Alongside the obvious sensitive data pertaining to the cards, the dump includes personal information as well, including email addresses, phone numbers, and the address of the card holder. As for the credit cards, the file itself features cards with an expiry date from 2023 to 2026. Credit card theft is typically proven through evidence of unauthorized transactions, often identified by the cardholder or through the bank’s fraud detection systems. As a result, consumers need to be vigilant about protecting their credit card information and take necessary precautions to avoid falling victim to these scams. In this article, we delve into the dark side of credit cards and their entanglement with the sinister world of the Dark Web, shedding light on the dangers that lurk beneath the shimmering façade of convenience and ease. Prepare to be astounded, as we unveil the chilling reality that lies beyond the bright glow of your credit card statement.
Understanding Credit Card Fraud On The Dark Web
In this shadowy realm, hackers can obtain credit card details through various means, including phishing campaigns, malware attacks, and data breaches. Credit cards and the dark web pose a significant threat to individuals and their financial security. The dark web serves as a marketplace where stolen credit card information is bought and sold, fueling illegal activities. Cybercriminals exploit vulnerabilities in payment systems, compromising credit card details. Once obtained, this information is used for identity theft, fraudulent purchases, and money laundering. Once obtained, these stolen credit cards are quickly sold on the dark web, where they can be used for fraudulent transactions or identity theft.
- Researchers are still looking into the leak, but early reports show many of the cards could have already been reported to the card issuers.
- Criminals can easily sell stolen credit card information to other malicious actors on the dark web, leading to potential financial devastation for victims.
- To minimize the risk of payment data exposure, only shop from reputable retailers, use digital payment methods or one-time private cards, and protect your accounts with two-factor authentication.
- Next, let’s explore how individuals can access the Dark Web safely, while minimizing personal risks and vulnerabilities.
The intelligence gathered from these markets helps security teams predict and prevent future attacks. I’ve investigated too many breaches where malware jumped from an infected office computer to the payment network. Network segmentation is absolutely critical for businesses handling card data.
Ready To Explore Web Data At Scale?
You can also share your virtual card details with family members without revealing your underlying bank information. This can be especially useful for parents wanting to manage their children’s online spending with full control of the card settings. Millions of customers’ card data have been compromised in the past decade. No matter how vigilant you are, there is nothing you can do to prevent a data breach on a merchant’s website, but using a virtual card can shield your actual card data from being exposed. It’s easy to lose track of transactions on your credit or debit card, especially if you use multiple cards. You may not notice your credit card has been compromised until it gets declined or you start receiving monthly bills for transactions you never authorized.
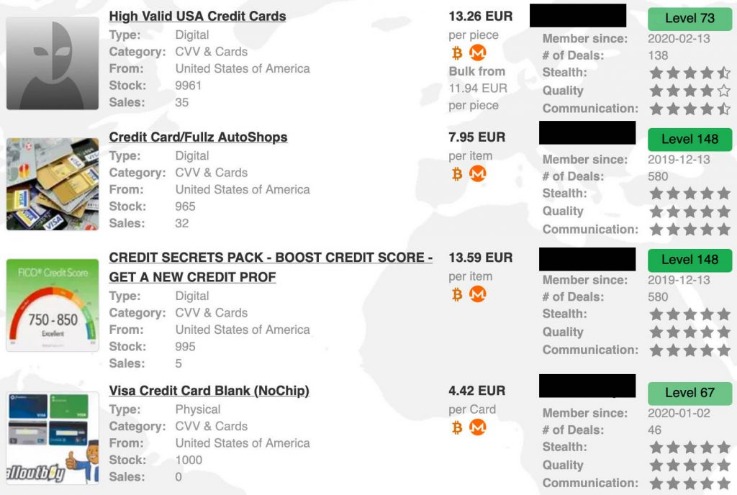
The Price Of Stolen Info: Everything On Sale On The Dark Web

Remember, while evaluating seller feedback and ratings can provide valuable insights, engaging in credit card transactions on the Dark Web is illegal and carries significant risks. It is essential to proceed with caution and prioritize personal security and ethical considerations. Stolen credit card details are sold for a fraction of their actual value, making it an attractive option for fraudsters looking to finance their criminal activities. The dark web is part of the internet that is only accessible using a specific browser called Tor. The dark web offers individuals who access it anonymity and secure communication channels that cannot be found using standard search engines like Google, Yahoo or Bing. Since the dark web provides its users with anonymity, cybercriminals often use it to carry out criminal activities like trafficking stolen personal information and selling illegal weapons.
Is My Credit Card Number Secure Once I Share It For Monitoring?

