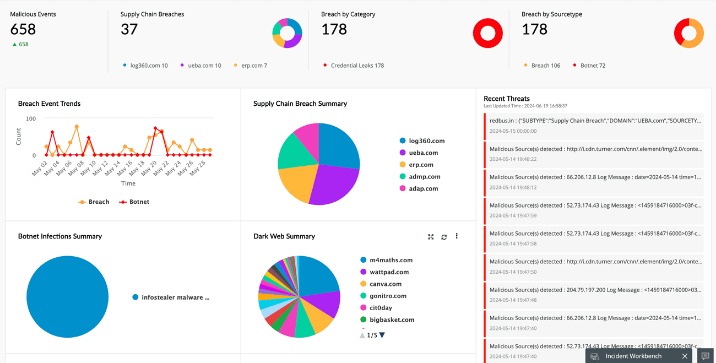
With visibility into the dark web exposure of suppliers and cybercriminals targeting your third parties. Our team uses Breachsense data to gain initial access during pen testing and red team engagements. When you first log into Bitdefender Central after activating your subscription, the service immediately starts mapping your digital footprint. After reading this guide, you will have a strong understanding of how data transactions on the Dark Web impact your privacy and security. Disgruntled employees or careless staff may intentionally or accidentally expose sensitive information by leaking it or mishandling data.
Why Prey Is The Ideal Solution For Organizations
Fortify your cybersecurity posture with thoroughly verified threat intelligence from hidden forums, marketplaces, and other dark web sources. Comprehensive threat detection ensures the discovery of compromised credentials, providing timely, accurate warnings and detailed reports. Consequently, it’s an ideal place for cybercriminals to go when they want to discuss, buy, sell or share the services, data and tools they use in cyberattacks. OWASP TorBot is a free dark web scanning tool written in Python, designed for crawling hidden websites with .onion addresses. Its features include retrieving page titles, addresses, and brief descriptions, saving crawl data to JSON files, crawling custom domains, and checking the live status of links. A research team investigating a data breach can use TorBot to efficiently gather and monitor relevant dark web pages, enhancing their ability to respond to threats effectively.
How To Effectively Showcase Your Linux Skills To Potential Employers ?
You will probably have your own preferred working practices that will lead you to one of these groups. The Network Traffic Analyzer is able to trace the source of incoming traffic and watch where outgoing traffic goes to. The service maintains a database of Tor network entry and exit points and keeps this list constantly updated.
You can add up to five email addresses and run an initial scan that searches deep to find any compromised information linked to the email address. Dashlane is a popular password manager, but it excels in basic password management functionalities and includes a unique dark web monitoring tool. It notifies users of any leaked passwords and encourages them to act immediately. It has a dedicated search bar where you can enter your email address or phone number to determine if it’s compromised in a data breach.
The indexed data is then analyzed and correlated to identify potential dark web threats, data breaches, or other relevant information. The dark web world is changing and adapting to modern cybersecurity tools, often overpowering the services that are supposed to protect us. With organizations facing cyber threats almost on daily basis, it is hard to keep up with modern dark web monitoring trends 2025 that are changing the cybersecurity world.
Respond To Threats Quicker
- Consider your use case, budget, integration needs, and data types you want to protect.
- Underground forums are established sites where reputed threat actors convene to discuss and transact the tools of their trade.
- Data breach tools are software solutions designed to detect and alert you to any unauthorized access to your sensitive information.
- He holds a bachelor of arts degree from the University of Washington and is now based in Boston, Massachusetts.
While web crawlers are a largely automated tool, a more manually-intensive – but highly illuminating – approach is attack group infiltration. Attackers don’t just publish complete attacks; there are entire forums and communities focused on discussing and planning ongoing ones. If your Gmail address is found on the dark web, you can set up 2-factor authentication to protect your account. Offer pros and cons are determined by our editorial team, based on independent research. The banks, lenders, and credit card companies are not responsible for any content posted on this site and do not endorse or guarantee any reviews.
Go From Reactive To Proactive With Dark Web Monitoring

A data breach occurs when cybercriminals successfully infiltrate a database and steal large volumes of sensitive or personal information. Dark web threat intelligence requires specialized tools for data scraping and natural language processing. Leveraging the right tools, enables you to automatically scan and analyze the huge amount of data involved.
