ProPublica is a non-profit investigative journalism outfit based out of New York City. It’s committed to transparency and public service, which is why it maintains a dark website along with its site on the surface web. Not to be confused with the riskier Hidden Wiki page, Wikipedia on Tor serves as a vast repository of information. You’ll find articles on a wide range of topics, such as history, science, and culture — and that’s just scratching the surface.
Bitcoin Wallets
For instance, many legitimate services such as private forums, subscription-based media, or cloud storage services are hosted on the deep web. In contrast, the dark web is intentionally hidden for illegal activities, often using Tor or other anonymizing tools to keep users’ identities secure. While deep web markets can include legitimate businesses, dark web markets are typically linked to illegal activities, and their anonymity makes it easier for illicit trades to occur.
Quick Links
- Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them.
- An easy way to find content on the dark web is to receive a link from someone who already knows about it.
- A random dark web link can lead you to malicious software, phishing sites, and illegal content.
- Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing.
- The sites also accepted payments for their illicit goods and services in bitcoin or similar virtual currency designed to be as anonymous.
- Websites and data on the dark web do typically require a special tool to access.
A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Still, since they exist within the dark web, there is a high chance that malicious entities have co-opted one or more for illegal activities.
Meet LockBit 50: Faster ESXi Drive Encryption, Better At Evading Detection
It makes up for this with enhanced security and user safety features, helping users to ensure they are not getting phished. People have been organizing illicit trades via the Internet since the 1970s. Those early examples, though, were through closed networks, and the actual exchanges of money and goods generally had to take place in person.
Monero (XMR): Darknet’s Currency
Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. Using the ProtonMail .onion site offers security and privacy advantages. Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection.
How To Hide IP Address In 2025 (A Comprehensive Guide)
In this volatile ecosystem, recognizing the dynamic nature of the dark web is half the battle. By acknowledging that services, communities, and security measures are in constant flux, you can better position yourself to respond effectively. This article aims to shed light on the more constructive side of the dark web, guiding readers toward reputable resources and reliable information. We’ll cover the foundational principles of anonymity on networks like Tor, discuss how to navigate this hidden realm safely, and emphasize the importance of verifying sources. Throughout, we’ll stress the ethical and legal considerations that come with exploring these lesser-known platforms. In addition to the Tor browser, you should use an antivirus program (like Norton 360) to protect your device from malware infections, and a VPN (like ExpressVPN) to secure your IP address and traffic.
The Rise Of The New Silk Road Dark Web
It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web. It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value.
It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. However, not all books on this site are legally available, so they don’t have copyrights. That means you may violate copyright laws while downloading books, so use a VPN to protect yourself from any legal repercussions if you have a dire need to use it. You can access thousands of issues, from the most popular to the most niche. It is one of the best sites on the dark web to find your favorite comics. The Imperial Library currently holds around 1.5 million books, some of which may be hosted illegally, and thus, their consumption might violate copyright laws.
He was arrested in a San Francisco library while logged in as site admin. The last several years have seen a vise-like grip tighten around dark internet venues like DarkMarket. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents.
Bypassing firewalls and other forms of geo-blocking helps people to access news websites and social media they normally wouldn’t be able to — and do so with less fear of recrimination. Impreza Hosting is a service that helps you host a site on the Tor network. It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. Pastebins are text sharing services, useful for sending and sharing large snippets of code or text.
Best Free Firewall Software In 2025
The dark web has no shortage of criminal activity, scams, phishing sites, suspicious links, and malware designed to trick newbies. And because there’s very little use of HTTPS on the dark net, verifying whether or not a website is genuine using an SSL certificate is not feasible. Dark net websites are called “Tor hidden services“, and they can be distinguished from normal websites by their URLs. Even when using security measures and your common sense, accessing deep web content still poses a risk. Antivirus will ensure that any viruses or malware downloaded from the dark web are removed.
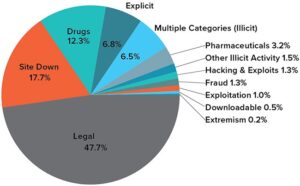
The darknet marketplace is home to a plethora of illegal and legal activities. However, the markets are dominated by things like illegal drugs, explicit content, pirated files, hacking services, and stolen personal information, among others. Ensuring that the onion links you follow lead to the intended, trustworthy destinations can be a constant challenge on the dark web.
If you access illegal content or participate in criminal transactions, you face legal consequences. The legality depends on your activities and your country’s specific laws regarding darknet use. The dark web contains numerous security risks, from malware to scams and illegal content. Thankfully, there are effective measures that keep you secure on the dark web and ensure you remain protected and anonymous while accessing .onion sites. The so-called “Dark Web” often conjures up images of hidden bazaars for illicit goods, secretive communication channels, and shadowy corners of the internet inaccessible through standard search engines. The dark market websites were designed to facilitate illicit commerce by providing anonymity to users, in at least two ways.