There are entire websites, channels, and forums dedicated specifically to carding. Unlike other types of stolen data—such as email lists or personal information—carding exists as its own distinct niche within the cyber crime ecosystem. Stolen credit card details are often sold on platforms and websites dedicated to, and branded as, carding websites. It is crucial to approach the Dark Web with caution and fully understand the risks involved.
“By the time the data is in the underground, it’s gone through a number of stages to get there. So … how do we stop the data from ever being exposed or compromised in the first place, before it can be accessible by any criminals? … That’s’ where things like 3DS 2.0 and tokenization really come into play. So that if data is potentially compromised at an e-merchant site, for example, that data has no value if it’s compromised,” he explains. Traveling with a credit card exposes you to risks like fraud or unauthorized transactions.
Dark web posts and offers of this size are usually scams, so the massive dump of cards could easily be fake data or recycled data from old dumps repackaged under a new name. To ensure larger reach, the crooks distribute the collection via a clearnet domain and on other hacking and carding forums. The most expensive card details, which cost about $20, were in Hong Kong and the Philippines and the cheapest, some at just $1, originated in Mexico, the US and Australia.

Where Is Credit Card Theft Taking Place On The Deep And Dark Web?
The expiration for most cards reviewed by BleepingComputer ranges from 2025 to 2029, but we also spotted a few expired entries from 2023. “There are sites out there where they ‘rack and stack’ them, and say how much exactly a specific card is worth,” agrees Wilson. Privacy is a BBB®-accredited company with a dedicated customer support team. As a company handling sensitive payment data, Privacy complies with PCI-DSS protocols and exceeds additional industry security standards to ensure the safety of your data. Telegram carding groups have become a significant threat in the cybercriminal community, with tens of thousands of members easily accessible through the chat application. Stolen card details often end up on the dark web marketplace for a quick profit, and this can happen before you even know about it.
Someone With Access To Your Card Uses It Without Your Permission
Follow our recommendations to secure your information, such as notifying your bank and updating security settings on your accounts. If your credit card number or other details are detected on the dark web, you will be immediately alerted, allowing you to take protective measures. The key is catching this activity before large volumes of card data make it to market. The average price of a cloned, physical card is $171, or 5.75 cents per dollar of credit limit. This time, the leaked data contains card numbers, expiration dates, and three-digit security codes (CVVs).
Dark web transactions play a key role in fund transfers for credit card fraud. Cybercriminals use cryptocurrency to buy and sell stolen card data anonymously. Our investigation into the activities of b1ack’s Stash has unveiled a substantial threat to the security of payment card data across local banks. Analysis of the leaked data, likely sourced from phishing campaigns, suggests a high probability of the validity of these stolen cards based on the available information. A significant portion of this data was uniquely identified in our intel collection.
Methods Used By Criminals
So, if you are curious about the mechanics of the Dark Web and how credit card transactions take place in this hidden realm, read on to discover the secrets of this nefarious underworld. The credit cards could come from multiple sources, including from malware forced into online shops, individual user malware attacks, or from breaches of companies who store credit card info. For example, hackers may sell credit card information in bulk, allowing others to commit fraud and financial theft.
Verified by Visa is a service that prompts the cardholder for a one-time password whenever their card is used at participating stores. “It is conceivable that the data was shared for free to entice other criminal actors to frequent their site…by purchasing additional stolen data from unsuspecting victims,” according to the post (machine-translated from Italian). Join us as we break down and discover the methodologies of card fraud using our dark web monitoring tool, Lunar.
Free 1 Million Card Leak Marketing Strategy
Credit card info is often used to steal your identity and could be linked to other personal data. Monitoring helps protect your identity by detecting any compromise early on. A second major leak of cards relating to Indian banks has been detected by Group-IB, with over 1.3 million credit and debit card records being uploaded to the Joker’s Stash marketplace. Canceling your PayPal account or credit card is a crucial step in preventing further unauthorized transactions. Here are some tips to keep your credit card information safe from compromise in the future. Here are the steps to take after discovering your credit card information is on the dark web.