Indeed, these websites use “atypical” names and domains to present themselves. So, instead of “facebook.com”, the URL can look like “12ls834mfdg8.onion”. Though secure against everyday threats, Tor is vulnerable to targeted attacks from state-level actors.
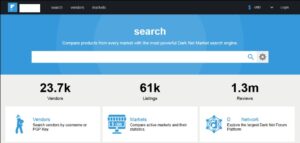
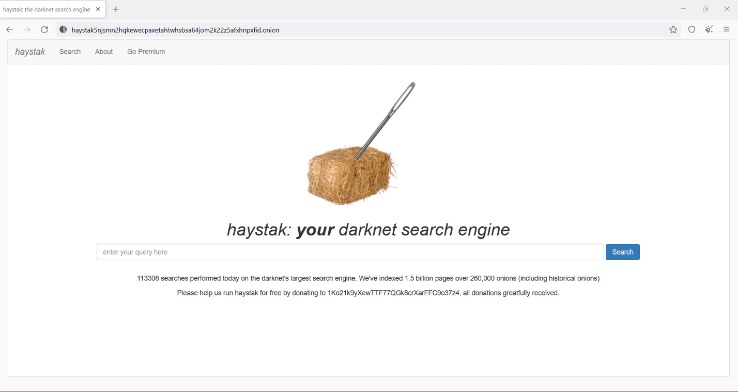
Dark Web Search Engines
In this tutorial, we’ll explain how to access the dark web in complete privacy and cover a few more important factors to consider before starting. Tor traffic is decrypted at the exit node, which opens a vulnerability for malicious actors to inject malware or intercept traffic. Hence, it’s advisable not to download files via Tor, especially from unknown sources.

Step 5: Navigating The Dark Web
Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity. People often have bad feelings about the dark web, but not everything on it is illegal or dangerous. In fact, journalists, privacy advocates and academics use it every day to protect their identities and get to material that has not been blocked.
Proton VPN
- Also, its P2P routing design is more advanced and does not rely on a trustworthy directory to obtain route information.
- Tor’s anonymity function is used by everyone from human rights workers and journalists through to drug and arms dealers.
- However, there are plenty of legal and legitimate online activities that require privacy and anonymity.
- For a number of technical reasons, it’s much faster and more reliable than Tor.
- When you use Tor, which routes your internet traffic through many different relay nodes, your online activity is obscured because you’re browsing anonymously.
Although websites can’t identify you and ISPs can’t decrypt your internet traffic, they can see that Tor is being used. If you want to learn all about privacy protection or cryptocurrency, the dark web has plenty to offer. There are a variety of private and encrypted email services, instructions for installing an anonymous operating system and advanced tips for the privacy-conscious. Dark web websites look pretty much like any other site, but there are important differences.

How Do I Access The Dark Web Safely Using Tor Browser?
The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment).
- Since these aren’t indexed on search engines like Google or Bing, you’ll need to dig around subreddits like r/Tor or r/onions to find them.
- However, don’t fret yourself about this frightening concept, than the actual meaning of the dark web.
- The spouses of Ashley Madison users received blackmail letters demanding they pay $2500 in Bitcoin or have the infidelity exposed.
- Given the prevalence of malware across the dark web, it’s vital to have antivirus software installed and active on your device when accessing it.
- After installation, you can use Tor to access the public internet as well as .onion websites.
Yes, Tor is slower due to multi-layer routing, but privacy is prioritized over speed. Secure communication for journalists, accessing privacy-focused forums, and whistleblower submissions. Tor encrypts your traffic and routes it through multiple volunteer-operated relays, making it difficult to trace. Additionally, always keep your Tor Browser up to date to benefit from the latest security enhancements and bug fixes.

