By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. AiPrise uses document verification, biometric checks, and data cross-referencing from over 800 sources to spot fake or manipulated identities. It helps businesses catch fraud early, meet compliance requirements, and streamline customer onboarding. Yes, with the right identity verification tools that include biometric checks, document verification, and real-time data matching across trusted sources.
How To Protect Your Personal Information From Fraud

It ensures the buyer’s identity is kept hidden and accepts payments through cryptocurrencies, including Bitcoin, Litecoin, Ethereum, and Monero. Awazon Market is a top-tier dark web marketplace with claims to revolutionize secure anonymous commerce. It offers a wide range of goods and services with robust anti-DDoS protection (with military-grade security protocols) and no JavaScript, ensuring privacy and uptime. These listings often include detailed descriptions, user reviews, and even shipping guarantees. Law enforcement agencies monitor many dangerous markets, and even anonymous browsing isn’t foolproof.
How Do Scammers Get Digital Identity Information?
Visit CyberNod and take the first step toward a secure digital future. This structured process ensures security while maintaining the anonymity of both buyers and sellers, making Dark Web marketplaces a persistent challenge for cybersecurity enforcement. Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins.
By implementing strong cybersecurity measures, SMBs can comply with cybersecurity regulations and safeguard their operations from Dark Web-related threats. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment.
Building The Future: Why The World’s Smartest Businesses Choose Digital One Agency
Brian’s Club has been around since 2014 and remains one of the most well-known credit card shops on the dark web. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks. Despite multiple takedown efforts by law enforcement and security researchers, Brian’s Club has resurfaced repeatedly and continues to add new stolen credit card data.
Digital ID Fraud And Black Market: A Comprehensive Guide
Beginning in September 2021, Abacus Market has established itself as one of the leading dark web marketplaces. After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces. Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals. Moreover, engaging in the trade or use of fake documents supports criminal networks involved in identity theft, human trafficking, terrorism, and organized crime, thereby harming innocent individuals and undermining social trust and security.
- He said, the low end of your guidelines is three years and the high end is five years.
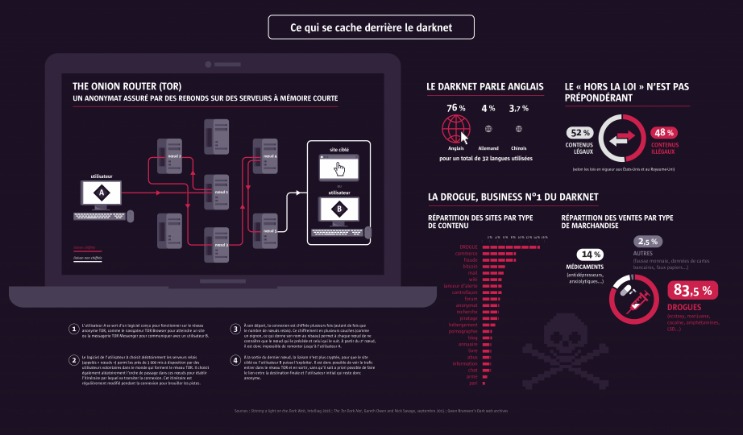
- Most buyers and sellers use the Tor network, which hides IP addresses and locations.
- The website has an interface and design similar to other dark web shops.
- Additionally, companies can also protect customer accounts from being hijacked by criminals by doubling up security protection through 2-factor authentication.
- For businesses, the cybersecurity risks posed by Dark Web marketplaces are substantial.
- Hidden in the back alleys of the “darknet” are the identity forgery professionals who churn out counterfeit ID documents sold in the hidden internet found on The Onion Router (TOR) networks.
What Can Criminals Do With Stolen Identity Data?
