
Instead, they receive a new disposable wallet for every order they place, and the cryptocurrency they deposit goes straight to the vendor — the market itself never actually controls it. Cryptonia was an active market that incorporated both multi-signature transactions and wallet-less escrow, though it recently closed down voluntarily. In recent years, some darknet markets and fraud shops have been integrating crypto payment processors on their websites via APIs, possibly as a way to improve operational efficiency and increase security. Essentially, these payment processors provide a white label service for darknet markets and fraud shops, and a seamless checkout experience for those services’ customers. UAPS, shown in the chart above, is one such example of a payment processor that many fraud shops, including the OFAC-designated Genesis Market, used in 2023. The value received by UAPS in this chart includes payments sent to multiple fraud shops using the service as a payment processor.
Darknet Market Links
This section explores Ponzi and pyramid schemes, ICO scams, rug pulls, and phishing attacks, as well as cryptojacking, fake wallets, and fraudulent exchanges. Addressing these risks requires clear regulations, effective monitoring, and collaboration between regulators and blockchain developers. Implementing compliance measures and leveraging technology can help balance privacy with security.
The chart above shows that, while values haven’t risen back to 2021 levels, darknet market revenue has slightly rebounded since Hydra’s closure in 2022. This defunct darknet market didn’t immediately move all its Bitcoin, and Nucleus still retains about $365 million in BTC. The price of Bitcoin has shot up astronomically since the company’s heyday; at no point in 2016 did BTC cross the $1,000 price point. So-called “ancient” Bitcoin whales pop up in the space periodically, but an extant darknet vendor is still quite rare. Nucleus’ assets have appreciated in value astronomically, but it will be very difficult to convert this BTC into fiat currency.
The Role Of Crypto Anonymity Tools
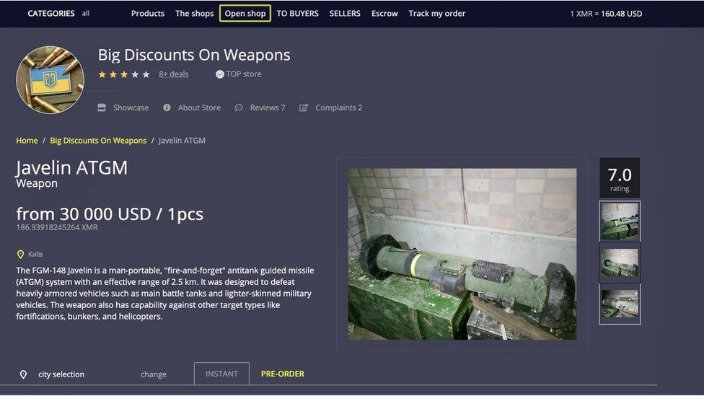
Cryptocurrencies have become integral to the dark web economy, enabling illicit transactions and fueling cybercrime activities. Initially, Bitcoin was the primary currency for darknet markets, but its traceability led to the rise of privacy coins like Monero and Zcash, which offer enhanced anonymity. These digital assets facilitate underground economies involving drug trafficking, weapons sales, and cybercriminal services. Despite advancements in blockchain analytics and regulatory measures, privacy-focused technologies continue to pose challenges for oversight and Anti-Money Laundering (AML) enforcement. Today, darknets are populated by a vast array of users, ranging from privacy-conscious individuals to cybercriminals, hacktivists, and nation-state actors.
Incognito Secures
Analytics Insight is an award-winning tech news publication that delivers in-depth insights into the major technology trends that impact the markets. The content produced on this website is for educational purposes only and does not constitute investment advice or recommendation. Always conduct your own research or check with certified experts before investing, and be prepared for potential losses. Opinions expressed herein are those of the authors and not necessarily those of Analytics Insight, or any of its affiliates, officers or directors.
Its 9,000+ users and 700+ vendors focus on drug trades with strong escrow security. Below are 2025’s leading darknet markets, ranked by listings, trade volume, and vendor reliability. Each offers unique strengths in cryptocurrency trading and escrow security—essential for navigating the onion network. Your definitive guide to the top darknet marketplaces of 2025—featuring verified onion routing links, cryptocurrency trading insights, vendor ratings, and escrow security details. “Over the years some markets … developed a robust catalog of illicit services like money laundering, fiat offramping, and products that enable cyber-criminal activities like ransomware and malware attacks.
These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. While China-based vendors are frequently referenced as the source of precursors for dangerous synthetic drugs, their involvement in machinery sales is also an important aspect of the drug supply chain. One China-based pill press manufacturer which advertises on clearnet business-to-business (B2B) websites has on-chain ties to drug vendors on Abacus Market. Along with its listings for large pill press machines, the vendor does not hide the sale of Oxycontin and Xanax TDP die kits, which are used to press counterfeit pills. The vendor accepts BTC and XMR, and analyzing its on-chain exposure to regional CEXs and DNMs reveals that it serves customers worldwide, including in the United States, Canada, Sweden, and Russia.
