When engaging in online activities over Tor, refrain from providing identifying information, including your name, email address, or financial details. Create new handles or pseudonyms to protect your identity throughout your online engagements. By the late 2010s, a myriad of platforms allowed users not just illegal goods but also forums for activism, whistleblowing, and even genuine speech that found little outlet in conventional media. You can find helpful free dark web books online if you search terms like Dark web books pdf, Dark web book pdf download, or The Truth Book Dark Web. You can use the dark web safely using the right tools, including a VPN and Tor browser. These technologies have security features designed to keep you safe on the dark web.
Dark Web 101: Your Guide To The Badlands Of The Internet
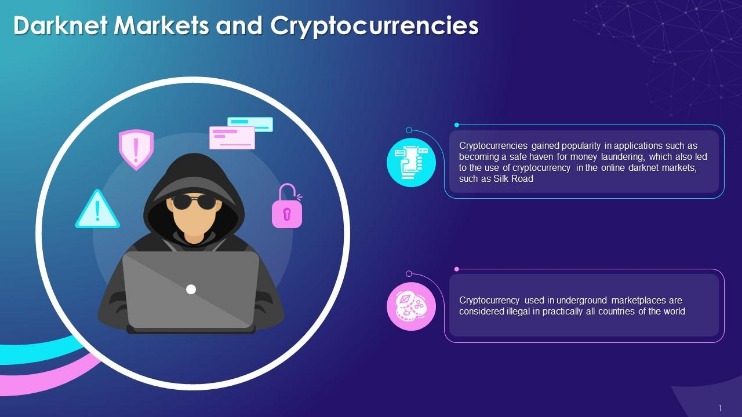
MGM is in a continuous state of development, with a focus on enhancing user experience. You can use a dark web scan tool to tell if your data has landed on the dark web. The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. Some believe STYX is the OG darknet market when it comes to financial crimes. It trades in hacked bank accounts, stolen credit card information, and other services that facilitate cryptocurrency laundering.

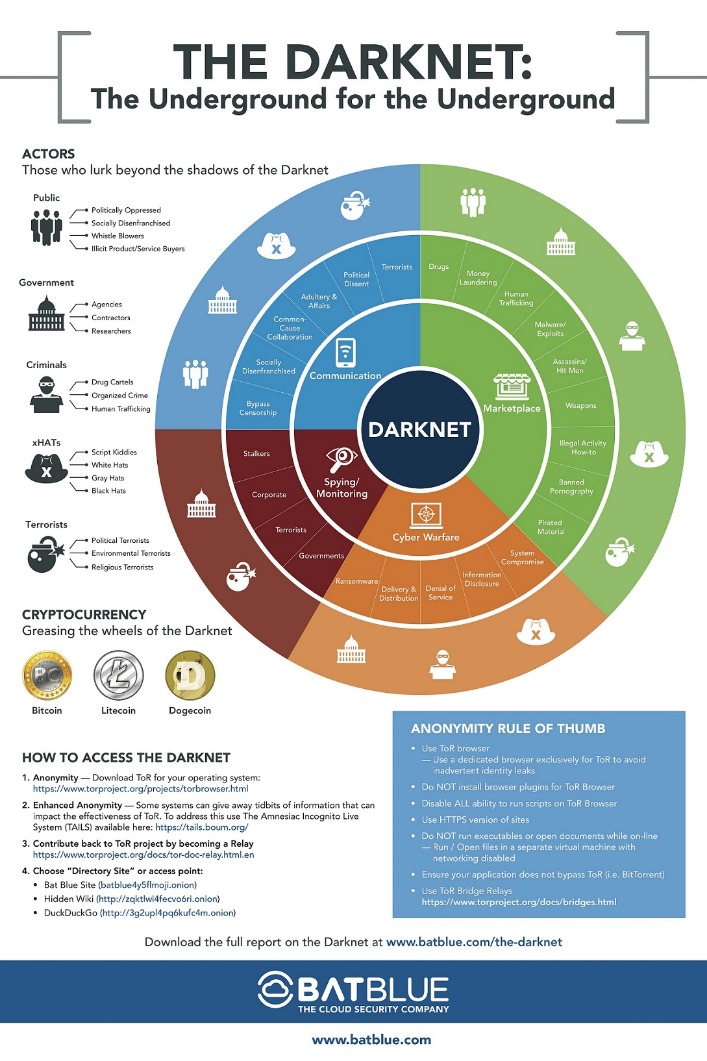
Accessing The Darknet
It’s hard to estimate just how big the deep web is, but the commonly cited research (albeit from 2001) puts the deep web at 400 to 550 times the size of the “surface web.” And with the rise of bitcoin, the “currency of choice” on the dark web, virtually anonymous payments are easier than ever. However, it’s very difficult and would require extensive resources, meaning that the average person’s identity is unlikely to be uncovered.
Q: Should I Use A VPN?
Individuals who blow the whistle, known as whistleblowers, play a crucial role in promoting transparency and accountability, often at significant personal risk. They may expose various issues, ranging from corporate fraud to governmental misconduct, in hopes of fostering change and ensuring the public’s right to know. While this method provides iron-clad data security and total online privacy, it significantly lowers website loading times. Nevertheless, you can use a secure VPN to maintain speeds similar to your regular browsing speeds.
Legitimate Uses For The Dark Web
- Tor says plenty of “normal people” use its service, as well as citizen journalists, whistleblowers, law enforcement agencies and, according to Human Rights Watch, Chinese dissidents.
- Operational security, or OPSEC, is the discipline that turns technical anonymity into real‑world protection.
