It’s an interesting resource that translates Tor internet traffic levels into easy-to-digest stats. Riseup is available on the surface web, but its presence on the Tor network extends its privacy benefits by letting you use its services without exposing their real-world identities. You can access encrypted email services through the onion site without getting tracked.
News & Media
Not to mention the fact that you’ll get exposed to some stuff that will definitely make you take several cold showers. At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays. Afterwards, your request will be matched with the appropriate website.
The Best Dark Web Search Engines In 2024
Safe, reliable, and uncompromising, SecureDrop allows users to share sensitive documents securely among themselves. The dark web also allows these individuals above to get around any restrictions that affect regular internet usage. In this article, we aim to share the best dark websites you can visit for unbiased and unrestricted news.
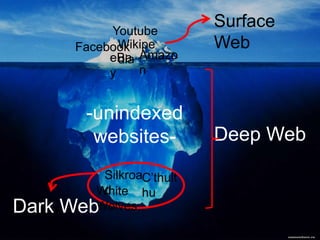
To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section. The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. That means that only 0.024% of all the known pages are findable in Google’s search engine. The users only have access to a fraction of the available data and web pages. Consider turning on your VPN at this stage in the preparation process.
Whether used for good or ill, its shadowy nature is unlikely to fade anytime soon. For example, the Freedom of Information Foundation has long advocated for the use of the Dark Web in enabling free speech in repressive regimes. The dark web exists inside layered proxy networks, known as darknets. Tor, or “The Onion Router” is by far the largest of these darknets.
We’ll use the Tor browser for this guide, but any other browser that supports the Tor protocol will do. Additionally, check the Block pop-up windows and Warn when websites try to install add-ons settings. You should review access to your camera, location, and microphone regularly to ensure no website has unnecessary permissions. Additionally, many Internet Service Providers (ISPs) flag Tor usage as suspicious and may block access to the network altogether. The dark web is a playground for hackers, cybercriminals, and people with nefarious objectives.
Overflow: Hidden;
I like testing new software for work, but I’m less “plugged in” to the internet than I used to be. I tend to read app privacy policies to see what kind of data companies collect, and as a result of those findings, I don’t use many mobile apps. In a similar vein, I was an early adopter of many social media platforms, but now I’m just an infrequent Reddit lurker.
Crawlers can automatically scan websites and their links, then record them. Pastebins are text sharing services, useful for sending and sharing large snippets of code or text. ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it. One of the most popular ways to get around the dark web is not to use a search engine at all.

Android users need to download the Tor Browser app, while iPhone fans should get the Onion Browser app. While the best dark web sites listed above are a good starting point for a safe, legal surfing experience on Tor, there really is no substitute for a VPN. SecureDrop has even been adopted by various news organizations worldwide.
Dark Web Links: The Onion Patch – Best 20 Websites You Shouldn’t Miss
- I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours.
- Using the ProtonMail .onion site offers security and privacy advantages.
- When you try to enter a .onion website, it will reroute your access request around the internet, bouncing it off three random servers before you reach the target website.
- But if you live in a country with restrictions, you would get all the features outside the restricted area.
- For evidence, look no further than the way Google automatically adds travel information, meetings, and other diary entries onto your calendar.
- Cryptocurrency miners and other malicious software often target dark web users.
It is a Swiss-based company (privacy-friendly country), and all its tools are open-source, meaning anyone can test its vulnerabilities. The advantage of this version is that you can effectively create a Facebook account anonymously or use this social media platform in a restricted region. Consequently, you’ll have maximum privacy while sharing opinions and anti-oppression resources. Yes, but you need to be cautious because there are many malicious sites on the dark web. The best way to do that is to get the link from legitimate sources, like The Hidden Wiki. What’s more, you should always use a VPN (like ExpressVPN) with Tor to protect yourself from IP leaks.
Other Safety Precautions To Follow
Stay private with a tool like Surfshark’s Alternative ID to mask your contact details and use generated data on sites you don’t trust. Given the above threats, it’s a good idea to use Tor over a VPN to access the dark web. ZeroBin is an attractive option for anyone looking to share sensitive information without compromising privacy.
Finding Onion Sites

To protect your privacy, always use a VPN before accessing the dark web. Additionally, avoid sharing personal information and refrain from clicking on unfamiliar links. When you access a dark web site, your connection is routed through multiple nodes, each adding a layer of encryption. This process is akin to peeling an onion, hence the name for the Tor network. Each layer ensures your IP address remains hidden, offering a degree of anonymity unparalleled on the surface web. However, this also means that navigating the dark web can be slower due to the extensive encryption involved.
Is It Illegal To Browse The Dark Web?

Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges. (Presentation and polish isn’t quite so important on this part of the internet.) Click on any website link, and it’ll appear on screen, with its address at the top. To help you make educated choices about cybersecurity to keep you (and your data) safe and secure, by providing detailed, accurate, and practical information based on thorough testing. Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users.
Use Verified Links To Ensure You Stay Safe On The Dark Web
Your clear web browser activity can be logged and tracked by advertisers, governments, and your ISP if you’re not using a VPN. Dark.Fail is one of the best ways to find active and—most importantly—legitimate onion links. The Tor browser is a modified Mozilla Firefox browser with numerous integrated scripts and add-ons to protect your privacy while browsing onion sites. The Tor browser is the perfect option for users who need to stay private while disseminating sensitive information. Thanks to the global community of volunteers, Tor Metric can utilize nodes for layered encryption. Regardless of the dark web’s reputation regarding its secretive dealings, it still has a lot of upsides.
An oppressive regime won’t tolerate this and will block the news website, restricting access. There’s no way to delete personal data once it is circulating on the dark web. Your best option is to take steps to make sure your information is useless to criminals. For example, it’s a good idea to change your passwords, contact your financial institutions, freeze credit, and set up two-factor authentication. But, for anonymity to really work, Tor needed lots of people using it, not just spies and their handlers.


