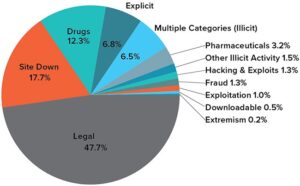
Google considers the majority of the content on the entire web highly irrelevant and useless to its users. That’s why such a large percentage (as much as 94%) of the entire web is not returned in Google Search. There are a lot of misconceptions about it, but we’ll answer that question once and for all in this guide. We’ll also discuss why it’s dangerous and why you should inform yourself about the dark web even if you don’t plan to be on it. Despite its relatively high profile, the dark web makes up a vanishingly small portion of the World Wide Web, perhaps less than 0.01 percent.
Researchers from Recorded Future estimated that while there are more than 55,000 existing onion domains, only 8,400 (or roughly 15%) of these sites were active. So, when measuring the total network of live dark web sites alongside the surface web, only about 0.005% of the internet is the dark web. Illegal drug marketplaces like the Silk Road have been hijacked for police surveillance in the past.
Are Dark Websites Illegal To Use And Visit?
This is because law enforcement often actively monitors these sites. All in all, it is not illegal to access the dark web, but it can create issues for you. If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.

What Is Available On The Dark Web?
By following these tips, individuals can enhance their safety and privacy while exploring the Dark Web. Be aware, however, that there are sites for absolutely everything, from the benign to the very illegal. There are some websites you can absolutely get in legal trouble for even visiting, so proceed with the utmost caution.
Ironclad Cybersecurity
When used in unison, these tools seal the security and privacy vulnerabilities of the Tor network, keeping you anonymous as you roam the streets of the dark web. Valentina Bravo is a managing editor at Cloudwards with a rich background in technology topics, particularly productivity tools and online security. She holds a Bachelor’s degree in Liberal Arts and a triple Master’s degree in Literary and Cultural Studies. Outside of work, she is a travel enthusiast, music lover and avid learner interested in global cultures, spirituality, psychology and neuroscience.
Cyble TIP Threat Intel

But you have to keep your fingers crossed that it remains there and hope the party holding your data (the school or hospital records department) keeps it according to the GDPR standards. With all this data, your ISP could create a very accurate profile of you and link it to your IP address. This is one of the reasons why it is always good to hide your IP address.
Exploring The Dark Web: Understanding Its Role In Cybersecurity Threats
Perhaps some of them are traps laid by the authorities to catch people who try to hire assassins, buy weapons, or acquire counterfeit currency. The dark web is a double-edged sword — full of both potential and peril. As you venture into it, prioritize your safety by using tools like the Tor Browser and VPNs, keeping your security software updated and being cautious with your online behavior. To further enhance your safety, you can use dark web scanners to know if your personal information has been compromised.
How To Remain Safe While Using The Dark Web – Essential Tips

The use of the dark web raises suspicion as it shows there is something you want to do privately. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address.
The history of the Dark Web is intricately tied to the development of internet technology and the ongoing pursuit of online anonymity. The concept of an encrypted, hidden layer of the internet began taking shape in the 1990s. The U.S. Naval Research Laboratory developed the precursor to the Tor (The Onion Router) project during this period as a means to protect government communications. Drugs are typically sold using cryptocurrency to maintain anonymity, and the buyers and sellers are often difficult to trace.
- There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale.
- For Example, In May 2021, authorities in Germany brought down Boystown, a child pornography network with more than 400,000 registered users.
- What’s known as the dark web exists within the deep web; it’s an area of the internet that is only accessible by users who have a Tor browser installed.
- It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.
It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing.
Anonymity is a crucial aspect of the dark web, enabling users to engage in activities without the fear of being identified or monitored. This anonymity can be beneficial for legal activities, such as secure transactions using cryptocurrencies, and for accessing anonymized browsers without breaking the law. However, it also provides a cover for illegal activities, such as cybercrime and the distribution of malware.
Apart from his professional endeavors, Samson is passionate about soccer and enjoys reading, table tennis and watching sports in his spare time. He has also contributed to platforms like Financesonline.com and Timeero.com. Learn effective strategies for conducting threat hunting in your organization. Just because the dark web feels anonymous doesn’t mean it’s invisible—especially to U.S. authorities.
If you are looking to read combating crime on the dark web online, many resources and platforms are available that shed light on the ongoing efforts to curb the growing threats of cybercrime. Unlike the surface web, which can be indexed by standard search engines, the dark web exists on encrypted networks and hosts websites with random, complex URLs. This layered encryption and anonymization make it difficult for authorities or outsiders to trace activities or identify participants. Because of these privacy features, the dark web remains a hidden but active part of the internet ecosystem. Like the regular surface web, the dark web offers its own social media sites and web forums.
- Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses.
- Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow.
- If you decide to visit these marketplaces, exercise extreme caution and remain aware of the legal implications of your actions.
- The Dark Web is the part of the deep web that is not indexed by search engines, like Google or Bing.
- This is why many people prefer an identity theft protection service and a financial and credit fraud protection solution.
- Use the Tor browser, a VPN, and a privacy-focused operating system like Tails to ensure anonymous browsing.
Dark Web Versions Of Clear Net Sites
Also known as The Onion Router, TOR enables users to browse the Internet, including the Dark Web, anonymously. It bounces traffic through several servers before delivering it to its destination, making it harder to track a user’s activity or location. When venturing into the dark web, it is crucial to prioritize safety by educating oneself about potential risks and employing robust security measures to protect data and maintain privacy. The dark web’s hazards include many risks, related to network breaches or data compromises. These range from infections, unauthorized access, espionage, and phishing, to the theft of sensitive information like customer and financial data, intellectual property, and more. Each category carries risks of devaluing enterprises through reputational damage, disrupting operations via malware attacks, or defrauding companies through theft of critical information.