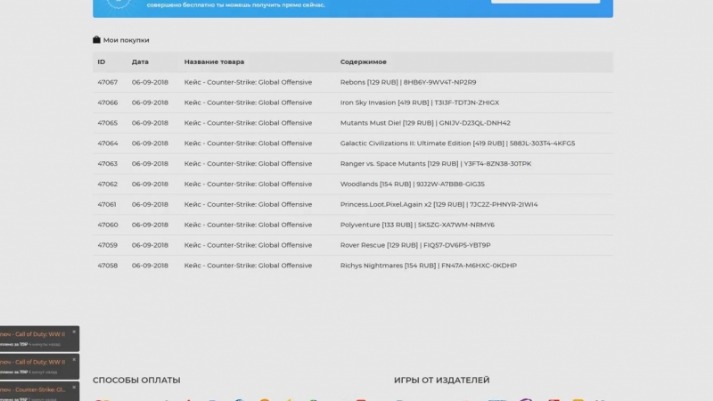
For example, drug dealers can use darknet markets to sell drugs without the risk of getting caught, and weapons dealers can sell guns and other weapons without needing a license. The growing popularity of these platforms is driven by their ability to offer a wide range of products, from pharmaceuticals to recreational substances, catering to diverse user needs. The use of darknet market lists and URLs has further simplified navigation, allowing users to quickly find trusted vendors and products. The growing popularity of darknet drug markets is also driven by their ability to adapt to user demands. Vendors frequently update their inventories, ensuring that the latest products are available.
Efficient And Secure Drug Trade On Darknet Markets In 2025
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
What Types Of Content Can I Find On Dark Web Marketplace Links?
This is the best place to get short and reliable links to an unalterable record of any webpage across government and corporate websites. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events. Even without monitoring your browsing activities, DuckDuckGo will offer decent answers to your questions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
Latest Rumors & News
If you’re seeing this message, access is restricted for regular browsers. Tor was oficially deployed in October 2002 and its source code was released under a free and open software license. Your traffic passes through 3 intermediate nodes before reaching destination. Each of the 3 nodes has separate layer of encryption and nobody who watches your connection can read what you send and where.
Importance Of Escrow Protection
Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Navigating the depths of these hidden services requires specialized tools and a cautious approach. The Tor Browser, a modified version of Firefox, is a common gateway to these services. It routes traffic through multiple layers of encryption, masking users’ identities and locations. For additional security, many users employ virtual private networks (VPNs) to encrypt their internet traffic. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records.
Exploring The Dark Web: What Are onion Links?
Sign up for free credit monitoring to get alerted when there are unexpected changes in your credit report, which could help you quickly respond to some types of fraud. Additionally, an identity theft monitoring service, such as Experian IdentityWorks℠, will look for your personal information in more databases and on the dark web. It also comes with identity theft insurance, which can help cover the cost of recovering from identity theft. Anyone can archive or retrieve data on any site they want, wherever available. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs.
Newsletter
As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. Keybase is a fantastic onion website that lets you cryptographically bring your different online identities together. Look no further if you want good music while navigating the dark web. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
The Darknet Landscape In 2025

Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee. The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities.
This means that there is no guarantee of quality or safety when buying goods or services on a Tor market. Darknet Markets are online marketplaces where people can buy and sell illicit goods and services under the protection of the anonymity by TOR. The products that are most commonly listed for sale include drugs, fake documents, fraud-related items, and hacking services and tools.
- Darknet Markets List 2021 Darknet markets are the name of the hidden portions of the World Wide Web that is not accessible with a darknet market lists traditional web browser or.
- Note that some features of the normal website are not available on the .onion version, including BBC iPlayer.
- Apart from the dark web markets that are operating online today, some raided platforms influenced many markets.
- NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites.
- Unlike the surface web, it’s not indexed by traditional search engines, making it a haven for anonymity seekers.
The Private vendor shop of JesusOfRave – Old time vendor selling LSD & MDMA. So you’ve downloaded the Tor browser to your device and now you’re ready to start exploring the dark web? This guide will ensure you’re good to go in no time with these 3 simple steps.
These resources allow users to access verified platforms that prioritize security, anonymity, and reliability. The best darknet markets are characterized by their robust encryption protocols, transparent vendor ratings, and diverse product offerings. Check out our list of the top dark web search engines and learn how to access the dark web safely.
It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Onion links have no regular domain names registered under the domain name registry.