Silent Courier is accessible from Friday and enables a secure avenue to submit sensitive information to the UK relating to terrorism or hostile intelligence activity. The secure messaging platform Silent Courier aims to boost national security by making it easier for the intelligence agency to recruit potential agents in Russia and around the world, the Foreign Office said. The secure messaging platform Silent Courier aims to boost national security by making it easier for the MI6 to recruit potential agents, the Foreign Office said.

Man Jailed For Selling 76kg Of Drugs On Dark Web
The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers.
Is It Illegal To Visit And Use Dark Websites?
Why else would the police in Brazil, Germany, and the United States need to raid dark web e-shops like the Wall Street Market and the Silk Road? Charging the operators with a long grocery list of crimes ranging stolen data, drugs, and malware. These things do happen on the dark web, but they are one piece of the jigsaw.

Others may act in ways that are illegal for the protection and safety of others. Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves. As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online. Abuse and persecution victims, whistleblowers, and political dissidents have been frequent users of these hidden sites.
Can Someone Sell My Data On The Dark Web?
You can also take a look at the blogs & essays section if you want to find some nifty coding resources. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination.
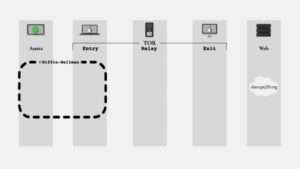
Although data sent through Tor can’t be tracked or decrypted, your internet service provider and network administrator can still see that you’re using Tor. The VPN’s encryption will hide from your ISP the fact that you’re using Tor. After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. Dark net websites are called “Tor hidden services“, and they can be distinguished from normal websites by their URLs.
The Legality Of Accessing The Dark Web
The dark web isn’t something you can just stumble upon, and that’s a good thing. Sites on the dark web can contain potentially catastrophic pitfalls in the form of illegal activity, phishing links, financial scams, and malware infections. There’s also little to no recourse to be had if you encounter any trouble there, because the dark web is a decentralized collection of websites hidden from search engines. It’s the side of the internet that’s used for transactions and conversations that need to stay anonymous. The dark web is a network of untraceable online activity and websites on the internet.
- This means content of such sites isn’t accessible to web crawlers.
- It was initially created to provide additional security and eliminate cryptocurrency theft.
- Unlock continuous, real-time security monitoring with DarkInsight.
- Evidence can be recovered digitally by the police, both from the internal storage of a computer and in the cloud network.
- This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously.
Legitimate Reason Defence
Many young people view their digital self as an extension of their identity and sense of self. Therefore, it’s crucial that we are supporting young people digitally. The range of uses of the dark net sheds light on broader societal challenges intertwined with anonymous online interactions.
Proofpoint Security Awareness And Threat Intelligence: The Perfect Pairing
This layer is intentionally hidden from the general public and can only be accessed with specific software, settings, or authorisation. It’s designed to offer users complete anonymity and privacy for their online activities, which range across both lawful and unlawful spectrums. That may seem an extreme way to browse the web, but such protections are increasingly worth considering, says Sarah Jamie Lewis, executive director of the Open Privacy Research Society. To protect against monitoring, individuals may opt to use virtual private networks (VPNs) to mask their IP addresses and encrypt their internet traffic. VPNs create a virtual tunnel between the user’s device and the destination server, making it difficult for surveillance agencies to monitor their online activities effectively.
- Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see.
- Chairing the first ever cyber COBR after the incident really brought home to me how damaging attacks like these can be and how important cybersecurity is.
- We often hear about the dark web being linked to terrorist plots, drug deals, knife sales and child pornography, but beyond this it can be hard to fully understand how the dark web works and what it looks like.
- Millions of stolen passwords sit on the dark web, meaning your finances and your data is at risk from getting into the hands of fraudsters.
Venturing further into the deep web does bring a bit more danger to the light. For some users, portions of the deep web offer the opportunity to bypass local restrictions and access TV or movie services that may not be available in their local areas. Others go somewhat deeper to download pirated music or steal movies that aren’t yet in theaters. The deep web rests below the surface and accounts for approximately 90% of all websites. This would be the part of an iceberg beneath the water, much larger than the surface web.
Crypto, Digital Asset And AI Advisor,
The Dark Web relies on darknets or networks where connections are made between trusted peers. Examples of Dark Web systems include TOR, Freenet, or the Invisible Internet Project (I2P). Most e-commerce providers offer some kind of escrow service that keeps customer funds on hold until the product has been delivered. However, in the event of a dispute don’t expect service with a smile. Every communication is encrypted, so even the simplest transaction requires a PGP key.
It is crucial to remember that using Tor is not illegal, but engaging in cyber-terrorism or other unlawful activities through it is. You can use Tor to access the surface web since it only provides an encrypted network and transfers your data through random nodes, making it hard to track you. However, the dark web was soon utilized by other groups like drug dealers, weapon traders, and other malicious and illegal corporations, which changed why the dark web was designed.
Just like Google, the dark web has some search engines present on it. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results. SecMail is one of the most popular email services on the dark web. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data.
Given its relationship with crime, some ISPs and companies automatically block Tor traffic. A reference to how Tor works; sending encrypted traffic through layers of relays around the globe as it hides content, the sender, and their location. Users need a special browser with added software to access the tor dark web in the first place. A smart person buying recreational drugs online wouldn’t want to type related keywords into a regular browser. He/She will need to anonymously go online using an infrastructure that will never lead interested parties to his/her IP address or physical location. Drug sellers wouldn’t want to set up shop in an online location whose registrant law enforcement can easily determine or where the site’s IP address exists in the real world, too.