Each node decrypts just enough data to know the next destination but not the origin, making tracing...
Uncategorized
If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Always...
BBC is the most popular news source and is the best example of restrictions on International media....
Warmenhoven highlights the danger, pointing out that as long as password reuse continues, these attacks will remain...
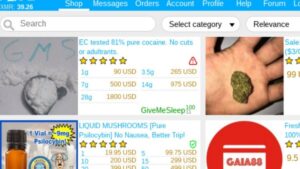
Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look...
For sellers, it’s often about making money while staying off the radar. The first category includes classic...
This way, if you’re interested in a specific topic, you can find it quickly. Radar Rundown Free...
Bohemia’s got a chill community vibe—low fees (1-3%), vendors you can lean on. From digital loot to...
They know how to process the information and get it to the correct law enforcement agencies internationally....
Neither of these require user identification, and provide immediate access to the Network, and users do not...