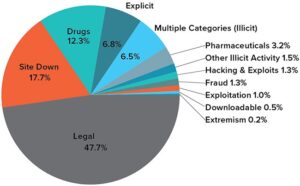
If you’re searching for a reliable dark web marketplace, We The North Market provides secure transactions, encrypted communications, and a low 5% vendor fee. In this guide, we’ll break down the top dark web markets and how to stay safe while using them. We see that, unsurprisingly, the actual implementation of security mechanisms is actually very relevant to almost every aspect of market operations. This is reasonable, as some users go to dark web markets with the intent of hiding their true identities, in order to conduct potential illegal activities without legal consequences. Market operators also know the importance of security mechanisms, and often build their infrastructure with security at its core. Georgoulias et al. 18 comprehensively documented the features and functionality of existing dark web markets in 2021.

Darknet Market
In practice, some markets have very restrictive thresholds, making it very challenging to obtain data for the entire market. For example, in Bohemia, our crawler operates at an average of ten requests per minute without the need for manual intervention for a long time. If we doubled up the speed (or even faster), we might be able to collect data more quickly in bursts, but if we continued for several minutes, we would trigger the anti-crawling mechanisms and this would interrupt our data collection. Bergman and Popov 3 systematically reviewed 34 published research articles that contained web crawlers on the dark web.
- In the area of Milan (53%) and Bergamo (22%) 75% of the Lombard seizures were carried out.
- The platform’s popularity continues to grow, attracting both new and returning customers.
- NAPLES, Italy (AP) — Hundreds of once-missing artifacts, hunted down over decades by a special police unit, have been unveiled for the first time in the National Archaeological Museum of Naples, in southern Italy.
- Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data.
- The Italy Dark Fiber Network Market has substantial opportunities in expanding infrastructure to underserved and rural areas.
- It is the loot of raiders who for decades have targeted sites from classical antiquity in southern Italy, such as Pompeii and Herculaneum.
Incognito Enhances Security

And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. One of the most common is the exit scam, where a marketplace suddenly disappears and takes everyone’s money with it. There’s also a privacy angle—some users live in countries with censorship or surveillance, and the dark web gives them a space to communicate or access information more freely. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. For operations security he suggests avoiding storing conversation logs, varying writing styles, avoiding mobile phone-based tracking and leaking false personal details to further obfuscate one’s identity.
- For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
- A timeline of darknet marketplace evolution, from Silk Road to 2025’s top players.
- Others are looking for stolen data, hacking services, or even banned books and political content.
- For example, Tor got to an average speed of 51 kB/s while I2P only got to approximately 13 kB/s.
- For markets marked with open circles, we believe users are still able to report directly to the market operator via in-site messages or support tickets.
Given the explosive growth of these markets, organizations must prioritize proactive threat monitoring. Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily.
Cyble Titan Endpoint Security
Accordingly, long-term participation in the market becomes a signal of the concept of the’shadow of the future’, suggesting that expected future interactions influence present behaviour. Similarly, the lifespan of criminal actors on online carding forums, particularly in the form of’long-term participation in the market,’ has been identified as an indicator of trust 29, 144. Prior research also identified the length of time vendors are active on the sites as a signal of trust 33, showing that seniority is significantly and positively correlated with criminal opportunity. This suggests that longer engagement may improve criminal performance, which indicates reliability. It is, therefore, reasonable to hypothesise that the longer sellers have been in the market, the lower the probability or number of fraud cases.
Anonymity Through Tor
The Dark.Exchange is a gateway to products and services being bought, sold, and traded on the black market, underground economy, and dark markets. Incognito Market runs 20,000+ listings and $2.8 million monthly trades with BTC and XMR, holding a 5% market stake. Its 10,000+ users and 800+ vendors rely on 2FA and escrow security for private cryptocurrency trading. With many dark web marketplaces coming and going, finding a safe and reputable platform is more important than ever.
What Is Cyber Threat Intelligence?
But don’t let the expiration dates fool you, all of these items are still perfectly good to eat and can be stored in the freezer or pantry. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. It has a bidding feature, with new batches of stolen data being frequently added. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts.
Silk Road 20
Its 13,000+ users and 1,100+ vendors rely on a secure, fast-paced trading network. Alphabay reigns supreme with 60,000+ listings and $20M monthly trades, dominating 20% of darknet commerce via BTC and XMR. Incognito channels 20,000+ listings and $2.8M monthly trades through BTC and XMR, with a 5% market presence.
Archetyp Was One Of The Dark Web’s Biggest Drug Markets A Global Sting Has Shut It Down

In fact, similar anti-crawling techniques are still unseen in dark web markets. Since dark markets focus more on sales than forum-like discussions, we speculate that security mechanisms may be more stringent. In relation to this, we feel there is a real need to investigate these security mechanisms further, particularly regarding the protection of user accounts.
Visiting markets in Italy is a pleasure and, often, an authentic cultural experience. A lovely market in the charming and glitzy town nestled between mountains and coast. Forte dei Marmi is famous as the “fortress of marble” with its surrounding quarries being rumored to hold Michelangelo’s carrara marble, and as a glamorous Tuscan beach break.
Thanks to this, even if the market is closed, transactions can still be completed (as long as the buyer and vendors have another communication channel, which is usually a public dark web forum) if the items have been shipped. At the same time, when using this mechanism, the transaction funds do not need to go through the market’s wallet address. As the most widely used security mechanism in this sector, CAPTCHAs are ubiquitous on the dark web.
It shapes market interactions since buyers could punish the seller through an immaterial sanction that implicitly becomes material. Indeed, many empirical studies have confirmed Shapiro’s reputation theory 43, which states that a bad reputation negatively affects the price and number of sales of a product or service 20,44,45. In this context, the objective structure of social relations is partially shaped by comparing it to the previously described structure at the beginning of section two, in the absence of a reputation system. Reputation creates an incentive for cooperative behaviour and a disincentive for opportunistic behaviour.