A VPN is a confusing factor for many because there are two ways to use it with Tor. If you don’t know where to start, you can use The Hidden Wiki to find a few dark web domains. Simply copy the URL of the site you want to visit, press Enter, and you’re all set. On top of that, Tor’s nodes can also malfunction because they’re owned by volunteers, which will expose your traffic and sensitive information. This is where a VPN comes in, and a reliable VPN like NordVPN (read our NordVPN review here) can do wonders for you. You might’ve heard of the domain extension called “.onion“, which sits at the end of each dark web website.
Step 4: Access I2P Sites (Eepsites)
Ultimately, the Dark Web is neither purely nefarious nor inherently virtuous—it’s a dynamic environment shaped by the motivations and actions of its users. Your decisions, responsible conduct, and awareness of potential risks will determine your experience in this hidden realm. If you exercise due caution and use a combination of the Tor browser and common sense in which sites you access on the dark web, yes, the dark web is safe to use. You may be targeted by law enforcement, exploited by hackers, or threatened by criminals using the dark web for nefarious purposes. The deep web is every part of the internet that is not indexed by search engines, like private messages from your social media or your online banking portal. The dark web is a small section of the deep web that is hidden on purpose, requiring specific software to access.
Using tools like Tor or visiting privacy-focused websites can be perfectly lawful, and in some cases, the dark web is used by journalists, researchers, and activists for legitimate purposes. However, engaging in illegal activities is against the law regardless of where it takes place. Laws vary by jurisdiction, so readers should always check their local regulations before attempting to access the dark web. In this article, we have explored what the dark web is and how Tor Browser provides the necessary anonymity and encryption to access it. We discussed the importance of setting up Tor Browser correctly, ensuring security and anonymity, and navigating the dark web safely.
In your browser settings (like the NoScript extension in Tor), you will want to disable JavaScript and other active scripts. By disabling, you reduce such attacks’ potential (especially on untrusted websites). It is made up of two virtual machines – a Gateway and a Workstation.
Can I Protect My Privacy Without Going Onto The Dark Web?
Before you embark on your journey into the Dark Web, it’s crucial to establish a secure foundation. While the Tor network is designed to provide anonymity, it alone cannot guarantee your privacy or safety. This section will guide you through the essential preparatory steps and tools to ensure that you remain as protected as possible while exploring hidden services and tor onion domains. The “Dark Web” often conjures up images of hidden marketplaces, illicit trades, and shadowy figures lurking in the digital underworld.
Can I Be Traced, Tracked, Or Hacked If I Use Tor?
Although content on the dark web is not as ‘indexed’ compared to the one on the clear web, you can still use search engines to find stuff. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. Forest VPN adds an extra layer of security by encrypting your internet traffic. It ensures your activities remain untraceable, providing peace of mind. Plus, its battery-saving technology means less CO2 generation, aligning with eco-conscious values.
Will Visiting The Dark Web Attract Attention?
Your ISP still knows you’re using Tor, and entry nodes can see your real IP address. A VPN adds protection before Tor, closing these gaps without breaking access to .onion sites. Tor routes your traffic through a chain of relays to obscure your IP address.
How To Get The Tor Browser
Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Other dark web search engines worth investigating are Ahmia, Torch, NotEvil, and the Onion URL Directory—just type out some keywords for what you’re looking for. Some of these sites can be found through regular web browsers, but you’ll then need to switch over to Tor once you’ve got the onion links you want to follow. There are also popular free legal websites which can be accessed via a .onion address.
Meet LockBit 50: Faster ESXi Drive Encryption, Better At Evading Detection
Some of these cybercriminals are known to track and blackmail pedophiles. Moreover, hackers who offer their services over the dark web have also targeted financial institutions and banks. The most prevalent dark web content is child pornography, about 80% of its web traffic, despite being challenging to find.
By following these setup instructions, you can ensure a smooth installation and configuration process, allowing you to reap the benefits of Tor Browser and browse the internet anonymously. It’s important to note that Tor Browser may run slower than traditional browsers due to the encryption and multiple relays used to route your internet traffic. This is a trade-off for the increased privacy and anonymity it provides. The Tor browser is completely free to use and is available for most major platforms, including Windows, Linux, macOS, and Android. You simply need to download it for the platform you use and install it on your system.
Are Dark Websites Illegal To Use And Visit?
That allows .onion sites to be accessible anonymously without services like DNS. Never sign in to any account linked to your real identity (email, social media, banking, etc.) while browsing the dark web. Doing so can tie your activity back to you, destroying your anonymity. If you need to create accounts on dark web services, use a burner email and never reuse usernames or passwords from your real life. If you must purchase anything on the dark web — which I don’t recommend — you should always pay in cryptocurrencies.

For the dark web, though, you need an entirely different entry point known as an overlay network. The dark web is full of malicious actors, cybercriminals, and other people who are looking to prey on curious but unprepared dark web browsers. By defining your goal and purpose, you won’t find yourself wandering down the dimly lit corners of the dark web, and you can stay on the path you set out for yourself.
- Cybercriminals often disguise harmful files as legitimate downloads, making it easy to get tricked.
- Ensure that you’re aware of what is permissible in your jurisdiction.
- Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise.
- Fraud and scams run rampant on the dark web, including offers too good to be true and fake services requiring upfront payment.
- Exploring the dark web can be a valuable experience if done safely.
- The first step in accessing the dark web using DuckDuckGo is to download and install the Tor Browser.
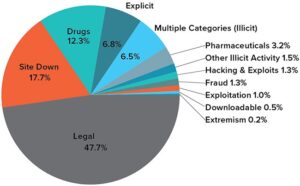
The problem is that getting to those forums may require opening yourself up to safety concerns like the ones listed above. The Tor network combined with a VPN is one of the safest ways to get on the dark web. Many internet service providers (ISPs) and governments are suspicious of Tor use, but a VPN will hide your internet activity and help prevent anyone from knowing that you’re using Tor. Researchers from Recorded Future estimated that while there are more than 55,000 existing onion domains, only 8,400 (or roughly 15%) of these sites were active. So, when measuring the total network of live dark web sites alongside the surface web, only about 0.005% of the internet is the dark web. When searching and surfing the dark web, it is possible to run into malicious websites that contain malware.
The dark web offers a high level of anonymity, attracting various users, including journalists, activists, whistleblowers, and unfortunately, criminals. While not all activities on the dark web are illegal, it is infamous for facilitating illegal activities such as drug trafficking, hacking services, and the sale of stolen data. It is important to understand that engaging in illegal activities on the dark web can have severe legal consequences, as law enforcement agencies actively monitor these activities. The dark web refers to websites and content that are not indexed by search engines and require special software, such as Tor, to access.
The Tor Browser also features many built-in protections that protect against tracking and fingerprinting. Identifying specific individuals who use the dark web can be quite tricky. However, we advise connecting to one of our recommended VPN services to stay anonymous. One of the great things about Tor is that it can be used to access both the dark and surface web.