An easy way to find content on the dark web is to receive a link from someone who already knows about it. No one is hiding here—they’re just guaranteeing that people in censored countries can read the news without being flagged. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction. This makes it extremely difficult to find out who you are transacting with.
The Best Dark Web Search Engines In 2025
Clicking on random onion links is quite risky and isn’t recommended. A random dark web link can lead you to malicious software, phishing sites, and illegal content. It doesn’t track browsing habits or personal data and won’t expose a user’s identity or location. This makes it safer for those who can’t freely access certain content. The New York Times operates one of the biggest news sites on the Tor network, letting users access its regular news coverage with increased privacy and security.
- Previously, the Silk Road was the most popular darknet market, created by Ross Ulbricht, AKA Dread Pirate Roberts.
- Beneath it lies the deep web, which includes content not indexed by traditional search engines.
- Haystak does not censor content by default but provides safety flags to help users make informed decisions.
- Always use a fake name and a temporary email address when you buy something from dark net shops.
- The dark web is often confused with the deep web, but they are not the same.
Ever-Changing Addresses And Infrastructures
Hidden networks also host a range of resources that can inform, educate, and support individuals who value anonymity. From uncensored libraries to secure whistleblowing channels, these platforms can offer benefits difficult to find on the clear web. Beyond the legal aspects, there are ethical considerations to weigh. At the same time, these networks can also facilitate exploitation, hate speech, and other harmful activities. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links.
To stay safe and private when visiting any listed sites, ensure you have a VPN and anti-malware installed and enabled. Because it’s a members-only platform, you’ll need to register first. Thankfully, you don’t need to use your official name or email; just use a fake username (we tested it successfully). The site doesn’t require an email verification, though it offers all the features and security that you want in a dark web marketplace.
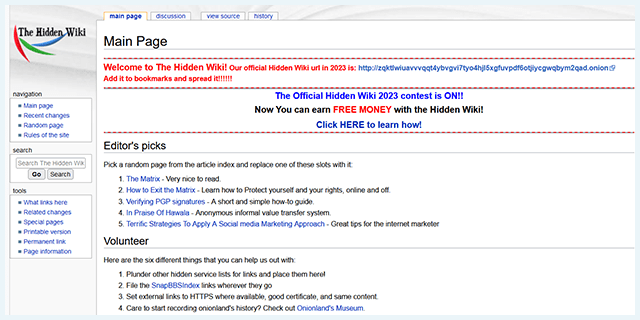
The Hidden Wiki
- It allows access to the .onion sites on the dark web that you won’t find using a regular browser.
- Using TAILS is yet another security measure that protects your online identity on the dark web.
- But before we start, install Norton VPN to help protect your digital identity and stay safer online.
- While the deep web comprises about 90% of the total web, the dark web makes up just a tiny fraction of the deep web total.
- Most people start by using the Tor Browser, which hides your IP address.
- You can even apply for jobs and request information, among other things.
Some may log search history, contain hidden scripts, or other elements that can jeopardize user anonymity. Always choose search engines that uphold user privacy and avoid those that collect data or present intrusive scripts. Unlike the surface web, dark web search engines have no reliable mechanisms to report or take down malware-hosting websites.
While some .onion sites provide essential services like secure communication and censorship-free journalism, others spread malware or run scams. With this in mind, finding verified links is crucial for avoiding threats on the dark web. H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites.
Useful Links
Perhaps that’s their option for generating consistent traffic and a steady influx of new members. Perhaps its strong community is helping the administrators to keep the forum alive after all the attempts by authorities to seize. Russian Anonymous Marketplace (RAMP) is a hybrid marketplace that strongly focuses on ransomware groups. One of its highlighting features is the fact that it has multilingual support, as it features Russian, Chinese, and English. We’re back with another video in our Webz Insider video series on everything web data. Learn how to automate financial risk reports using AI and news data with this guide for product managers, featuring tools from Webz.io and OpenAI.
Darknet Markets
Get in touch with one of our experts to learn more about how our tools can help you gain better access and insights from sites and content far beneath the surface web. However, any illegal activity that is prohibited in the real world is also illegal on the dark web. The dark web often conjures images of shadowy corners of the internet, filled with intrigue and danger. Contrary to popular belief, it isn’t all illicit dealings and clandestine exchanges. There’s a wealth of legitimate resources and communities hidden behind the “.onion” domain, waiting to be explored by those who dare.
Encryption
Beneath it lies the deep web, which includes content not indexed by traditional search engines. Within the deep web exists an even more concealed layer known as the dark web. Explore the best dark web links 2023 for safe browsing, resources, and communities.
Frequently Asked Questions (FAQs) About The Top 10 Dark Web Search Engines
We’ll cover the foundational principles of anonymity on networks like Tor, discuss how to navigate this hidden realm safely, and emphasize the importance of verifying sources. Throughout, we’ll stress the ethical and legal considerations that come with exploring these lesser-known platforms. George is a seasoned Cybersecurity writer who has been writing guides and news about digital security for over five years. He has worked for several international tech platforms, and his writing and editing expertise has also enhanced over time. He loves covering topics about VPNs, online privacy, and anonymity and shares his knowledge of online security with internet users through his words.
While these platforms should never be used casually or without proper precautions, they offer unique visibility into potential threats that may otherwise go unnoticed. Given the decentralized and hidden nature of the dark web, finding specific content can be a major challenge. Unlike Google or Bing, which use crawlers to index the “surface web,” dark web search engines like Ahmia, Torch, and Haystak are specifically designed to crawl and index .onion sites. They act as a guide, providing a curated list of links and marketplaces that would otherwise be nearly impossible to find. While some of these search engines filter out known scams or illegal content, others are un-curated, meaning a search can lead to highly disturbing or dangerous material. Their role is to provide a form of navigability to a network that is intentionally difficult to navigate, serving both those with legitimate intentions and those seeking illicit goods.
Dark Web Resources
While no approach is foolproof, a thoughtful, criteria-driven strategy ensures a more secure and beneficial experience on the dark web. Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal… The deep web is not a series of sites but a storehouse of records, including email accounts, medical records, private messages, and more. We recommend installing a premium antivirus program for optimal protection against malware infections. We also made sure to select only sites that have been around for a considerable amount of time without being taken down or being the subject of any privacy or security scandals. The Tor browser option for streaming comes with eleven channels with varying genres.
Altenen employs aggressive marketing tactics—new users must promote its links on social media to gain access—ensuring a constant influx of traffic. Dark web forums play a pivotal role in the cybercrime ecosystem, enabling the exchange of stolen data, hacking tools, and illicit services. Below is a curated list of the most active and dangerous dark web forums, each with its own specialties and threat landscape. Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.
Legitimate Use Cases For The Average User
This is usually due to the sensitive nature of the businesses or services they offer. Onion sites may offer secure access to cryptocurrency wallets or anonymous email clients. Using a reliable VPN with Tor provides a way to improve security when accessing dark web links. The VPN encrypts your traffic before it enters the Tor network, preventing your ISP from seeing that you’re using Tor. This double encryption also protects against compromised Tor entry nodes that could potentially monitor your activity.