If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Always use a fake name and a temporary email address when you buy something from dark net shops. You can even use a secure email provider or a burner email address whenever you visit the dark web. In April 2016, its APIs were compromised, resulting in stolen messages.
Scammers Sell Access To Steam Accounts With All The Latest Games – It’s A Trap!
- Keybase is a dark web messaging application that functions much like Signal and WhatsApp, except it is secure and private.
- The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results.
- It lets you search both clearnet and dark web sites, but it blocks all trackers, doesn’t use your location data, and never stores your search history.
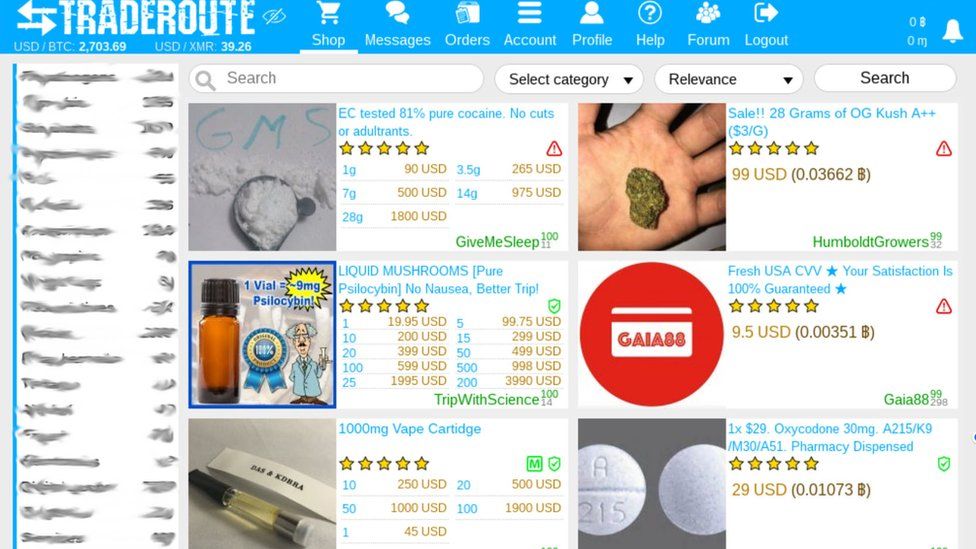
- The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins.
- District Court for the Eastern District of New York unsealed a superseding indictment charging Volodymyr Viktorovich Tymoshchuk — also known as deadforz, Boba, msfv, and farnetwork…
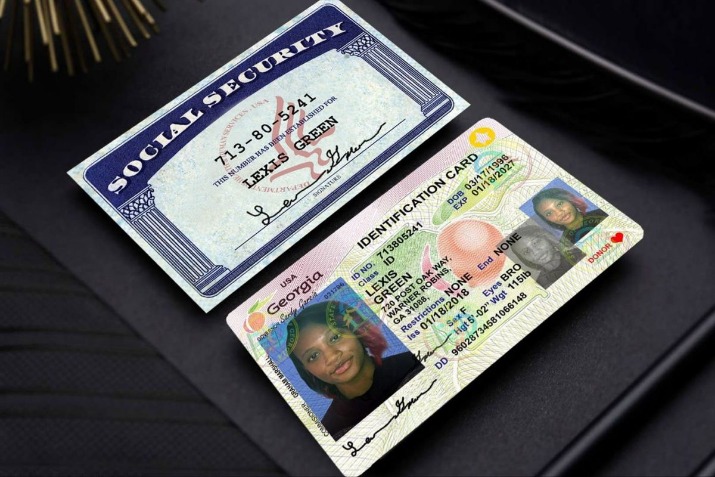
Since all activity on the dark web is anonymous by default, it is definitely where the murkiest transactions on the internet take place. A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. The FBI moved swiftly to remove the Silk Road (and other illicit online marketplaces) from the dark web because they were flagrantly facilitating online drug sales and other illegal activity. Other marketplaces were taken down due to more direct threats to public safety, like assassination commissions and sex trafficking. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools.
You can even apply for jobs and request information, among other things. People like spies or whistleblowers often contact the CIA via the dark web to keep themselves hidden. To provide freedom of speech and keep journalism a strong pillar of the economy, the BBC made this Tor mirror. It helps people anonymously use the BBC website without restrictions. The famous social media platform has a prominent presence on the dark web.
By doing so, we contribute to a safer and more secure digital environment for everyone. Precautions, such as educating oneself, consulting legal advice, protecting personal information, and choosing reliable sellers, are essential if one were to consider exploring the dark web. However, it is strongly advised to abstain from engaging in illegal activities altogether.
Thus, use the best antivirus software that protects against these online threats. As these marketplaces keep changing, it is critical to stay on top of the main platforms on the dark web worth monitoring. Monitoring dark web markets is crucial, no matter if you are a business or individual, as you can then proactively identify and mitigate potential breaches and cyber threats.
Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews.
Kurt The CyberGuy’s Message To Parents: Don’t Rely On Social Media Safety Features For Your Teen
It contains a good selection of product listings that range over 35,000 items. The website has an interface and design similar to other dark web shops. It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. To prevent users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers. Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea of the vendors for the buyers and vice versa. This marketplace accepts payments via Monero but also supports the Escrow system.