- You don’t need special tools or a dark net browser to access most of the deep web; you just need to know where to look.
- Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine.
- However, before you start your search, toggle the button beside “Onionize” to anonymize your session.
- Other than the most popular markets, you won’t really find, for a lack of a better word, the “good stuff” on the Darknet unless you already know where to look or who to ask.
They will only get you into big legal trouble if you do not use them correctly. For added security, consider using a reliable VPN in conjunction with Tor. A VPN can mask your Tor usage from your Internet Service Provider (ISP), but be cautious — some VPN providers keep logs that could compromise your anonymity. Thus, what started as an intriguing experiment with anonymity has transformed into a multifaceted realm, serving both the liberation of voices silenced and the shadowed dealings that we pursue.
As we mentioned at the beginning of this article, your regular browsers won’t take you into the dark web. You’ll need a browser like Tor to gain access to the underworld of the Internet. This book is a great choice if you want a detailed tutorial on how to use Tor for the dark web. It takes you through the setup and how to use the software to evade surveillance by prying eyes. Award-winning journalist Evan Ratliff spent nearly five years piecing together the uncommon story.
Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously). Although the official Tor Project advises against VPN over Tor, both methods are superior to not using a VPN at all. Tor over VPN also doesn’t protect users from malicious Tor exit nodes. Because Tor nodes are made up of volunteers, not all of them play by the rules. The final relay before your traffic goes to the destination website is known as the exit node.
If you want to access the Tor network on your iPhone or iPad, you can use the Onion Browser app. The mobile app uses DuckDuckGo as its default search engine and is supported by the Orbit framework to provide secure access to the Tor network. The Tor network is operated by thousands of volunteers worldwide who maintain the proxy servers that protect your identity. You can download the Tor Browser for Windows, MacOS, Linux, and Android. ZDNET tested the best VPNs available based on speed, number of servers, security features, price, and more. ExpressVPN is our pick for the best VPN overall, thanks to its fast and reliable connection and the wide range of platforms it works on.
Why Use The Reddit Darknet Market List 2024?
There exists a hidden underworld of the Internet that’s anonymous, lawless and uncensored. Whistleblowers, activists and political dissidents certainly have good reason to obscure their online location and post with anonymity on the dark web, but that level of secrecy is also sought by criminals. Europol says the dark web and other peer-to-peer networks are still the “main platform” for sharing child abuse material.
Whistleblower Platforms And News Outlets
All ISO publications and materials are protected by copyright and are subject to the user’s acceptance of ISO’s conditions of copyright. Staying ahead of cybercriminals requires more than reactive measures; it demands a proactive, systematic approach built on continuous improvement, risk awareness and adherence to proven security protocols. By integrating top-grade security into their operations, organizations can not only reduce their exposure to cyber threats but also reinforce trust in an increasingly data-driven world. As cyber threats grow more sophisticated, organizations are keeping a close watch on the dark web. Companies use dark web monitoring to scan for leaked data, stolen credentials and breach indicators, helping them track and identify perpetrators.
Archetyp was founded in May 2020 as an online marketplace to facilitate the illicit drug trade.17 It did not host other black market listings such as those for firearms or prostitution. Keep in mind that while Tor anonymizes your browsing activity, it is not foolproof. Major entities (like governments or large corporations) may still analyze traffic patterns. Always remain vigilant about the risks involved with risky behavior, even when browsing through Tor. Malicious files might bypass Tor’s security, giving away your real IP address. If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine.
You won’t be able to search the dark web with a regular browser (such as Chrome or Firefox). Besides, your online activity on such browsers is visible to your ISP unless you connect to a VPN service. As such, you should exercise caution when accessing any unofficial dark websites. Then there’s the less popular VPN over Tor, which is advised against by the official Tor Project. Only two VPN providers that we know of, AirVPN and BolehVPN, offer this service, although neither of these score highly for speeds.
The content of all these pages is stored on Google’s servers, but it’s mostly outdated, old content; smartphone app content; journals; court records; private social media profiles, and much more. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details. It’s something built into the password management services offered by Apple and Google as well, so you don’t need to trawl through data leaks manually yourself. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet. However, it’s much harder to get at the people who are doing the uploading and downloading.
Use Secure Communications
Ever since Silk Road went down, several dark web marketplaces have kept coming and several of them shut down again. To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents. The significance lies in the potential compromise of national security. Governments and businesses must invest in advanced threat intelligence, cyber defense, and counter-espionage measures. In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described.
The Legality Of Accessing The Dark Web
Tor and VPNs mask your network path, but a single careless click can still expose your identity. Tails (The Amnesic Incognito Live System) is a Linux‑based operating system that boots from a USB stick and routes all traffic through Tor. It leaves no forensic trace on the host computer, resets to a clean state at every reboot, and includes VeraCrypt, KeePassXC and OnionShare for secure file handling. Use Tails when the stakes—journalistic work, whistle‑blowing, sensitive research—justify a fully compartmentalized environment. Our guide also covers the role of cryptocurrency in the dark web ecosystem. You’ll discover the most commonly used cryptocurrencies, such as Bitcoin and Monero, and learn how to securely manage your wallets and transactions.
Why You Need Tor Browser?
Most people think this is THE Internet, the all encompassing World Wide Web. To the uninitiated this makes sense, hence it’s also known as the “Visible Web”. This is a mini-series of posts about the hidden, anonymous and dark part of the Deep Web. While browsing online, you might have noticed that the websites you are visiting have URLs starting … With online surveillance and data tracking keep increasing, protecting your identity and data online… Then, a law enforcement agency (still unidentified) provided information to the FBI that later accessed the site’s host server.