How To Safely Access The Dark Web
We will never sell, rent, lease or trade your personal information to any third party. When we use a payment-processing merchant we ensure that the same strict privacy criteria are in place. We do not (knowingly) collect personal information from persons under the age of 18. Protecting your online presence must be a priority whether you’re on the dark web or not. While it may sound like something instantly out of a spy movie, the dark net is undoubtedly part of the internet.
Related Articles From The Safe Browsing Section
As long as you are vigilant about your online activity, there aren’t any issues. The maximum trouble you can get into on the dark web is visiting political forums or marketplaces. In that case, the government might flag and monitor you even if you’re not a participant or trader. Both methods improve your online security and anonymity compared to not using a VPN.
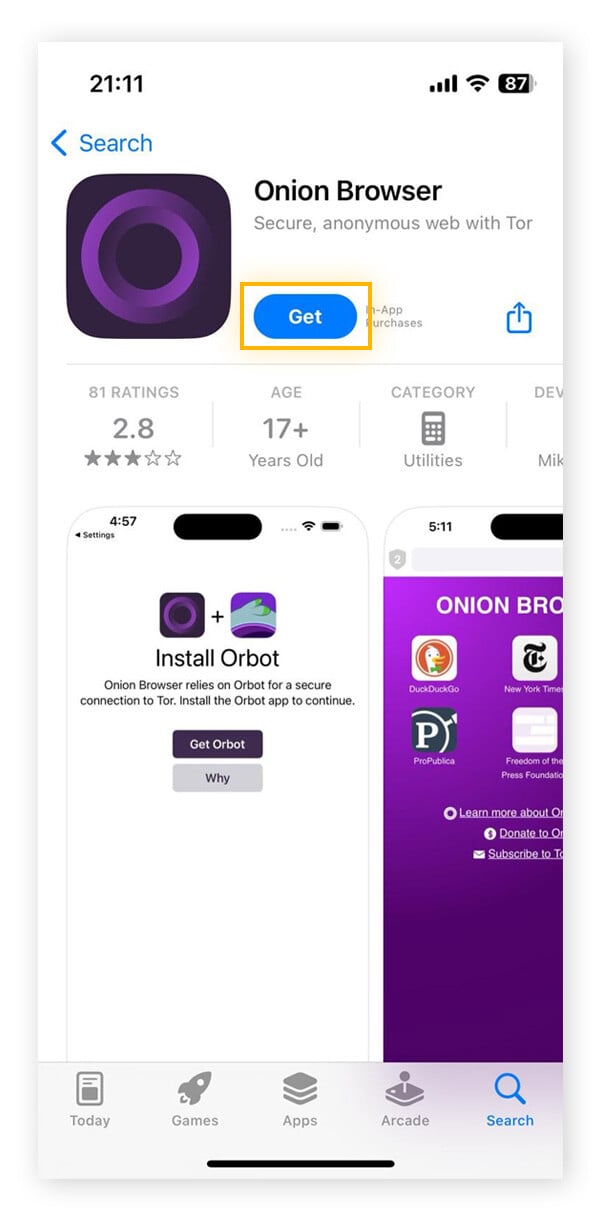
Step 2: Download Tor Browser
You may have heard a lot about the so-called Deep Web and Dark Web lately. The Deep Web is the part of the Internet that houses 90+ percent of the web yet it’s completely tucked away from the easy access we’ve come to enjoy from search engines. The Dark Web, on the other hand, is a smaller portion of these Deep Web that’s only accessible with special software like the Tor browser. Joking aside, there are some crucial steps to take if you want to access the dark web safely and anonymously. A dark web search engine is an online program that searches the dark web for websites not listed on regular search engines. Although dark web search engines are available, keeping pace with their constant evolution is challenging, even for the best programmers.
Can You Use The Tor Browser On A Mobile Device?
The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users. By doing so, early signs of fraud can be detected in near-real time, such as new inquiries on your credit file, like new credit cards or bank loans. With all this data, your ISP could create a very accurate profile of you and link it to your IP address. This is one of the reasons why it is always good to hide your IP address.

Dark web websites don’t bear Internet Corporation for Assigned Names and Numbers (ICANN) domains, such as .com. They use a scramble naming structure that combines a string of letters and numbers to create URLs that are impossible to remember. Anonymizing browsers are banned in some countries like China and Russia. Moreover, given the nefarious nature of the dark web, some government agencies may set up Tor gateways to monitor what’s happening on the dark web.
This section will guide you through the essential preparatory steps and tools to ensure that you remain as protected as possible while exploring hidden services and tor onion domains. The dark web is a hidden part of the internet that isn’t indexed by traditional search engines and requires special software like Tor to access. It’s often used for anonymity, both for legitimate privacy reasons and for illegal activities like black market trading or data leaks. While the dark web has search engines such as Ahmia that index some “.onion” websites, many hidden services are not indexed at all. This makes it more challenging to find specific sites, increasing the chances of stumbling upon malicious or fraudulent sites.