Improving The Web: Building A Smarter, Safer, And Faster Internet
Yes, you can access the dark web on a smartphone, but you’ll need an appropriate browser, like Tor browser for Android or Onion browser for iPhone. Remember that phones can get viruses just as easily as computers, and the chances of getting a virus likely increase when you’re browsing dark web mobile sites, no matter your platform. Onion sites are websites on the dark web that use the “.onion” top-level domain instead of “.com,” “.net,” “.gov,” etc. Onion sites use The Onion Router (Tor) software to encrypt their connections and enable anonymous communication. The dark web is the unregulated part of the deep web, which encompasses all parts of the web not indexed by search engines. While the deep web comprises about 90% of the total web, the dark web makes up just a tiny fraction of the deep web total.
Ready To Explore Web Data At Scale?
You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on. Before clicking any of the dark web links below, you’ll need to get the Tor Browser (also called the Onion Browser) or another service that provides dark web access, such as the Brave browser. LifeLock Standard comes with a range of identity protection tools, including a Dark Web Monitoring feature to notify you if your information is detected on the dark web. If it is, LifeLock will help you take steps to secure your identity and accounts.
Cryptocurrency Wallets For Safe Transactions
- The Tor browser option for streaming comes with eleven channels with varying genres.
- This includes separating personal and market-related accounts, avoiding reuse of usernames, and never sharing identifiable information.
- It offers features like encrypted communication for chats and file sharing, making it popular with privacy-conscious individuals.
- The potential short-term gains are not worth the long-term legal and ethical implications.
- Avast SecureLine VPN encrypts all of your internet traffic to help block hackers and keep snoops out.
- It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer.
Unlike surface web content, dark web pages are not indexed by conventional search engines. Accessing this hidden part of the internet requires specialized software such as the TOR Browser and a Virtual Private Network (VPN) to maintain security and anonymity. It all starts with Tor, which keeps your identity under layers of encryption. The Tor browser conceals IP addresses and browsing activity by redirecting web traffic through a series of proxy servers operated by thousands of volunteers across the globe. This process, called onion routing, protects users from surveillance and tracking.
Discover Content
We’re back with another video in our Webz Insider video series on everything web data. PGP ensures that messages and sensitive instructions are encrypted and cannot be intercepted. Using unique keys for each vendor or market prevents leaks and protects your communication from third parties. In the next section, we will discuss how to choose a reliable seller in the Dark Web marketplace, should you decide to proceed with purchasing an SSN.
We rank markets based on what we believe is important for you and let you choose what works for you best. Tor Links is a backup directory of “.onion” sites in case other directories go offline. The best Tor sites are under constant threat of closure, including Tor directories like the Hidden Wiki, so having a backup in case one goes down is handy. ZLibrary hosts free file-sharing access to academic texts, scholarly articles, and general-interest books. It often hosts copyrighted materials without permission, violating many countries’ copyright laws. Downloading or distributing such material is against the law and can have legal consequences.
Don’t click on suspicious links, be skeptical of what you read, and avoid dark web marketplaces if you don’t want to stumble on illegal activity or content. The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage. Rapid response can prevent unauthorized transactions, minimize financial losses, and protect your customers’ trust in your business. Dark web monitoring platforms, such as Lunar, provide an automated solution to safeguard personal identifiable information (PII) and credit card details. These platforms continuously scour the deep and dark web, looking for any traces of your sensitive information. By setting up alerts, businesses can receive notifications whenever their PII or credit card information appears in suspicious contexts.
How Dangerous Is It To Click On Random Onion Links?
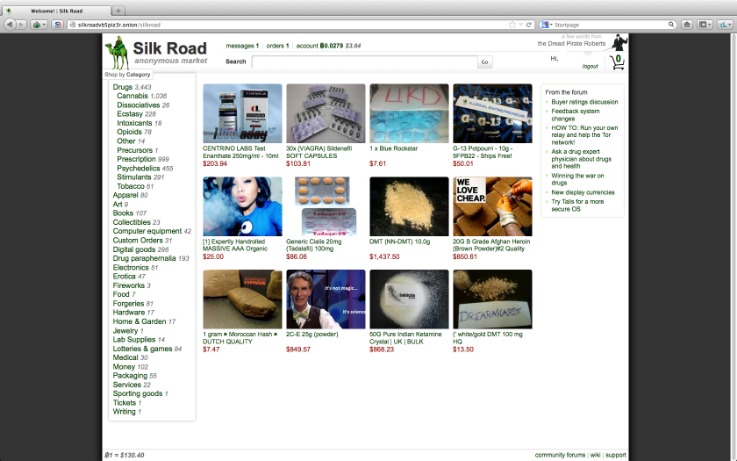
The Silk Road was a famous dark web marketplace where users could buy and sell goods and services anonymously. All the payments were made through cryptocurrency, further enhancing marketplace anonymity. The users on this site can review and rate the products that promote reliable and fraudster vendors.
Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity. That’s why we recommend connecting to VPN before accessing Tor—VPN encryption protects your data, and changing your IP adds an extra layer of privacy to protect you. Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar.