Instead, it is funneled through different ‘nodes’ – other user’s computers – before coming out the other side. These computers are all owned by volunteers, passionate about privacy and happy to offer up their device to help others. Traffic is relayed through three nodes each time it passes through the Tor network.
Your Data Can End Up Landing Anywhere
Tor has an in-build slider which lets you adjust the level of security. This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. Hidden Facebook is hardly the only social media client on the dark web. The major issue with these websites is that a whopping 50 percent are fake, and there’s no way of telling for sure if they’ll deliver or not. At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen.
The dark web presents various threats, including malicious software and computer viruses, posing risks to users’ systems and data security. Users also face the potential danger of government monitoring and surveillance — or scams and fraud, and other activities that can lead to financial loss and identity theft. The dark web is home to the internet’s hidden sites, services, and products — some innocent, others downright dangerous. Read on to learn the pros and cons of the dark web, how to access it, and get tips for staying safe. Then, install Norton 360 Deluxe to get AI-powered scam detection to help secure your browsing against online threats.
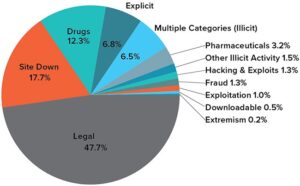
Dark Web Sites
The deep web is crucial for maintaining privacy and security online, as it keeps sensitive information away from the prying eyes of the public and search engines. While the term “deep web” might evoke images of hidden, secretive content, most of it is just routine data stored on private networks. The surface web is the part of the internet most of us interact with daily. It includes all the websites and pages that are indexed by search engines like Google, Bing and Yahoo.
Engaging in illegal activities can lead to severe legal consequences, including criminal charges. Therefore, it is important to have a legitimate reason for accessing the dark web and to be aware of the potential risks involved. Staying informed about the latest news and developments related to the dark web is essential to staying safe.
How To Browse The Dark Web Legally
DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Social networks, such as Facebook, have created dark web versions of their sites to address privacy problems related to their surface web versions. ExpressVPN had created a .onion version of its website to allow greater privacy and anonymity for Tor browser users. VPNs are often recommended as protection in such cases, but Whited disagrees. When people go on about the so-called dark web, they’re usually talking about onion sites, which aren’t searchable via Google or accessible via standard browsers. On the regular web, domains such as are translated into their actual IP addresses via the domain name system (DNS).
Dangerous And Disturbing Services And Items
The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group. These groups include Mazafaka, Trojanforge, Hack Forum, xDedic, and dark0de. Some of these cybercriminals are known to track and blackmail pedophiles.
Though secure against everyday threats, Tor is vulnerable to targeted attacks from state-level actors. For example, in Safer mode, JavaScript is turned off on non-HTTPS (insecure) sites, but in Safest mode, JavaScript is turned off entirely for all sites. Images load normally in Safer mode, but some complex images may not load in Safest mode. The Safer option disables all potentially dangerous website features, while the Safest option enables only the features necessary for basic website functions. To use a new circuit, click the circuit button next to the domain. Then, click on New Tor circuit for this site, as illustrated below.
- Dark web commerce sites have the same features as any e-retail operation, including ratings/reviews, shopping carts and forums, but there are important differences.
- Instead of the onion routing Tor uses, I2P relies on unidirectional tunnels and garlic routing, which bundles multiple messages together for better traffic obfuscation.
- The VPN connection will route your online activity through a different server, masking your activity from your internet service provider.
- Designed to be hidden from conventional search engines like Google or Bing, the dark web is a portion of the internet.
- You can also use a password manager to generate and store complex passwords with ease.
Private Internet Access

You can never be sure who’s really behind the other end of the line. These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy.
What Does Tor Browser Do?
As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor.
Accessing it without proper protection exposes you to surveillance, tracking, and potential security risks. If you need to access the dark web, NymVPN can add an essential layer of privacy and anonymity, encrypting your connection before you even access the Tor network. If you log into personal accounts on the dark web or visit websites with tracking scripts, then your activity may be tracked. Similarly, unless you’re using a VPN, your IP address will be visible to the first relay node you connect to. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
Download And Connect A VPN
I also like NordVPN and ProtonVPN, as they offer dedicated Tor servers that allow you to access .onion sites directly from regular browsers like Chrome. These search engines can help you discover .onion sites related to your interests. However, note that dark web search engines don’t index as many sites as regular search engines, so results can sometimes be limited or outdated. Tor isn’t available for iOS due to Apple’s restrictions, but you can still access the dark web on your iPhone using the Onion Browser, which is from the Tor Project. This app connects to the Tor network, allowing you to visit .onion sites.
The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives. In opennet mode, the network will automatically assign you to other users on Freenet’s network. As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others. That alone might already raise suspicion and place you under special surveillance.
Words Of Caution When Using Dark Web Sites
VPNs let you mask your location and prevent online breadcrumbs from leading back to you. This stops online criminals from eavesdropping on your Wi-Fi connection and intercepting any data you might be sending or receiving. Just like when navigating the surface web, the dark web has similar risks that should be taken into account when protecting your personal information.
But you have to keep your fingers crossed that it remains there and hope the party holding your data (the school or hospital records department) keeps it according to the GDPR standards. If you live in the EU and want to know what data your provider has collected about you, the GDPR gives you the right to request a full report. However, it is often prohibited for ISPs to sell your data to third parties. During that period, on top of the risk of accidental disclosure and theft, governments and the police could ask ISPs to share data.
The Tor network’s principal benefit is that it routes your traffic through numerous servers, wrapping it in several layers of encryption. This makes it difficult for interlopers to monitor the traffic or trace any legal or criminal activity back to you. After all, some websites on the deep web are like those on the open internet, except that they are hidden behind a paywall or protected via passwords to limit access.