Mixers, Exchanges, And New Markets
AI simplifies pattern recognition, and blockchain forensics leverages openness in trying to follow illegal transactions and construct lawful evidence. Protecting digital assets requires vigilance, secure platforms, and education on potential risks. As the crypto industry evolves, fostering transparency and proactive security strategies will be essential to building trust and ensuring a safer investment environment. Criminals employ layering and structuring methods to conceal their illicit Bitcoin transactions, which are hard to track and regulate. By breaking large sums into smaller transfers and leveraging multiple exchanges, they evade regulatory scrutiny. These methods exploit gaps in compliance frameworks, complicating efforts to track and prevent financial crimes.
This differentiation will be key to building trust and attracting institutional capital. Investors, in turn, must conduct thorough due diligence, diversify their portfolios, and remain acutely aware of evolving regulatory landscapes. Monitoring global regulatory harmonization efforts, the development of Central Bank Digital Currencies (CBDCs), and geopolitical events will be crucial, as these factors can significantly influence market sentiment and project viability. The primary market impact of the RAKS bust is less about direct price volatility of specific tokens and more about the intensification of regulatory scrutiny. This event will undoubtedly bolster calls for stricter Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations across all legitimate Virtual Asset Service Providers (VASPs). Regulators, already armed with increasingly sophisticated blockchain forensics and chain analysis tools, will likely redouble their efforts to monitor suspicious transactions and enforce compliance.
The Dark Side Of Cryptocurrency: How Digital Assets Fuel Money Laundering And Illicit Trades
The pseudonymous nature and evolving tactics of criminals make regulatory oversight challenging. Strengthening Anti-Money Laundering (AML) and Know Your Customer (KYC) measures, along with advanced blockchain analytics and AI-driven monitoring, can help mitigate illicit activities while preserving the benefits of digital finance. Historically, Telegram has been a favored platform for selling drugs — due to its security and public perception of non-cooperation with law enforcement, as well as strict access controls for groups and channels. However, Durov’s arrest has heightened fears that Telegram will now provide data on its users to law enforcement.
Combatting Online Drug Sales: Should Law Enforcement Chase Vendors Or Shut Down Markets?
These tools pool and redistribute transactions, making it challenging to trace senders and recipients. While they provide anonymity, they also pose regulatory challenges by complicating financial tracking and raising concerns about illicit activities. Cryptocurrencies are using decentralization, transparency, and security, fostering financial inclusion and innovation in decentralized finance (DeFi) and tokenized assets.

- Implementing AI-powered fraud detection, enhancing oversight, and promoting responsible adoption will help build a more transparent and resilient crypto ecosystem.
- As digital finance evolves, striking a balance between innovation and security is crucial.
- Not only that, but for the first time since 2015, darknet markets increased their share of overall incoming cryptocurrency transactions, doubling from 0.04% in 2018 to 0.08% in 2019.
- Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web.
- Darknets and dark markets have fueled the growth of cybercrime, provided a marketplace for cyber threats, and expanded the attack surface for malicious actors.
- The unique part is that the platform offers free samples of stolen information, often to attract more customers.
Darknets and dark markets present a multifaceted challenge to businesses and society as a whole. While these hidden networks can be used for legitimate purposes, they are equally significant as vectors for cybercrime and illicit activities. To mitigate risks and secure against the potential fallout, businesses need to adopt a multi-faceted approach, combining robust cybersecurity, regulatory compliance, and vigilant monitoring to adapt to the evolving threat landscape. Dark markets provide a one-stop-shop for cybercriminals, offering a wide range of services such as hacking tools, stolen data, ransomware, and Distributed-Denial-of-Service (DDoS) attacks for hire.
Reddit Darknet Market Noobs
- In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks.
- Retail vendors appear to be holding a greater portion of their proceeds on-chain than wholesale vendors, while wholesale vendors (those who distribute drugs in large quantities) are making greater use of DeFi.
- In addition to these tools, the market offers access to compromised accounts, VPN services, and digital identities, making it a hub for individuals involved in illegal activities like hacking, identity theft, and other forms of cybercrime.
- Cryptocurrency fraud has seen a significant rise in recent years, with various schemes exploiting the digital nature of cryptocurrencies.
- While they provide anonymity, they also pose regulatory challenges by complicating financial tracking and raising concerns about illicit activities.
The site operator, known only by the alias “Vito,” attributed the site’s withdrawal delays to a flood of new users and a distributed denial-of-service (DDoS) attack, an excuse seen in previous exit scams such as Evolution and Nemesis. The hacking claim may be true, as the alleged rogue employee posted vendors’ mnemonic sequences — random series of words vendors could enter to recover their passwords — which several vendors then confirmed were correct. The hacker also posted screenshots of Nightmare’s backend, such as its user analytics and financial data. By leveraging automated dark web monitoring, organizations can mitigate risks, and take preventive measures before the leaked data is exploited. This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web.
– Silk Road Launch
A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials.

Some markets have services related to cybersecurity, while others might list more controversial items. This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats. Our regional data reveals that most people buying stolen credit card data on UNICC are from North America (after Global), while most of those selling it are from China. While it’s difficult to say exactly why that is, it’s possible that more criminals from China have the technological proficiency to steal credit card data.



