
Bearing in mind all the dangers, if you’re sure you’re willing to accept the risks, all you need to enter the dark web and access onion sites is an internet connection and Tor Browser software. Borderless news reporting and uncensored media are among the most important and practical uses for the dark web. Bypassing firewalls and other forms of geo-blocking helps people to access news websites and social media they normally wouldn’t be able to — and do so with less fear of recrimination. The various channels focus on stealer logs, combo lists, scam lists, and a community marketplace.
Cyble Strato Cloud Security
This is largely due to harmful elements in the dark web, and Ahmia contains certain questionable and largely illicit links. Therefore, use NordVPN to view search results and browse anonymously. When you access this site, do so with extra protection, even if you are technically anonymous when you use the Tor browser. We highly recommend using a strong VPN like NordVPN to stay safe and private. It’s because the US Navy created Tor for anonymous communication.
NoName057( : Pro-Russian Hacktivism And DDoS Attacks
In 2022, following the closure of RaidForums, a very popular forum founded in 2015, Breached was established in a similar format to RaidForums. To fill the void left by these closures, a new forum called ‘Exposed’ was opened. The forum with a similar theme and name was opened to users, and this brought to mind the question of whether it was a game of the FBI. One of their most well-known contributions is MegaMedusa, a Layer 7 DDoS tool based on NodeJS. What makes MegaMedusa noteworthy is that it enables large-scale attacks without requiring advanced technical skills, making it accessible to anyone with malicious intent. It runs on Debian, Ubuntu, Kali Linux, Termux, and Windows, making it a popular tool in the hacktivist ecosystem.
Check out our list of the best dark web links and how to navigate onion and Tor sites safely. Then get a VPN to help protect your privacy on dark web websites or wherever you browse online. Dark web monitoring and threat intelligence firms like Cyble help mitigate these risks with advanced AI-driven threat intelligence solutions.
Many of these channels operate almost like Dark Web forums, facilitating the exchange of stolen data, hacking tools, and all kinds of illegal services. The Dark Web Hub equips law enforcement, enterprises, MSSPs, and researchers with essential knowledge to navigate dark web threats. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
The New York Times

