter that an international law enforcement operation brought AlphaBay down.
- We also assisted the joint INTERPOL and AFRIPOL operation combating cybercrime across Africa.
- Both nominal and real wages & salaries in personal income and unearned personal income (including interest income, dividends, rents, and proprietors’ income) rose to record highs during October (Fig. 8).
- Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats.
- It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last.
Navigating the depths of these hidden services requires specialized tools and a cautious approach. The Tor Browser, a modified version of Firefox, is a common gateway to these services. It routes traffic through multiple layers of encryption, masking users’ identities and locations.

Related Posts
Our technology scans the dark web for any mention of your sensitive data and sends timely alerts to protect your business from exposure. CyberNod stands as a trusted partner in the fight against dark web threats, ensuring your security as the hidden underworld continues to grow and transform. Market listings on these platforms often carry the same professional touch you’d expect from legitimate sites complete with product descriptions, seller ratings, and even customer reviews.
#BHUSA: 1000 DoD Contractors Now Covered By NSA’s Free Cyber Services Program
Also, it doesn’t log your IP address or any information about your browser or device. The best news is Torch updates its sites every single day, so you’ll always be able to browse the latest news and access new services and sites. “Some of the sellers in the market advertised shipping from the Netherlands,” the Politie said. “An initial analysis shows that at least 14,000 transactions took place from the Netherlands with a value of at least 1.7 million euros.” In general, we have noticed an overall increase in the frequency of corporate database advertisements on the dark web.
Agentic AI In Cybersecurity: Transforming Threat Detection And Defense
This mechanism holds funds in a secure account until the buyer confirms receipt of the product, reducing the risk of fraud. Additionally, multi-signature transactions are increasingly common, requiring multiple parties to approve a payment, further enhancing trust between users. Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence. It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data. The marketplace is well-known for its bug bounty programs and robust security mechanisms, including mandatory 2FA. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring.
- Sellers can list their products and services, set prices, and communicate with buyers through a messaging system.
- It features over 40,000 listings including narcotics, counterfeit items, hacking tools, and stolen data.
- Additionally, many markets now integrate PGP encryption for communication, further safeguarding sensitive information.
- While hard statistics are scarce, darknet markets have continued gradual growth for years.
- One such sophisticated darknet market, Hydra, offered all that and more,” Chainalysis explained.
Centralization Risks
This, combined with the use of onion addresses, ensures that users can access these platforms without exposing their identities or locations. One of the key factors contributing to the success of these markets is the emphasis on vendor ratings. These ratings are based on user feedback, delivery speed, and product quality, creating a transparent system that rewards trustworthy vendors. High-rated vendors often gain more visibility, which incentivizes others to maintain high standards. This system ensures that buyers can confidently select sellers with proven track records, reducing the risk of scams or low-quality products.
Explore a diverse selection of goods and services, with a focus on privacy and security. Always remember that while the above measures significantly reduce risks, no method guarantees complete security on the dark web. Always exercise extreme caution and verify the legality of any services you access. KeyBase combines encrypted messaging with secure file sharing and identity verification.
Law enforcement agencies have seen notable successes in identifying and apprehending darknet market operators. Their focus tends to fall on the largest markets, or those that have operated the longest. This attention can be too much for some markets, which will voluntarily close rather than remain an obvious law enforcement target for too long. Darknet markets are an important part of the underground criminal economy and facilitate the trade of illicit goods and services ranging from narcotics to hacking tools. Law enforcement agencies worldwide are actively monitoring onion activity, and cybercriminals are constantly devising new scams and malware to exploit unsuspecting users. To mitigate these risks, hidden onion users must prioritize security and privacy.
In the intriguing realm of the dark web, the prevalence of drug-related listings has garnered significant attention. The GA version has normally undergone all testing and finalization to be ready for commercialized purchase, including regulatory and security testing and more. Der Tor-Browser hingegen verschleiert solche Informationen, indem die Anfrage auf seinem Weg über mehrere Server auf der ganzen Welt wie eine Zwiebel umhüllt, also verschlüsselt wird. In this blog post, we will dive deep into the latest dark web statistics, shedding light on the scale, activities, and trends that define this hidden realm of the internet. By exploring the data and understanding its implications, we can better navigate the murky waters of the dark web and remain informed about its continuous evolution.



