Assuming everything checks out, once you successfully log in, you can navigate through the site to explore the vast selection of stolen credit card data and sensitive information available for sale. However, it’s important to exercise caution, as Blackpass takes security measures seriously, and any carelessness could lead to failure or potential legal consequences for those caught misusing or stealing sensitive data. Comparitech researchers gathered listings for stolen credit cards, PayPal accounts, and other illicit goods and services on 13 dark web marketplaces.
See Why DarkOwl Is The Leader In Darknet Data
Emerging on April 30, 2024, it quickly gained notoriety by releasing 1 million stolen payment card details for free, a strategy aimed at attracting cybercriminals to its platform. The market sells credit card information to users occasionally shares free credit card dumps (as seen below). In this blog, DarkOwl analysts take a deep dive into the market, how it operates and what the reaction to the site has been on the dark web.
Criminals sell stolen credit card information in different formats, such as CVV codes (Card Verification Value), full cards, or complete dumps of thousands to millions of records. One critical action a company must take when facing a credit card dump is to notify customers of the breach as soon as possible. In many cases, state and federal laws require that companies disclose any unauthorized access to customer information.
- Joker’s Stash still has imitators that masquerade as the now-defunct site, researchers say, with the goal of capturing that old traffic.
- This information is then used to create counterfeit credit cards or make fraudulent online purchases.
- Criminals may use credit card dumps to make high-value purchases, such as luxury goods or electronics, as these items can be easily resold for a profit.
- Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents.
- While no method is foolproof, being informed and proactive in safeguarding your financial data goes a long way towards protecting yourself from cybercriminals.
- As unsuspecting customers pull up to refuel their vehicles, they insert their credit cards into the compromised card reader.
The Easy Way In/Out: Securing The Artificial Future, Trend Micro Security Predictions For 2025
Pattern recognition through machine learning has revolutionized how we spot compromised cards. I’ve worked with family-owned businesses that nearly went under after getting hit with a wave of fraudulent purchases. When fraudulent transactions occur, merchants frequently end up eating the costs through chargebacks. The Magecart group pioneered this technique, compromising thousands of online stores by exploiting vulnerabilities in popular e-commerce platforms.
Dangers And Risks Of Credit Card Dumps
Notice how it normalizes fake data buying by including buyer ratings and comments. As the local dealers say, the first hit is free, though in this case such a leak could have meant free money for any user who managed to snag a card. Researchers are still looking into the leak, but early reports show many of the cards could have already been reported to the card issuers.
These listings can include information such as the BIN number, credit card number, expiration date, and CVV number. In this hypothetical scenario, let us study the actions of a cybercriminal, Alex. Alex is well-versed in credit card fraud and decides to target a local gas station. He discreetly installed a credit card skimmer on one of the gas station’s card readers. A credit card skimmer is a device that looks like a normal card slot but is designed to secretly capture credit card information.
Not to mention the resulting tarnished reputation, which required extensive post-event damage control. For example, it is used in money laundering schemes and to turn dark money into “legitimate” funds. The proceeds from sales of card numbers are used for enabling organized crime and gang activities, weapons exchange, trafficking drugs and guns, and many other illegal activities, he says.

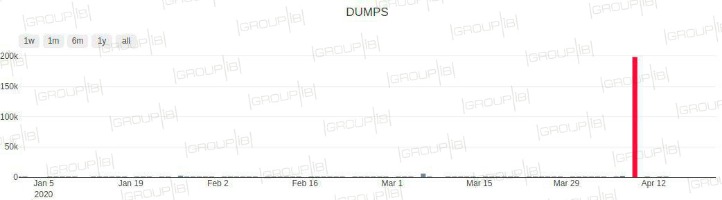
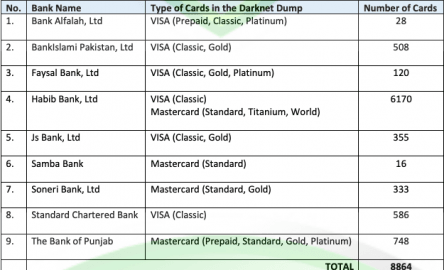
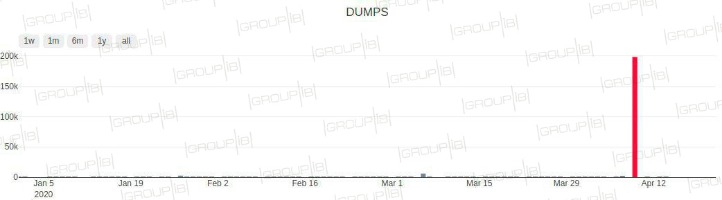
Darkweb Market BidenCash Gives Away 12 Million Credit Cards For Free
B1ack Stash’s primary motive from the outset has clearly been financial gain, which they have pursued by building a strong reputation as a card seller within the carding community. Our analysis of the payment card details leaked by B1ack over the past six months and the data we’ve collected for the affected local banks indicates that these were largely obtained through phishing campaigns. The data format, which includes user agents and victim IP addresses typically observed in both local and global phishing attacks, allows us to assert with high confidence that it originated from such activities. Financial data can leak in many ways—through phishing attacks, data breaches at online services, or poor account security.