Is Your Personal Data On The Dark Web? How To Find Out
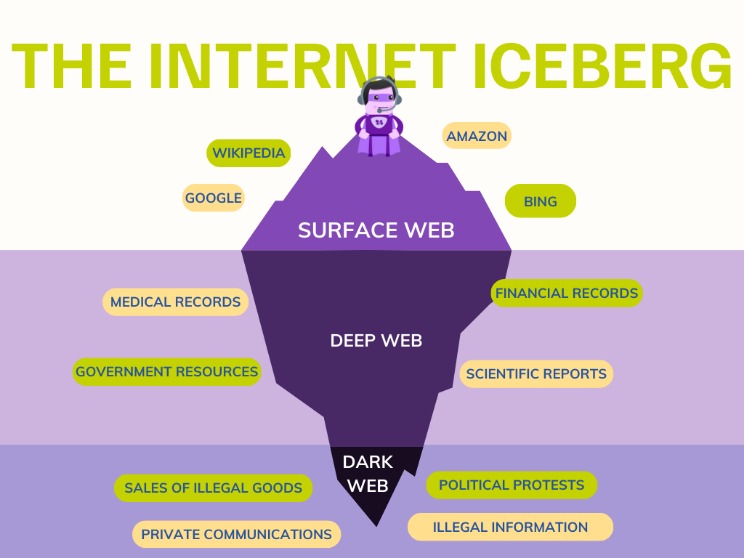
It’s intentionally hidden, accessible only through special software like Tor (The Onion Router). Tor gives people anonymity by bouncing their connection through a maze of servers worldwide to make it much harder to trace your identity. ShadowDragon offers a robust suite of investigative tools tailored to streamline the complexities of modern investigations. Their product lineup comprises OIMonitor, MalNet, and SocialNet, each serving a distinct investigative purpose.
Integrates With The Tools You Already Use
Unlike some open-source tools, which can be unstable and written in less robust languages, Lunar guarantees consistent data access. An uninterrupted flow of data ensures you can maintain a strong cybersecurity posture without worrying about gaps in monitoring. Standout features include a simple, user-friendly interface, smart filters and dynamic charts for efficient data analysis, plus an AI query builder to ease the effort of creating complicated search queries. In wrapping up, dark web monitoring enables organizations to navigate the complex terrain of digital threats with more confidence. By delving into the depths of the deep web and areas beyond the reach of standard search engines, a robust dark web monitoring solution becomes indispensable.
Does LifeLock Monitor 100% Of The Dark Web And Private Forums?
Dark web sites are anonymously hosted websites accessible only through special software—commonly “TOR” (The Onion Router). While the dark web has legitimate uses, it’s also a hotbed of illicit online marketplaces and other illegal activity. The dark web is a hidden part of the deep web that isn’t indexed by search engines. Because of the murky anonymity of the dark web, cybercriminals can surreptitiously buy and sell information illegally, like two people meeting in a dark alley to exchange cash for illegal goods. Cybercriminals sell personal information, credentials or asset access on the dark web.
The dark web is a hidden corner of the internet that isn’t indexed by traditional search engines. It’s where stolen data is traded, illegal activities take place, and digital identities are bought and sold every day. For businesses, government agencies, and individuals, this represents a major threat.
Ways Agentic AI Is Transforming Cybersecurity
- Flashpoint Ignite is our top pick for a Dark Web monitoring tool due to its comprehensive capabilities and user-friendly design.
- Learn how Lunar by Webz.io provides comprehensive, reliable coverage to keep your organization safe from hidden threats.
- Instead, a new suite of dark web monitoring capabilities has been established and developed by OSINT investigators.
- Lunar by Webz.io is a robust tool designed for dark web monitoring and threat intelligence.
- Once you spot identity theft, be sure to file an identity theft report with the Federal Trade Commission.
Yes—if your employees use email, passwords, or cloud-based tools, your business is at risk of credential exposure. Dark web monitoring gives you early warning before those credentials are weaponized in attacks. The solution’s AI-driven risk scoring system automatically prioritizes threats based on credibility assessments and potential impact on specific industries or organizations. Integration capabilities with major SIEM platforms and security orchestration tools make Recorded Future an excellent choice for enterprises with mature security operations centers.