There are some supposed ‘dark web’ search engines like Torch or Haystak is said to have indexed more .onion sites than any other search engine. While it is not flawless in protecting user privacy, it works well enough to give users much more privacy in where they go, the content accessed, and protecting their identity and location. The multiple relays help keep some distance and anonymity between the person visiting the website, the website itself, and any entity trying to eavesdrop on the communication between the two. Several secure email providers, such as Riseup and Mailbox.org, provide onion sites for users who want to add an extra layer of privacy and anonymity to email communications.
Table Of Contents

When you visit dark web sites, even if you don’t have any ill intentions, you support the dark web ecosystem, which serves as a medium to conduct various illegal activities. As dark web websites are not moderated, they can host a wide range of malware, such as ransomware, keylogger, and remote access Trojan. You can inadvertently download malicious software by visiting these websites, infecting your system. The dark web exists to provide users with anonymity and privacy on the internet.
What Is The Dark Web? How It Works And How To Stay Safe
Always exercise extreme caution when using publicly posted onion URLs. If you can’t get a personal recommendation from someone you trust, verify the URL from multiple sources. The dark web, or dark net, is a small part of the deep web that is kept hidden on purpose. Websites and data on the dark web do typically require a special tool to access. For the open web, just type your name into Google and see what comes up. Whether this is a Linkedin profile, Facebook, social media, or any community involvement, chances are that you already have some online presence.
Stay Away From Questionable Sites
- The topics you can find vary from literature, programming, science, and….artistic photography.
- In this article, we will unpack everything you should know about what the dark web is, how it works, how to surf it safely, and more.
- Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble.
- This service is a good source of statistics if you have a school project requiring research on Tor and the dark web.
- The threat can extend to your entire network of devices connected to the internet.
There are huge numbers of such pages, and most exist for mundane reasons. Hackers stole the data and threatened to upload it to the web if the site did not close down, and they eventually acted on that threat. The spouses of Ashley Madison users received blackmail letters demanding they pay $2500 in Bitcoin or have the infidelity exposed. When you purchase through links in our articles, we may earn a small commission. We have simplified the cybersecurity assessment process and made it accessible for all businesses.

Strengthening Your Digital Hygiene
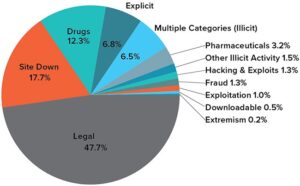
The “surface web,” on the other hand, is the publicly available part of the internet that search engines index. Dark web, websites not indexed by search engines and theoretically possible to visit with complete anonymity. The dark web is a small segment of the deep web that has been intentionally hidden and is inaccessible through standard web browsers. Unlike the surface web, which is indexed by search engines like Google, the dark web requires specific software like the Tor browser for access.
Dark Web Search Engine
In addition, the content on the pages don’t need any special or custom configuration to access. It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries. Did you know that Google only shows you a glimpse of all the websites that actually exist? The last time I checked, it’s estimated that the entire web is roughly 500 times larger than what Google returns in Google Search.

Torch – Oldest Tor Search Engine
This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. This type of government surveillance applies mostly to countries with environments that are hostile to free speech.
Rely On Secure Browsers (eg, Tor)
Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. But human trafficking, illegal pornography featuring underaged victims, money laundering, and assassinations are also examples of the darkest corners on the dark web. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. Typically, any reference to the visible web will be to common websites with a familiar internet domain extension. Google considers the majority of the content on the entire web highly irrelevant and useless to its users.
Do I Need A VPN If I Use Tor?
People use the dark web for both good and bad, but generally speaking, it’s used for activities requiring a high level of anonymity. To properly peel back the internet’s layers, you need a tool that provides layers of encryption to hide your activity. Tor Browser is a tool created and maintained by a non-profit privacy group, and it uses onion routing to repeatedly encrypt data and route it several times before it gets to its expected destination.
It encrypts your traffic right away, which is beneficial if you don’t want your ISP to see you’re using Tor. Some countries frown upon dark web usage, so it’s good to have your back covered by a reputable VPN service. This allows you to go online anonymously and without ISP monitoring. The key is to encrypt your traffic BEFORE you use Tor so that your ISP (Internet Service Provider) doesn’t see you’re in the Tor network. The entry node encrypts your traffic and it bounces across several nodes in the Tor networks until it reaches the exit node.
The darknet version of DuckDuckGo is not a search engine for the dark web, but a private browsing tool for the dark web. DuckDuckGo’s regular site can take you to the dark web, as it brings up onion sites and dark web links when searched. Neither DuckDuckGo’s dark nor normal versions keep a log of your web activity. To find .onion links for dark web sites, you’ll need to use a dark web search engine. Many of them are safe for beginners to use since they filter out dangerous/illegal content to only provide safe .onion links. My favorites are DuckDuckGo (usually the Tor browser’s default search engine), The Hidden Wiki, and Ahmia.
This is the standard internet you use daily on your phone, computer, smart TV, and IoT devices. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. It has a bidding feature, with new batches of stolen data being frequently added. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. Never log in with your real name or reuse passwords from other accounts.
Your access to illegal content, even if it is unintentional, can violate laws in many countries. I2P, or the Invisible Internet Project, is an anonymous network layer to facilitate secure and private communication among its users. It works as a decentralized, peer-to-peer network that emphasizes censorship resistance and complete anonymity. Dark.fail is an easy-to-use .onion platform equipped with a status checker that tracks website uptime.