Agentic AI In Cybersecurity: Transforming Threat Detection And Defense
Harris said, “this particular seller has a rating of 4 and a half out of 5 stars. So, it appears they have been doing this for a while and have some good customer service.” The operators of BidenCash have caused significant harm to millions of victims whose personal and financial information has been compromised. The average price of a cloned, physical card is $171, or 5.75 cents per dollar of credit limit. The answer lies behind distributed denial of service (DDoS) attacks that targeted its original domains. As a result, in order for word to get out in regard to fresh URLs for the service, the hackers are distributing the data free of charge. One of the largest known underground shops, Joker’s Stash, generated more than $1 billion before getting shut down in February, according to Gemini Advisory.
- While the site claims to source data ethically, there are substantial risks involved in its use.
- Virtual cards generate one-time use numbers that can be linked to your actual account, making them less susceptible to being stolen in data breaches.
- Believe it or not, some dark web marketplaces have pretty advanced systems for building trust.
- A significant portion of this data was uniquely identified in our intel collection.
- As detailed in a Saturday report from Bleeping Computer, BidenCash first came onto the scene in June this year when they leaked several thousand credit card details for free online.
Ways Agentic AI Is Transforming Cybersecurity

It’s essential to keep your credit card information private and not share it with others. The dark web operates similarly to legitimate e-commerce platforms, with buyers browsing through listings and selecting cards to purchase using cryptocurrency or other anonymous payment methods. Credit cards are designed to facilitate easy and secure transactions, but they can also be vulnerable to unauthorized use. “It is conceivable that the data was shared for free to entice other criminal actors to frequent their site…by purchasing additional stolen data from unsuspecting victims,” according to the post (machine-translated from Italian).
Cyble Strato Cloud Security
Criminals obtain this data through various methods, such as skimming or hacking into payment systems. Once obtained, the stolen credit card data is resold to other individuals or criminal organizations on the dark web. This massive data breach highlights the importance of businesses taking a proactive approach to cybersecurity to prevent similar incidents in the future. A credit card dump can result in significant financial losses for both consumers and companies. For individuals, credit card dumps can lead to identity theft, unauthorized transactions, and other fraudulent activities. In some cases, the stolen information may be used to open new credit accounts or loans, leading to long-term consequences such as damaged credit scores and financial strain.
Dark Web Marketplace ‘BidenCash’ Hands Out 12 Million Stolen Credit Cards As A Promotion
By understanding these incidents, we can better appreciate the significance of data security measures like multi-factor authentication, encryption, and real-time monitoring. Additionally, staying informed about potential threats and taking steps to secure our personal information is crucial in an era where data breaches have become a worryingly common occurrence. B1ack’s Stash’s emergence and rapid growth highlight the ongoing evolution of dark web marketplaces and the persistent threats they pose to global cybersecurity. By strategically releasing millions of stolen credit card details for free, the marketplace has garnered significant attention—both from cybercriminals looking to exploit the data and security researchers tracking its impact. The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage.
Credit Cards Showcase
Organized criminal groups have recognized the potential profitability of credit card dumps and have turned it into a lucrative business model. These groups invest in advanced tools, techniques, and infrastructure to target victims and monetize their stolen data. They sell the information in various forms, such as individual card numbers, cardholder details, or entire databases, depending on the demand and price range. The prevalence of credit card dump activities highlights the need for improved security measures in our financial systems. Financial institutions, merchants, and individuals must prioritize robust security protocols, employ encryption technologies, and stay updated on the latest threats to prevent credit card information from falling into the wrong hands. By following these measures, you can significantly reduce the risk of falling victim to credit card dump fraud.