All dark web data and prices were pulled from SafetyDetectives’s dark web research team. If you want to increase the level of security across your desktop and mobile devices, read through some of our top antivirus, anti-spyware, and password manager reviews, including Norton, Dashlane, Bitdefender, and Malwarebytes. As you become increasingly connected to the digital world, it’s important to stay vigilant and aware of all the invisible dangers hiding on the web. Among the education documents that can be purchased via the dark web are high school diplomas, bachelor’s degrees, and master’s degrees. Fixing poor grades is also a common service offered — a D-grade student could have their entire profile changed to all A-grades.
Revolutionizing Paper Personalization With PaperProtectTM
Undercover agents create convincing fake profiles, interact with criminal vendors, and conduct controlled purchases. These interactions help law enforcement track the identities and operational tactics of criminal organizations. Individuals purchase fake IDs and other fraudulent documents for a variety of reasons.
Silk Road quickly grew into the largest darknet market, handling hundreds of millions in transactions. But in 2013, law enforcement traced Bitcoin activity, monitored DPR’s forum posts, and exploited server vulnerabilities to identify Ross Ulbricht. He was arrested in a San Francisco library while logged in as site admin. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange.
- (Trento University) and an MA in Global Criminology (Utrecht University).
- In 2022, for example, BidenCash was linked to the breach of over 1.2 million credit card records.
- We understand the curiosity to venture into the dark web, but you also need to understand that it’s never safe to venture into this portion of the internet without fully understanding what it entails.
- Second, game-theoretic models could extend the prisoner’s dilemma framework to incorporate repeated interactions, exploring how frequent use of fake IDs alters the behaviors of both students and bouncers over time.
- Even passive activity on these sites can contribute to criminal networks.
Sellers establish trust through a rating system, similar to legitimate e-commerce platforms, where buyers leave feedback on product quality, delivery speed, and communication. Some vendors offer “stealth shipping” guarantees, ensuring products are discreetly packaged to avoid detection. A dark web search engine like DuckDuckGo offers impressive anonymity features and makes it easy to access the shops. These search engines neither track your search queries nor record any information, improving digital privacy and keeping your data private.
A dark web market is a hidden online platform where users can anonymously buy, sell, and trade illegal or sensitive items. Such markets are typically accessible through the Tor network, which anonymizes traffic by routing it through multiple relays and encrypting each layer. This encryption makes attribution and tracking more difficult for authorities and cybersecurity professionals. Organisations should follow industry standards on securing data and implement security technologies to prevent cyber attacks and reduce the risk of data being stolen and traded in the darknet markets.
Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. In 2024, the platform grew significantly in popularity, partly because of its strategic acquisition of users from a number of recently shut-down marketplaces, such as AlphaBay and Incognito Market, which had recently closed their doors. The cost of buying a counterfeit Australian passport via the dark web starts at US$660, and a counterfeit Australian driver’s license starts at US$420. This is a substantially higher combined average than any other country’s identification cards. ID cards and driving licenses start at US$200, and a brand new Social Security Card/Number costs between US$2 – US$5. Our researchers discovered that passports advertised as “registered”, “authentic”, and “verifiable” were expected to be genuine and, as such, demanded more money.
Educational campaigns have begun emphasizing the unintended consequences and hidden harms of such seemingly harmless infractions, advocating a shift in societal attitudes towards greater ethical responsibility and adherence to legal standards. Due to the cross-border nature of cybercrimes, international cooperation is essential. Department of Justice frequently collaborate to share intelligence, coordinate simultaneous operations, and ensure effective prosecution of criminal actors across jurisdictions. Use anti-virus software such as AVG on your personal computer to scan for malware and make sure that it is set to update automatically. If you need to log in to an account on a network you don’t trust, such as a coffee shop, use a VPN to encrypt all connections. The high value of accounts combined with the abundance of BTC ATMs for anonymous cashing makes cryptocurrency accounts a very valuable target for hackers.
Attackers pull this information from various sources, often without needing to breach anything themselves. Prices depend on how complete the identity is and how easily it can be used to open accounts, apply for loans, or pass KYC checks. Yet, even seemingly minor infractions have ripple effects, leading increasingly to public calls for stronger enforcement and accountability.