
Again, not all the dark web is used for illicit purposes despite its ominous-sounding name. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. It has a bidding feature, with new batches of stolen data being frequently added. The second category consists of data stores, which specialize in stolen information. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. Please note that personal data collected through this form is used and stored for the purposes of processing this report and communication with you.
Elliott believed his stress stemmed from secret work he claimed he had done for the government. An analysis by Secret Service experts linked the fraudulent bills to thousands of others that had been passed with a total face value of $4.1 million. That made Billmaker the nation’s most prolific domestic counterfeiter. “Thanks to the Brantley Dollar General location, we’ve been able to pretty much eliminate that as a threat to our local businesses here in Crenshaw County,” Nix said. “Stay aware that this could go on and could happen to all of us. Printing, like any technology, gets better and better as time goes on so we always have to have our guard up.”

Buy Counterfeit Money Online

In addition to that, our prices are fair enough, understand the financial constraints our clients go through, so they can get their basic needs. The report goes on to detail these underground marketplaces’ feedback systems as a means to observe an increase of quality with regards to these notes. The research also revealed that during this time, the number of unique actors selling these fake bills increased by approximately 82%.
Darknet Counterfeit Money For Sale: Exploring The Deep Web’s Illicit Trade
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. Telegram channels supplement traditional onion sites, blurring lines between the dark web sites and more mainstream communication tools. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. The estimated face value of the notes was about 1.3m euros ($1.4m; £1.1m). To report inappropriate content on this page, please use the form below.
Many dark web sites deploy tools that prevent bots and web crawlers from accessing the site. Some well-known underground sources can be easier to find because there are dedicated sites that share links and maintain regular status updates. But in many cases, finding the exact URLs through manual search methods can be next to impossible.
Stolen Credit Cards On Dark Web Platforms
All work should be tracked in Google Analytics and Search Console so we can measure improvements in ranking and, more importantly, revenue attributed to organic traffic.For social media, I’m concentrating exclusively on Instagram. I have a complete research topic ready and now need a seasoned academic writer who can turn it into a publication-ready PhD paper in Computer Science, with a heavy emphasis on machine learning, deep learning and AI. I will expect a polished structure—abstract, introduction, related work, methodology, results, discussion and conclusion—with clear, well-commented equations, figur… Sometimes hackers will commit “card-present fraud” by breaching the point of the sale at a physical store. Or they’ll commit “card-not-present fraud,” by hacking a website and stealing the online card information that gets entered into the checkout page. With stolen payment cards, a cybercriminal can immediately make purchases under your name, or even drain your bank account.
- Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors.
- Discrete measures in the counterfeit business are very essential as it protects both the buyer and the seller.
- There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks.
- All of these features, its competitive pricing, along with the volume of credit card information listings, make Real and Rare one of the prime sites to trade credit card information online.
Stolen Crypto Wallets
Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it.
Unmasking The Underworld: Counterfeit Money For Sale
These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. More than 26,000 fake banknotes had been bought from – and delivered by – the gang, according to the agency. We keep all client’s identities very secret and reship in case of unsuccessful delivery. Just let us know exactly what you want, the amount, and your location. Counterfeit Money for SaleWe have been printing banknotes for more than 5 years and our expertise is reflected in every note, with our high-tech printing processes and quality inspection systems.
Why Deal With Us For The Purchase Of Fake Notes Dark Web

Stolen credit cards and their details are added and bought on these shops on an hourly basis, and more and more markets launch a matching forum and/or a Telegram channel to keep expanding and supporting criminal online activity. Early detection is key in the fight against credit card fraud. The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage. Rapid response can prevent unauthorized transactions, minimize financial losses, and protect your customers’ trust in your business. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details.

The US dollar was originally minted in deference to the Spanish ‘piece of eight’, the silver dollar, and the quarter was in reference to American’s use of the Spanish two-quarter dollar. Spanish and Mexican currency were in widespread use and legal tender until 1857. Political conflicts raged over the metal content of dollar coins, pegging the dollar to the Gold Standard, and recently the value of a fiat currency in comparison to cryptocoins.
It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected.
Dark Web Scams: Hidden Threats And How Businesses Can Stay Protected
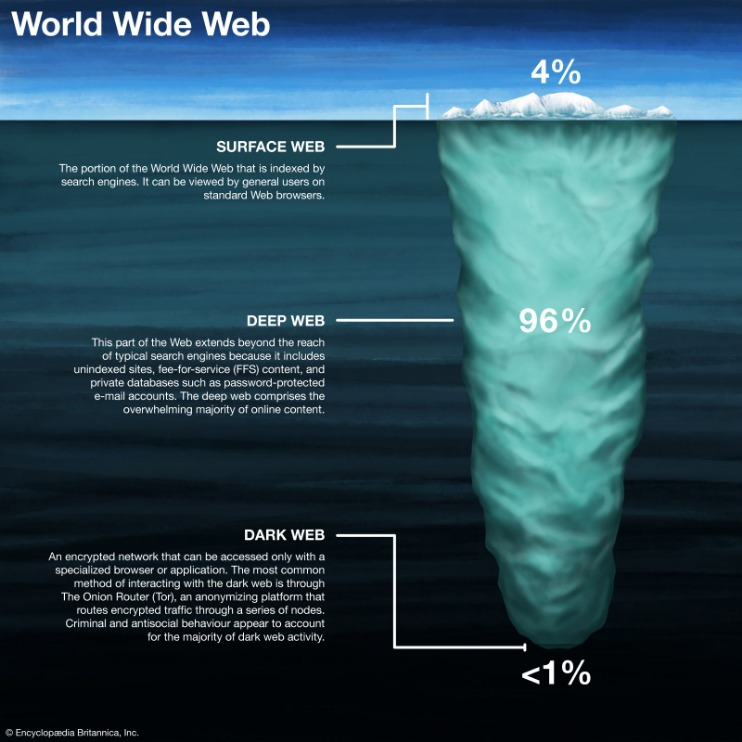
Let us get the most out of this flawed financial system to live the life we deserve. We ensure that issuers throughout the world safeguard their banknotes for the Cash Cycle. The Deep Web contains all the web sites that web crawlers cannot index. Examples of sites on the Deep Web that require a login to access include bank accounts, Netflix accounts, and social media accounts. Other content on the Deep Web include private files like medical records, legal documents, and sites that have blocked search engine crawlers.
The illicit activities of fraudsters are happening across the Gray, Deep, and Dark Web. But the real battle against fraudsters is on the Deep and Dark Web, where tracking their activity is much more difficult. Choosing the right Cyber Threat Intelligence platform can be the best weapon to win the war and protect your organization and customer data. Deploying a CTI solution will allow you to monitor and gather data on what’s happening on the Deep and Dark Web get alerts on activity specific to your organization. For example, many dark web sites, such as gaming forums and online marketplaces, are used for legitimate purposes — and distinguishing between the good and the bad can be difficult without proper intelligence tools. Deep Web sites include private databases, restricted content, and other sources of in-depth information about companies and their operations.
Related Content
Two thousand dollars in counterfeit $100 bills were found hidden in the van and one of the suspects had another $100 in his possession. That doesn’t count what the men had already spent, investigators said. We have simplified the cybersecurity assessment process and made it accessible for all businesses. How much of are risk are you taking for buying counterfeit money? I’m preparing to ship out our new Alsan Wheels line and need a striking, production-ready box design. The contrast should feel premium while keeping print costs realistic.Core branding elements – Our logo (attached) must be the hero.