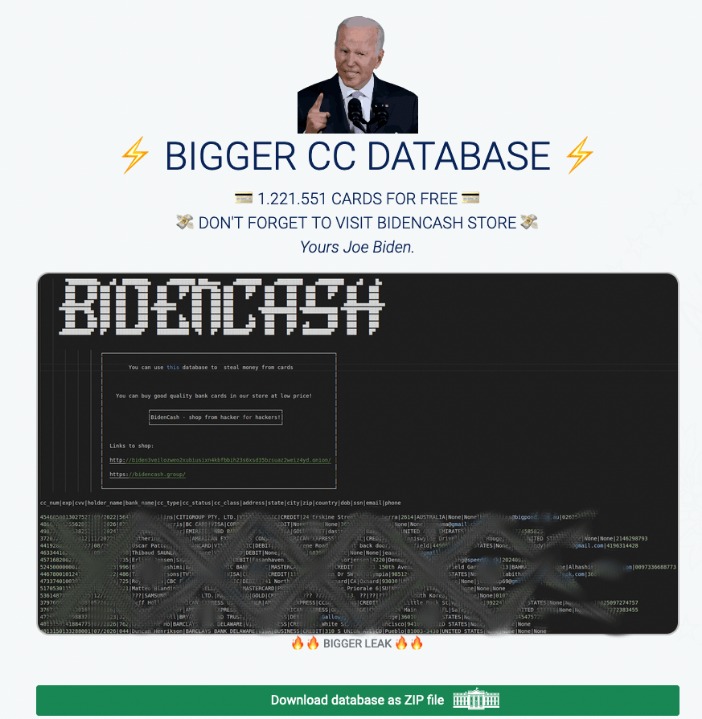
A second major leak of cards relating to Indian banks has been detected by Group-IB, with over 1.3 million credit and debit card records being uploaded to the Joker’s Stash marketplace. Canceling your credit card is a bit more complex, but you can start by contacting your bank or credit card issuer to report the card as stolen. Thieves often buy cards to use on specific sites that don’t have security features like Verified by Visa (VBV) or MasterCard’s SecureCode. You can protect your company with ThreatMon’s dark web monitoring to safeguard your reputation. Dark Storm Team is a pro-Russian and pro-Palestinian hacker group known for its cyberattacks against countries including Israel, France, Egypt, Denmark, the UAE, and the U.S.. They have collaborated with other actors like Anonymous Sudan, launching coordinated DDoS attacks and strategic hacks.
Tor Crypto Wallets
Do note that products are genuine and covered by official warranty. This is another, feature-rich, end-to-end encrypted email service. It even supports “dual-ended removal”, so when you delete an e-mail, it’s deleted from both the sender and the receiver’s database. Now, it’s mostly used by hackers or those who wish to learn hacking. Does let you set the refresh rate, background colour, font colour and a few other settings manually.
WhatsApp Account Hack
Dark.fail is an easy-to-use .onion platform equipped with a status checker that tracks website uptime. The site offers access to PGP-verified URLs and runs free of JavaScript or tracking. This platform’s library of websites currently totals 50, which may not sound impressive until you consider that all the links are active and popular.
Advertising Carding On Legitimate Platforms
The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero. FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels. Bohemia accepts Monero and Bitcoin as payment methods and places a strong emphasis on protecting user anonymity through PGP encryption. Its user base is primarily English-speaking, and it appeals to more sophisticated cybercriminals. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online.
Amazon Gift Cards
- These tools offer consumers the most effective way to defend against carding attacks.
- Yes, governments can still monitor onion sites if they really want to.
- Card data is a hot commodity on the dark web, with credit card details and cloned cards being sold to cybercriminals.
- Our clients have shared positive reviews ⭐⭐⭐⭐⭐ with us about these shops, and our team has also vetted them, so they are 99% trusted.
- It’s your responsibility to understand and abide by local regulations.
Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms.
While other forums became more discreet, RAMP chose to double down and become a central meeting point for those deeply embedded in this type of cyber operation. RAMP enforces extremely strict access policies, with one key requirement being a solid reputation on other well-known forums like XSS or Exploit.in. In other words, if you don’t already have a credible track record, don’t even bother knocking. Our clients have shared positive reviews ⭐⭐⭐⭐⭐ with us about these shops, and our team has also vetted them, so they are 99% trusted.

How Telegram Became A Safe Haven For Threat Actors

According to Radware, bot-driven carding attacks increased sharply due to the rise in digital commerce. E-commerce platforms, streaming services, donation portals, and SaaS tools are especially vulnerable. It’s also important to note that your activities on the dark web aren’t completely immune to web tracking, and the expectation of anonymity can create a false sense of security. You can run a dark web scan to see if any of your data has leaked onto the black market. And if you think you’ve fallen victim to identity theft or fraud, be sure to report the internet scam just like you would any other crime.
Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content. The dark web is part of the internet that is not indexed by standard search engines like Google, Yahoo, and Bing. It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. The biggest and most frustrating part about dark websites is that they live for a short span of time.
Card Shops typically host the trade of credit cards and other stolen financial information, making it easy for cybercriminals to find what they’re looking for. LeakBase, which has an important place for database leaks, emerged in 2023. The forum focuses on database leaks and includes a community that challenges the Breach forum.
The group operates several Telegram channels, the most notable being the DDoSia Project, where they recruit volunteers to carry out coordinated DDoS attacks. In return, participants receive cryptocurrency rewards, incentivizing involvement in these cyber offensives. Your IP is still being revealed to one of the nodes in the onion, meaning your activity and identity can be unmasked. Although profiting from pirated copyrighted material is unethical and illegal, there are some exceptions to using copyrighted material, such as a “private study” provision under UK law. Of course, bypassing paywalls is ethically questionable and may be illegal in some jurisdictions.



